FortiGate Web Filtering KB ID 0001787
Problem
In all honesty, enabling Web Filtering on your FortiGate really could not be simpler, you can simply enable it on your default users outbound policy, and select one of the three ‘pre-canned’ profiles, job done!
But most companies not only want to filter their web traffic they want to see who is getting blocked, and what are users trying to get access to. Most businesses now have ‘an acceptable use policy‘ for their IT, and if you don’t, get it sorted or when you want to sack “Creepy Dave” because he’s been frequenting ‘dodgy‘ websites you might be on a sticky wicket.
So before you even think about enabling Web Filtering you may want to roll out FSSO, so the firewall knows who everybody is, and what machines they are logged into.
FortiGate Web Filtering
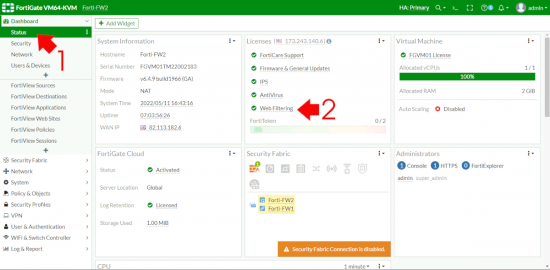
As with any Advanced Threat Protection product, you need to have a license for Web Filtering, let’s check that first > Dashboard > Status.
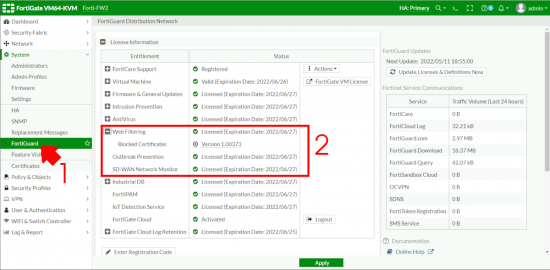
Then let’s make sure our definitions are up to date and the FortiGate is happy > System > FortiGuard > Web Filtering.
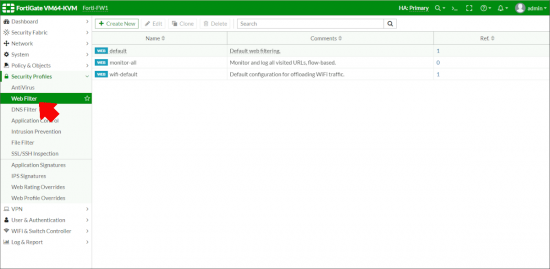
You can find the three ‘pre-canned‘ profiles under Security Profiles > Web Filter
Edit the policy, some of the things that are ‘allowed’, might raise an eyebrow, so block anything you consider to be inappropriate for your workplace.
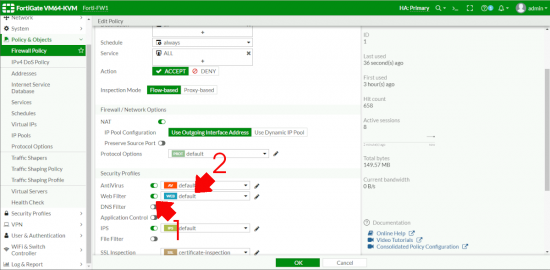
Then locate the policy object that your users are using to browse the web (under Policy & Objects > Firewall Policy) > Scroll down and enable Web Filtering > Select the correct Profile > OK > OK.
Note: If you are just rolling this out it might be worth using the Monitor All policy first for a while, just so you can get a handle on what your users are doing, and how much data there will be to trawl though.
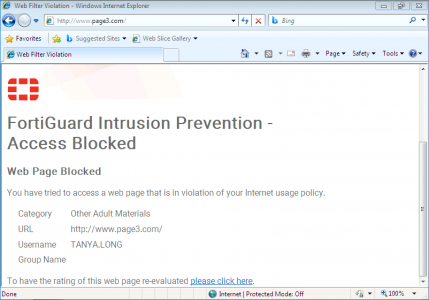
Then if your users attempt to go to a site that’s blocked, they will see something like the screen below.
Technical Tip: When testing Web filtering I use www.page3.com, (for my friends over the pond, in the 70’s, 80’s, and 90’s one of the UK “newspapers” used to have a scantily clad, (usually topless) lady on page 3. In modern society we frown on exploiting these girls, and making them multi millionaires now). However the domain still exists, and (if it were not blocked), it just redirects to the “newspapers” home page now. So if someone is looking over your shoulder they will not get an eyeful of nakedness (there’s a phrase I never though I’d be writing on PNL).
