FSSO KB ID 0001786
If you are applying polices with your FortiGate, e.g. Web Filtering or IPS, then the ability to track actual users rather than IP addresses is advantageous, it’s all very well blocking access to adult material or gambling sites, from the corporate network, but most companies want to know WHO is attempting to connect to what and when.
To do that the firewall needs to learn what users are where, we can make all users actively authenticate to the firewall as they attempt to get on the web, but that does not make for a great user experience, it’s better to passively learn where your users are, and what machines they are using, then we can the use that in a policy. (let’s not get to far ahead for the moment).
Q. How do we learn where your users are, and what machines they are on?
A. FSSO
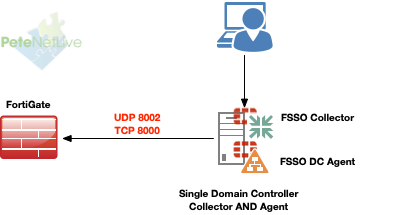
To enable FSSO you need to understand the difference between two pieces of software, the FSSO Collector, and FSSO DC Agent. The DC Agent (as the name implies) run on each of your DCs, it captures login events and then does DNS lookups to see what machines people are using. The Collector takes the output from one or more DC Agents and collates it for the firewall, it does not have to run on a domain controller (but it can).
I only have one server! Well thats OK, both the collector and agent can be on the same box
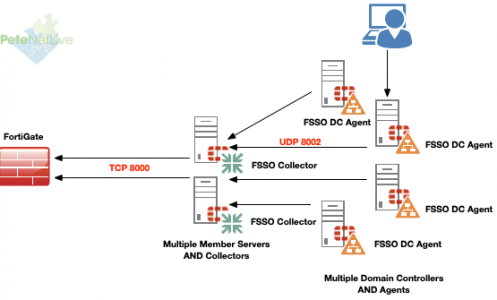
However most networks will have multiple Domain Controllers, so your FSSO topology may look a little more like this.
Or if you have an even larger network, you may want to build in a backup collector(s)
Deploy FSSO
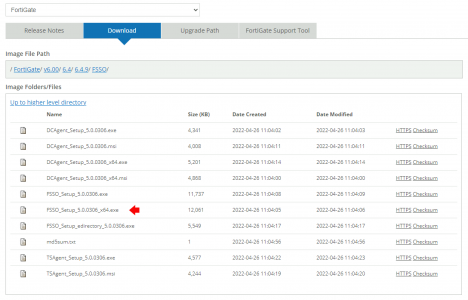
In my small test environment I’m going to put the collector and agent on a single DC. Your first challenge is actually getting the FSSO software. Log into your FortiCloud portal and proceed as if you want to download some FortiGate firmware.
Then in the version of FortiGate firmware that matches your firewall you will find an FSSO directory, (unless your’e in the dark ages your domain controllers will be x64 bit) so in my case I want FSSO_Setup5.0.0306_x64.exe (that will download the collector setup, that also includes the DC Agent software as well, which you can also download separately if you wish).
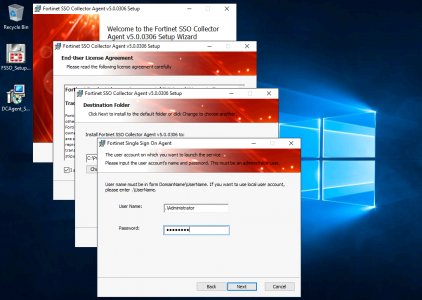
Install Collector
Accept the EULA, change the install directory if you don’t want it on the C: Drive > Enter some administrative credentials > Next.
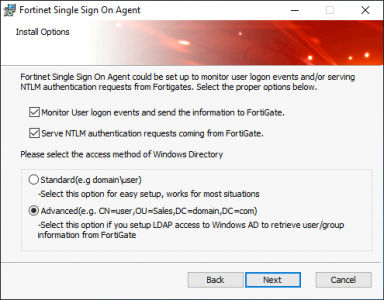
My FortiGate has LDAPS Lookups so I’m going for Advanced > Next.
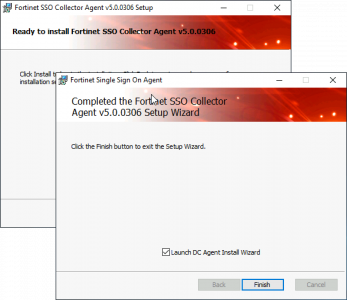
Install > When complete, Im installing the DC Agent on the same server so MAKE SURE ‘Launch DC Agent Install Wizard” IS ticked, and click finish.
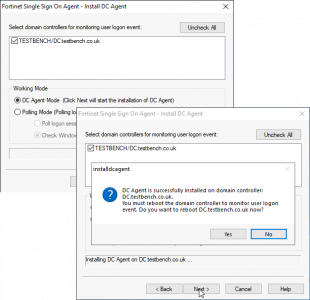
Warning: Installing a DC Agent will result in the reboot of this DC, (you might want to do the next step out of hours).
