KB ID 0001682
Problem
In this article I will focus on ‘Remote Access’ VPN, which for Cisco FTD means using the AnyConnect client. Ive spent years deploying this solution for ASA so it’s a product I know well. As with all things Cisco, there are a couple of things that could trip you up. Let’s get them out of the way first.
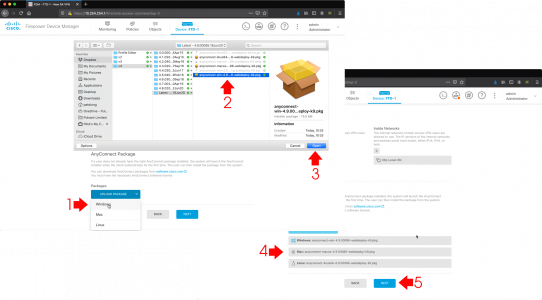
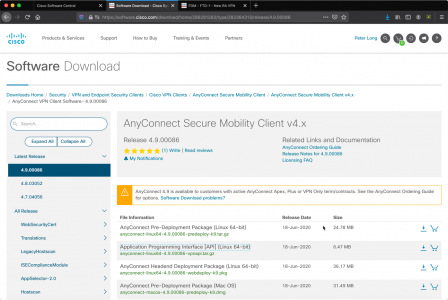
If you are used to AnyConnect then you probably have the client software. It’s the same software package that’s installed with Cisco ASA. Sometimes just getting access to the download is a trial! Anyway you will need the AnyConnect ‘Package’ files, these typically have a .pkg extension, (Cisco refer to these as Head-End packages). Theres one for macOS, one for Windows, (well another one now for ARM processors, but I’ve not needed it yet), and one for Linux. You will need to download a package for each platform your users will need to connect with.
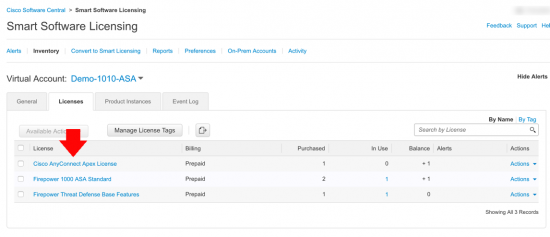
AnyConnect Licence! After years of getting a few free with a Cisco ASA, I was unhappy to find that’s not the case with Cisco FTD. If you want to use AnyConnect you need to have a licence, and it needs to be in your Smart Licensing Account, (before you enable Remote Access VPN).
Final Gotcha! Make sure you HAVE NOT enabled HTTPS management on the outside interface of the FTD before you start configuring AnyConnect, or you will get all the way to the end, and it will fall over and you will have to start again (thanks Cisco! How hard would it be to say, if you enable this, I will disable https outside management is this OK?)
Solution
If you haven’t already done so enable the Remote Access VPN licence > Smart Licence > Fire Configuration > RA VPN License > Enable > Change to licence type (mines Apex). Have a coffee and recheck everything is licensed OK.
AnyConnect 4 – Plus and Apex Licensing Explained
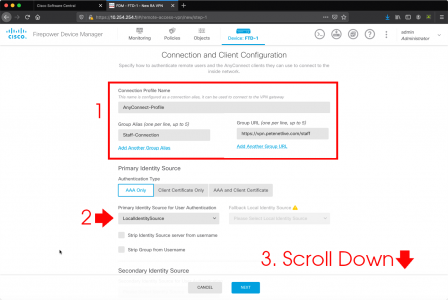
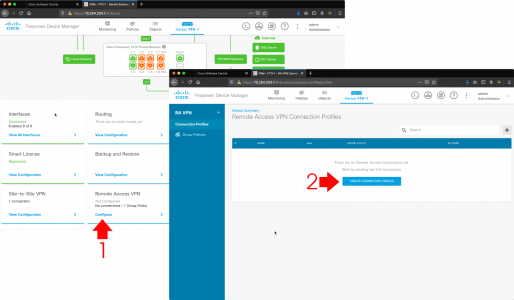
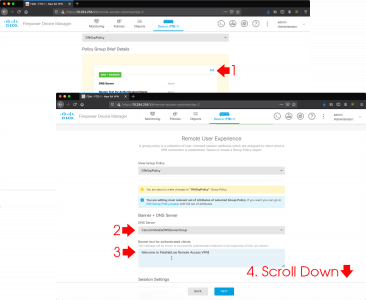
Remote Access VPN > Configure > Create Connection Profile.