FortiGate Web Filtering: Whitelist a Blocked URL
The system is pretty robust, but you may sometimes want to allow a particular blocked URL, as you can see (above users can apply from the block page to have that URL unblocked if it’s been blocked in error. But what if you want to explicitly allow a URL thats getting blocked, (I had to do this a lot when I worked in the health sector for example).
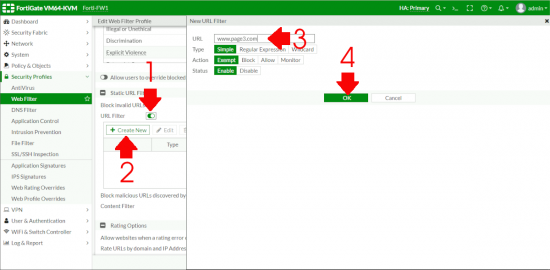
Go to the Profile thats applying the block > Edit > > Enable URL Filter > Create New > Type in the URL you want to unblock > Note: I’m selecting Exempt NOT Allow, (theres three hours I’ll never get back) > OK > OK.
FortiGate Web Filtering: Enable Password Override
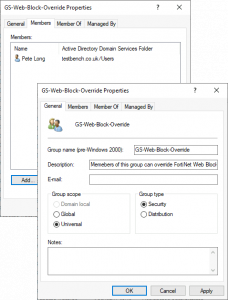
You can (if you wish create a group that can manually override the block screen (Note: It will still get logged). So here I’ve created a Domain Security Group.
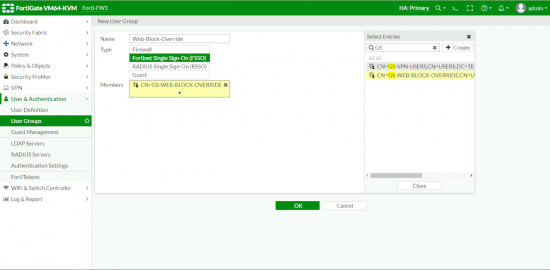
Then I can use FSSO, to enable that group on my FortiGate.
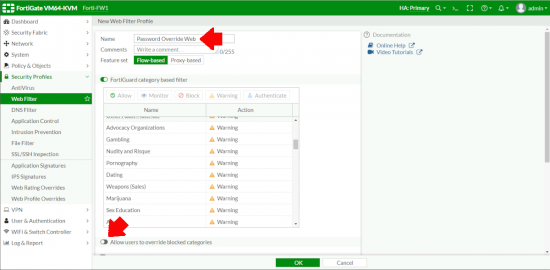
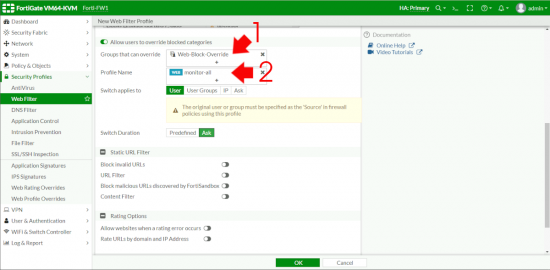
Create a new Profile > Give it a sensible name > Enable “Allow users to override blocked categories”.
Add in the FSSO Group you created above, then in the profile section select the profile you want to ‘Switch‘ them to, and select ‘Monitor-all” > OK.
Now create an outbound policy for web traffic > Add your FSSO users and ALL to the source, and make sure you enable the password override policy.
Note: Make sure this rule comes BEFORE your normal web traffic rule.
Now when those users are blocked, they get the option to “Proceed“.
FortiGate Web Filtering (Viewing User Activity)
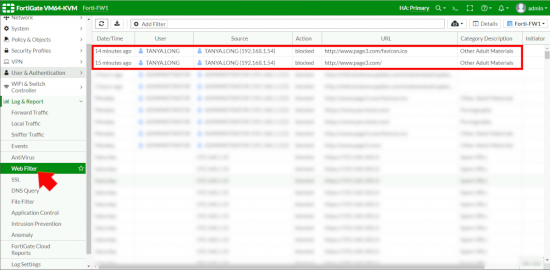
On my little test bench my firewalls are logging to FortiCloud. If you have FortiManager or FortiAnalizer then head in that direction for your reports, but for small deployments like this > Log & Report > Web Filter. Here you can see the block action that was taken above for example.
Related Articles, References, Credits, or External Links
FSSO FortiGate Single Sign On
FortiGate IPS (IDS)
Web Filtering Admin Guide