KB ID 0001737
Problem
Working for a cloud service provider, (and a Duo partner). I get a lot of queries about Duo MFA for Office 365. Typically (I think) the best solution is to enable Azure Conditional Access and couple that with Trusted sites, so clients get challenged when out on the road, but not in the office. The drawback of this is Azure Conditional Access requires a P1 License, at time of writing that’s about $6 a month on top of you normal 365 licence. So it can work out expensive.
A couple of weeks ago, I was on a call with a client who wanted to use Duo Access Gateway to provide Duo MFA to their 365 tenancy. I’ve done the same thing for other clients with ADFS before, Basically you are just Federating a DAG into your Azure AD, rather than Federating an ADFS Server
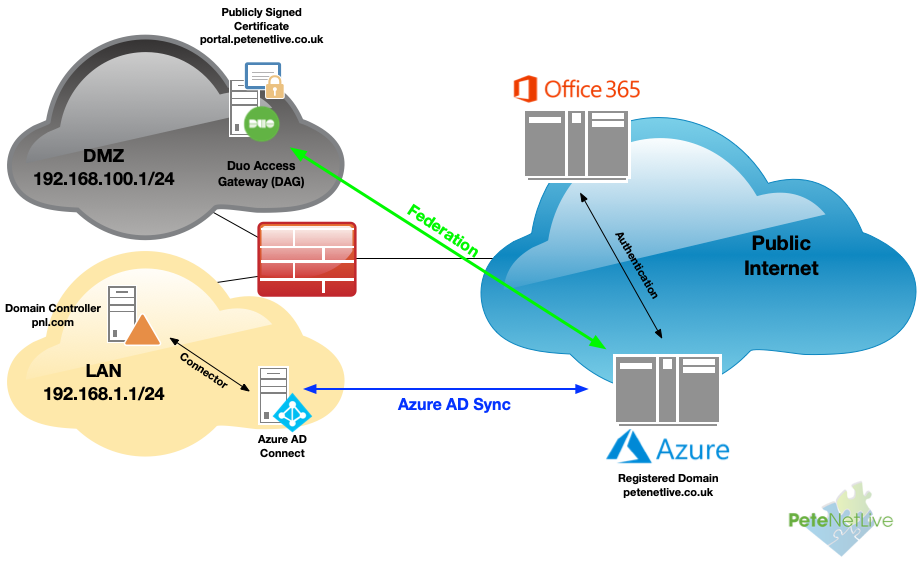
This is what it looks like;
Duo MFA: DAG & Office 365 Pre-Requisites
- Azure AD Sync needs to be setup, and a registered domain setup in your office 365 tenancy. (NOT the onmicrosoft domain!)
- You need (at least) Duo MFA licensing to deploy. One level above free ($30 for a year).
- DAG Server 2 x CPU, 4GB RAM, 60Gb HDD (Windows Server 2012 or newer (2019 supported) Note: You can also deploy DAG on Linux.
- DAG Server should be in a DMZ, (not domain joined).
- DAG Server needs IIS role installing.
- DAG Server needs TCP Port 443 open (outbound) to Duo.
- DAG Server needs TCP Port 443 open (Inbound) to Duo on the public IP address that your public DNS record is pointing to.
- Download PHP (in Zip file format) Keep the Zip file handy.
- Install a publicly signed SSL certificate (Common name or SAN must match the public DNS name).
Note: Duo have great walkthroughs and videos on their site, this article is just to tie the various steps together.
Installing Duo MFA DAG
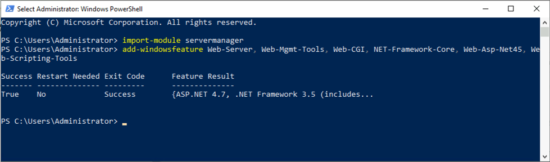
To setup IIS just use the following Powershell commands
import-module servermanager add-windowsfeature Web-Server, Web-Mgmt-Tools, Web-CGI, NET-Framework-Core, Web-Asp-Net45, Web-Scripting-Tools
Install and Bind a Publicly Signed Certificate: Let’s do this for free with Let’s Encrypt! See the following article.