Give the profile a name, a group alias, and group URL > I’m using the FTD as my AAA Identity source (so my username and passwords are held on the firewall) that’s fine for small deployments, but in production you should think about deploying an AAA solution (called a Special Identities Realm in FTD). Scroll down.
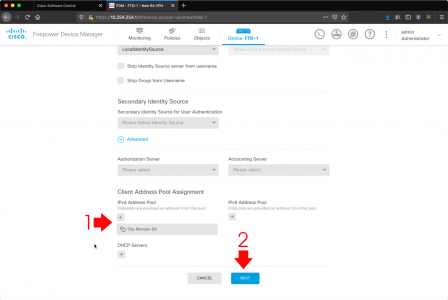
I typically create a new network object for my remote clients to use, you can select your internal DHCP server to send out addresses if you wish > Next.
I’m using Cisco Umbrella DNS servers, (or the DNS servers formally known as OpenDNS) > I’m setting a ‘welcome banner’ but you dont need to, (some people find them annoying!) > Scroll down.
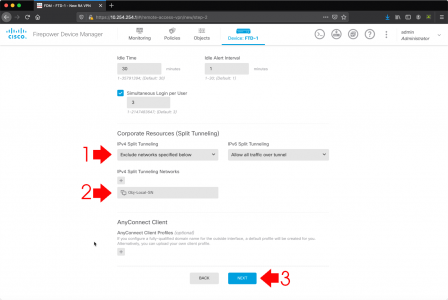
Split tunnelling: As always Cisco assume you want to tunnel everything, in most cases that’s NOT the requirement (BUT it IS the most secure!) I setup split tunnelling by Excluding my internal networks > Next.
Client Profiles: If you have one you can set it here, if you want to create one, see the following article;
Cisco FTD (and ASA) Creating AnyConnect Profiles
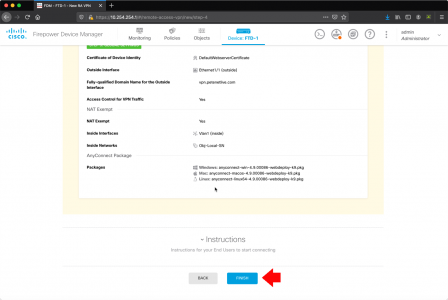
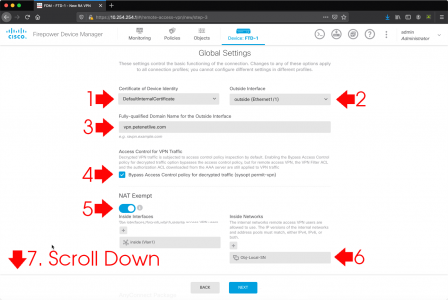
Select the certificate the FTD will present (don’t choose the web one it will error!) > Select the interface your client will connect to (typically outside) > Enter the FQDN of the device > I allow bypass for VPN traffic, if you want to scan remote traffic with firepower etc DON’T select this > Enable NAT Exemption (select the internal interface) > Internal Networks: Then add in the internal network, I’ve already got an object for that, (you may need to create one.) > Scroll down.
Here you upload your .pkg files (I mentioned above) when you have finished > Next.
Review the settings > Finish.
