KB ID 0001678
If you’re here you’ve either purchased a new Cisco Firepower device running FTD (FirePower Threat Defence) or have re-imaged your Firepower device from ASA to FTD code.
On its factory defaults, the unit will have the following settings.
- Inside IP address (VLAN 1) 192.168.1.1 (on all interfaces from 2 to 8).
- Outside IP Address set to DHCP in interface 1.
- Management IP address 192.168.45.1 on the Management Interface.
- DHCP Scopes on both the inside and management interfaces (192.168.1.x and 192.168.45.x respectively).
- Power Connector.
- 8 x Gigabit Ethernet ports: Normally GigabitEthernet 1/1 will be for the WAN, GigabitEthernet 1/2 though 1/8 will be for the LAN (with 1/7 and 1/8 being PoE).
- Management Port.
- Console Port (RJ45).
- Console Port (Mini USB).
- USB Port (useful for upgrades, and backups).
- Kensington Lock: Seriously? I’ve not seen one of these since about 2005, does anyone still use them?
- Reset Button: Depress for 3 seconds reverts the firewall to its factory settings, (and preserves the config apparently).
- Status Lights, (another reason not to put things on top of it!) Though you will notice there’s some on the back also. Note: When all lights are solid the firewall is operational, when the centre light is blinking, it’s still booting).
FirePower 1010 Setup
I will be deploying this as a stand alone FTD firewall, that will be managed locally on the device itself via FDM (Firepower Device Manager) and not via an FMC (Firepower Management Center) appliance.
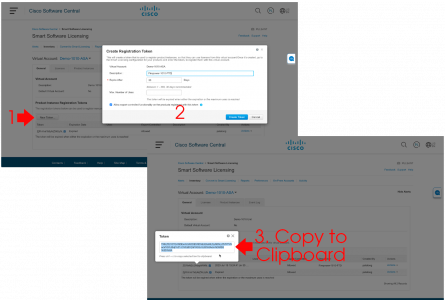
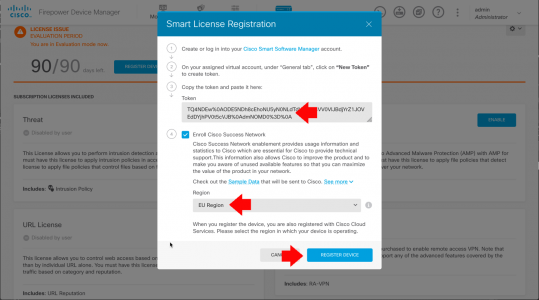
Smart Licensing: If you’re not already familiar with Cisco Smart Licensing, I’ve covered it in more depth here. Set yourself up a free Smart License Account, and generate a token, copy it to the clipboard, (we will need it in a minute).
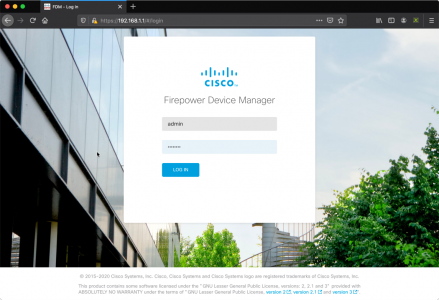
Connect to the firewall via a LAN port on https://192.168.1.1, or via the Management port on https://192.168.45.1 (unless you have ran though the FTD setup at command line, and have already changed the management IP).
Default usernames, (you will be asked to change them) are;
- Username: admin
- Password: Admin 123
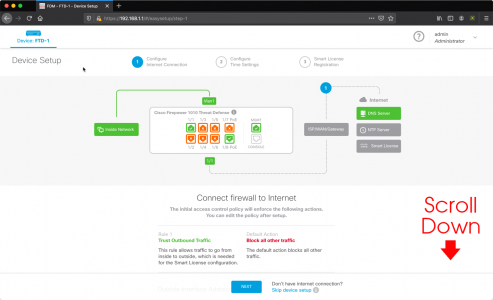
Scroll down.