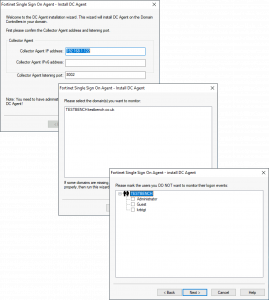
Install DC Agent
Accept the defaults > Next > Select the Domain > Next > Select any user(s) you want to be exempt > Next.
Select DC Agent Mode > Next > It will prompt for a reboot, let it do so.
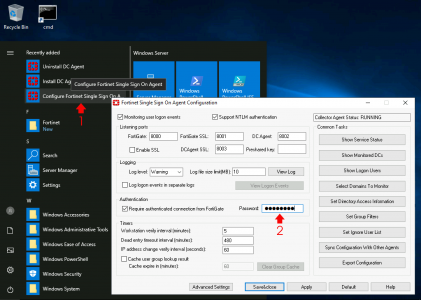
Post reboot launch FortiGate Single Sign On Agent Configuration > And change the password to something memorable, (you will need to enter this onto the FortiGate in a minute).
Register FSSO on FortiGate
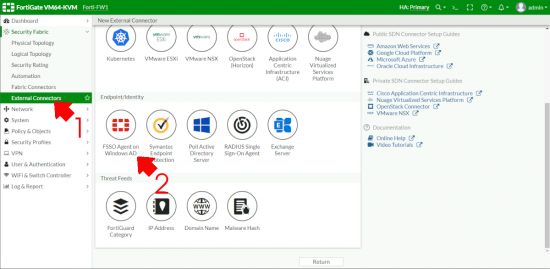
Back on the Fortigate > Security Fabric EXTERNAL Connectors > FSSO Agent on Windows AD.
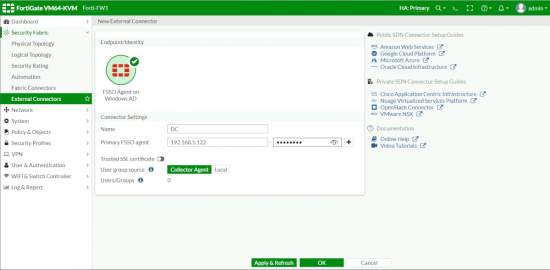
Give it a sensible name > Enter the IP address and the password you set above > Apply and Refresh > OK.
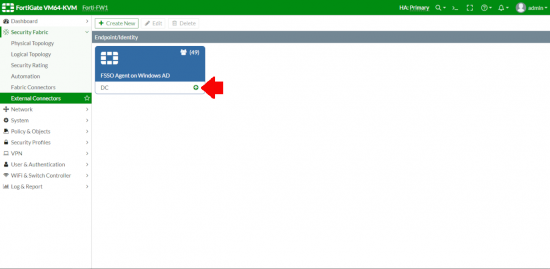
You will know it’s working because it will give you a free up arrow (it can take a little while, be patient).
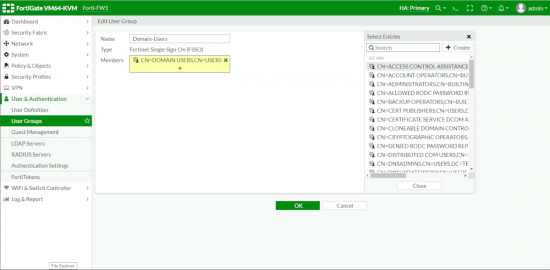
Create FSSO Groups
Now you can add GROUPs based on FSSO learned groups, like so.
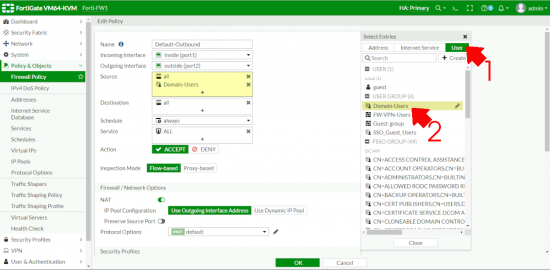
Once you have the FSSO groups defined, you can use them in policies. Below I’ve added Domain Users to my default outbound policy.
WARNING: If you have any devices, or assets that need access out you will need to add a new rule to alow them out explicitly before this rule, or their internet access will suddenly stop.
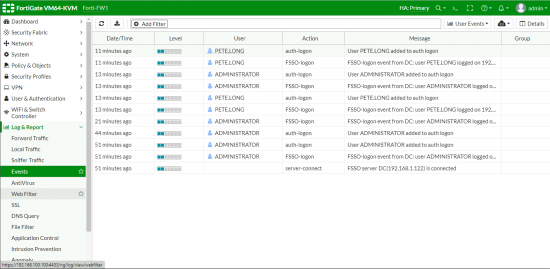
Monitor FSSO Events
To make sure the system is working you can go to Events > User Events > Make sure your user logon activity is getting logged.



02/06/2023
Awesome post, finally the documentation I was looking for !!
08/11/2023
Does this require any agent on the end user device at all
08/11/2023
No