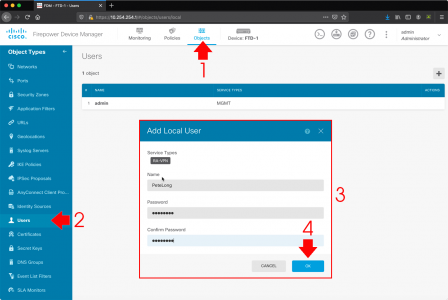
Cisco FTD Create User (via FDM)
You will need a username and password to authenticate (skip this as you are not using the FTD’s internal user database.) Objects > Users > Add > Supply a username and password > OK
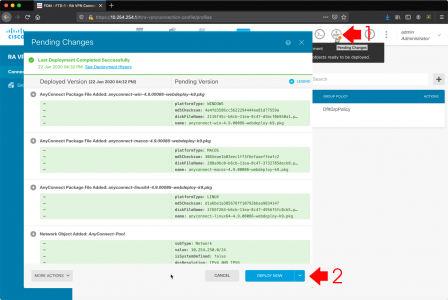
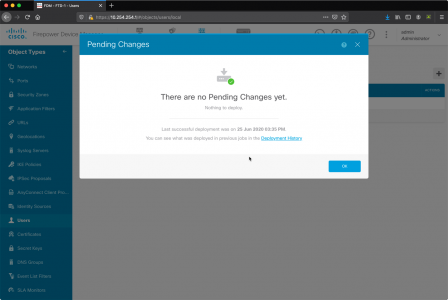
Pending Changes > Deploy Now.
Go and have a coffee again, keep clicking pending changes until it looks like this. (Quite why it takes so long, I have no idea?) It’s even more fun, if you made a mistake, because it will just error and fall over, so you have to find the error (if you can) > then remove the pending change and start all over again. Cheers Cisco!
Finally go to an external client and give it a try, if your clients don’t have the client software installed simply ‘browse’ to the FTD to get it.
Related Articles, References, Credits, or External Links
Cisco Firepower 1010 Configuration




10/01/2021
Thank you very much
03/02/2021
Hi,
Thank you for the tutorial. It helped me reach the point that I can connect to my vpn (firepower 1010 fdm) from the internet. But I am isolated to the vpn network 10.1.11.x in this case. If I wanted to reach the core network 10.1.10.x, how would I do that? Or can you point me to a tutorial or wiki. Thank you
05/02/2021
Summarise the network on the VPN settings https://www.petenetlive.com/KB/Article/0001138
16/04/2021
Thank you Pete very good tutorial, i just bought a Firepower 1010 for the company that i work do you know how much the anyconnect license cost?
19/04/2021
Depends how many you want, and if you want perpetual/subscription or plus/Apex licenses https://www.petenetlive.com/kb/article/0001013
04/09/2021
Hi Pete,
Thanks for the great tutorial – I’m fan of Your posts. There is one more “gotcha” in the configuration – our users are authenticating against the Microsft NPS server (RADIUS) and so we were able to add such identity source. But there is no option in the FDM (I spent last 4 hours searching for it) to enable secure protocol such as MS-CHAPv2. According to our syslog (no matter what we do) the FDM is always trying to send “PAP” requests to the NPS server. I was also trying to find answer to that in Cisco documentation but it seems that such feature is simply unavailable. Perhaps there is some trick to enable MS-CHAPv2 in the identity source.
21/09/2021
Not that I know of but I’ll throw it open….
01/12/2021
If you enable tick the ‘enable password management’ box in the vpn profile, it turns on ms-chapv2.
I wholeheartedly think the tick box should be called ‘enable mschapv2’ but there you go. Seems to be a hangover from the ASA which had the same box.
Sorry just to clarify:
RA VPN profile> AAA > advanced settings > enable password managemnt.
25/07/2022
@richard stevens, can You explain how You get to this settings in FTD?
In My FTD 7.0.1 there are no settings or AAA in RA VPN configuration. I saw this in ASA but this post is about FTD.
16/08/2022
@Damian
Here are the steps to get to the ms-chapv2 setting you need.
From the Firepower Management Center portal…
1. Select “Devices” from the navigation menu.
2. Select “Remote Access” under the VPN section in the “Devices” menu.
3. In the “Connection Profile” screen, select the pencil icon to edit the connection profile that you wish to enable the ms-chapv2 on.
4. In the “Edit Connection Profile” page, select the “AAA” section.
5. At the bottom of the “AAA” configuration section, select / expand the “Advanced Settings” section.
6. Tick the box for “Enable Password Management” setting and select the appropriation option selection.
7. Click the “Save” button to commit the profile changes.
22/08/2022
Thanks Mark, in my case, i had to upgrade Firmware to 7.2. After update finished, this option was available in VPN RA setttings.
15/09/2022
Is it possible to remove the group drop down in case you have more profiles ?