Free Certificate for IIS with Let’s Encrypt
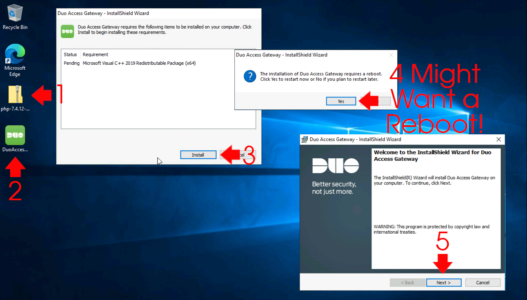
Download the newest version of PHP in zip format. and drop it on your desktop, then run the Duo Windows installer. You may be prompted to install the C++Runtime software (which may require a reboot). Post reboot the installer will launch.
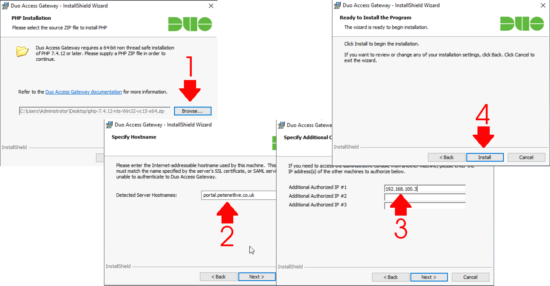
Browse to and select the PHP Zip file > Next > Select the correct server hostname (if it’s not listed, then you need to enter it in the ‘hostname’ section of the https binding in IIS manager > Next > If you want to manage the DAG from any other IP addresses enter them > Next > Install.
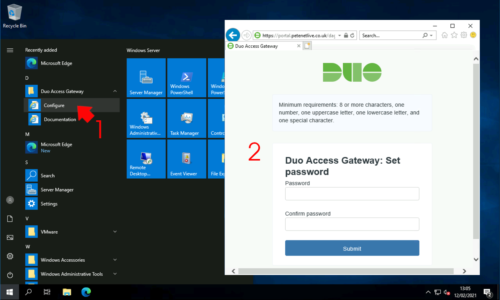
When done launch the ‘Configure’ page > Create an access password > Submit.
Configure Duo DAG Active Directory LDAPS Access
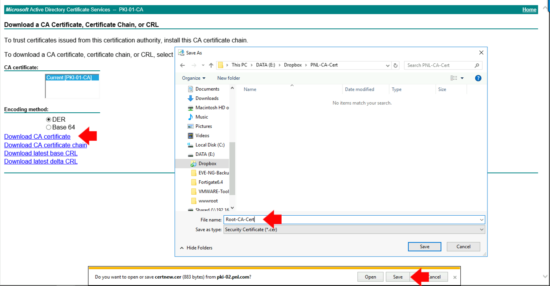
In the next step we need a copy of your CA Certificate (the CA that issued your domain controller(s) kerberos certificates). If you have just glazed over have a read of the following article;
Get Ready for LDAPS Channel Binding
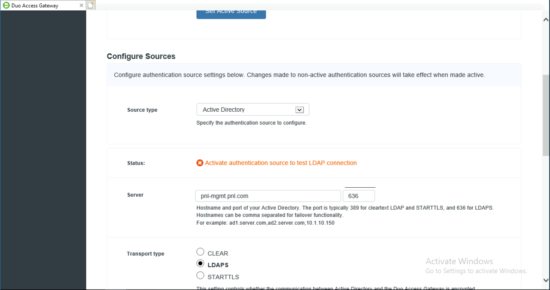
From the DAG console > Authentication Source > Configure Sources > Select Active Directory* > Enter the FQDN of a domain controller, (the DMZ server needs to be able to resolve this I suggest putting it in the server hosts file). > Port will be 636 (LDAPS) > Select LDAPS > Scroll down.
*You cant use Azure as a authentication source for Office365 MFA, (counter intuitively!)
Browse to and select the CA certificate you downloaded above > Set the attributes to “mail,sAMAccountName,userPrincipalName,objectGUID” > Search Base (I’m setting it to the top of my active directory e.g. ‘DC=pnl,DC=com’ > Search Attributes (I’ve set the same as the attributes above) > Search Username, set to a normal domain user account, (I’ve set-up a service account that’s just a member of ‘domain users’ > Scroll down > Type in the users password > Save Settings.
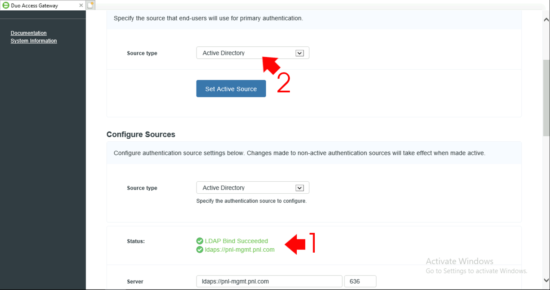
What should happen is, it should say LDAP Bind Successful, if it does not;
- Make sure TCP Port 636 is open from the DMZ server to the Domain Controller(s)
- Make sure you used the domain controller FQDN NOT its IP address, (the IP address is NOT on the Kerberos certificate).
- Install the Remote Server Admin tools for ADDS – this will give you access to LDP exe which you can test LDAPS connectivity with (I’ve written about LDP before, use the search box above).
When happy, ensure Active Directory is set as the Active Source.
Federate Duo DAG With Azure Active Directory
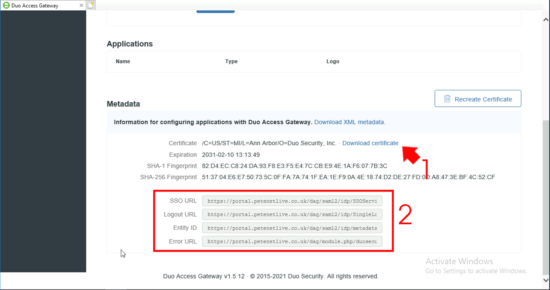
Within the Duo DAG management console > Applications > Metadata > Download the Certificate > Copy all the URLS to a notepad file.
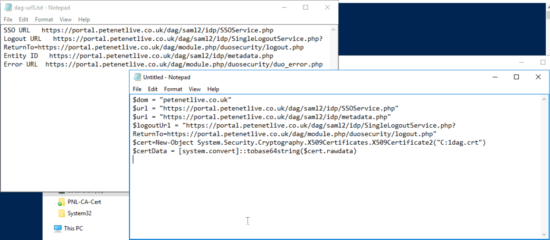
Copy the notepad file, and the certificate, to a domain joined server/PC that has the the Azure Active Directory Module for Powershell installed.
Execute the following commands, (change the values in RED to match your own);
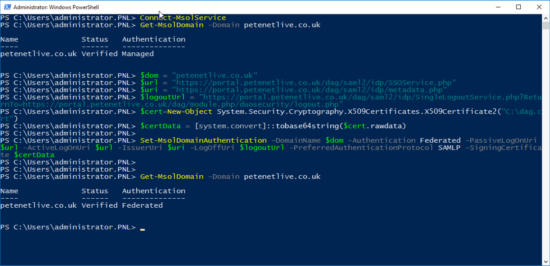
Connect-MsolService Log into your Tenancy, when prompted get-msoldomain -domain your-domain-name.com Make sure it says 'Managed' and NOT 'Federated'! $dom = "your-domain-name.com" $url = "https://portal.petenetlive.co.uk/dag/saml2/idp/SSOService.php" $uri = "https://portal.petenetlive.co.uk/dag/saml2/idp/metadata.php" $logoutUrl = "https://portal.petenetlive.co.uk/dag/saml2/idp/SingleLogoutService.php?ReturnTo=https://portal.petenetlive.co.uk/dag/module.php/duosecurity/logout.php" $cert=New-Object System.Security.Cryptography.X509Certificates.X509Certificate2("C:\dag.crt") $certData = [system.convert]::tobase64string($cert.rawdata) Set-MsolDomainAuthentication –DomainName $dom -Authentication Federated -PassiveLogOnUri $url -ActiveLogOnUri $url -IssuerUri $uri -LogOffUri $logoutUrl -PreferredAuthenticationProtocol SAMLP -SigningCertificate $certData get-msoldomain -domain your-domain-name.com NOW it should say 'Federated'!
Duo MFA Protect Office 365
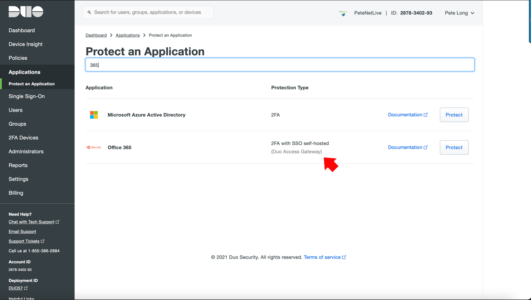
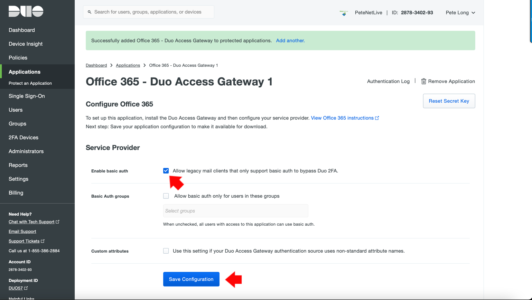
Log into your Duo online admin console > Protect an application > Locate Office 365 (2FA with SSO self hosted) > Protect.
Unless ALL your mail clients* support modern authentication then tick “Allow legacy mail clients that only support basic auth to bypass 2FA”
*Modern Authentication Supported on: Outlook 2013 (or newer), older Android mail clients don’t, though on modern versions of Android that you can install MS Outlook on does. Modern Apple IOS devices support modern authentication.
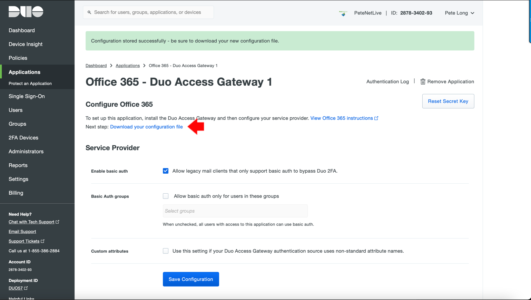
Click ‘Save Configuration‘.
Click “Download your Configuration File” this will download a JSON configuration file, put it somewhere your Duo DAG server can get to.
Add Office 365 MFS to Duo DAG
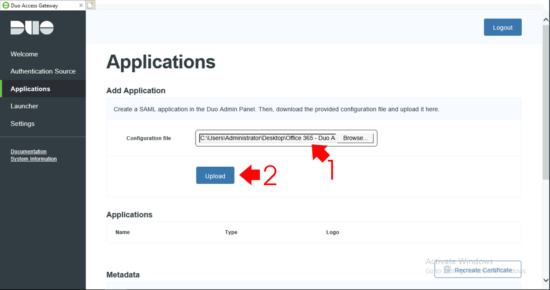
Back on the DAG server > Applications > Browse > Select the JSON file you downloaded above.
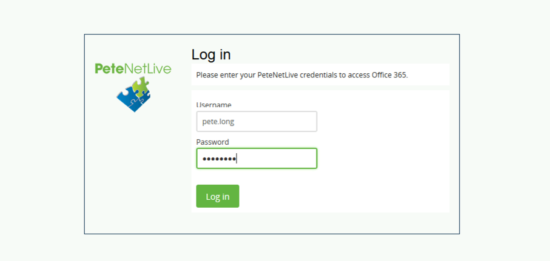
Open a web page, and try to log into office 365, after you’ve entered your username, you should be forwarded to your DAG for 2FA
Related Articles, References, Credits, or External Links
NA


02/02/2022
This is amazing. I did have a question about the DAG licensing. Today DUO licensing requires DUO Beyond to utilize the DAG. Does that mean you only need one DUO Beyond license to install it?
02/02/2022
Spot on yes, I think that’s what I did to write the article, then I cancelled it a couple of months later.
P
23/03/2022
Duo Network Gateway (DNG) requires Duo Beyond. DNG allows access to on-prem web apps, SSH, and RDP without the need to be on VPN.
Duo Access Gateway (DAG) and its replacement Duo Hosted SSO are included in all paying editions of Duo (MFA, Access, and Beyond)
27/03/2022
Just wanted to point out that Duo Access Gateway will be end of life Oct 2023. No new DAG’s can be created after May 2022.
https://help.duo.com/s/article/7486?language=en_US