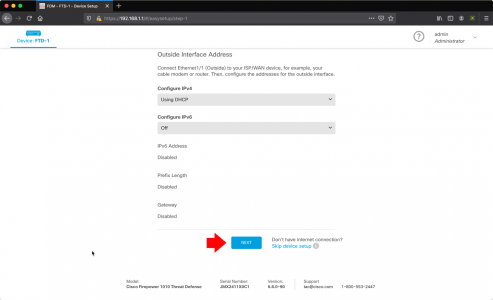
Here I’m accepting the default Outside/Public Interface settings of DHCP enabled, with IPv6 disabled, if yours has a static IP, or you want to user IPv6 then change the settings accordingly > Next.
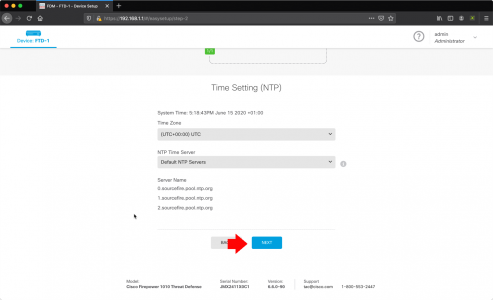
I’ll accept the defaults here, be advised those NTP servers may take a little while to ‘go-green’ (you will see what I mean later) > Next.
I’m going to do this manually in a minute, so we can skip this > Next.
Note: The unit will have a default policy of let everything out (sourced from inside), and nothing in (sourced from outside) we will leave that as it is, as a decent start point.
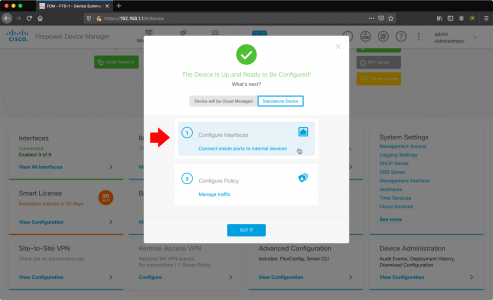
Stanalone device > Configure Interfaces.
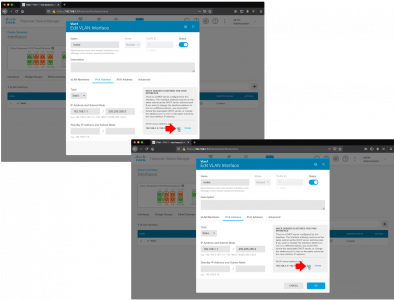
Note: Below I’m going to REMOVE the DHCP Scope, then change the ‘inside’ IP address (to avoid errors). Then later I will add the new DHCP scope back in again.
VLANs > Vlan1 > Edit. > DHCP section > Edit > Remove.
You can now set the inside IP address accordingly. (Don’t panic you wont lose connectivity yet!) > OK.
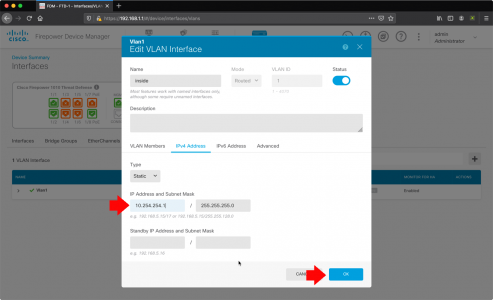
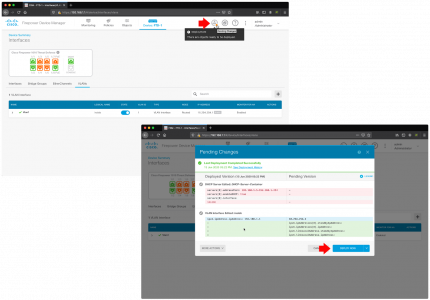
Now you need to Save/Commit the changes, and Deploy them. Now you will lose connectivity, if you have changed the inside IP address, so manually give yourself an IP address on the new network, and reconnect to the firewall.
Note: Update: Pleas ensure tha management is allowed in VLAN1 before proceeding (System Settings -> Management Access -> Data Interfaces.)
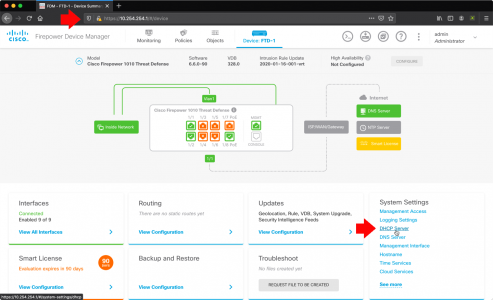
Cisco Firepower Setup DHCP
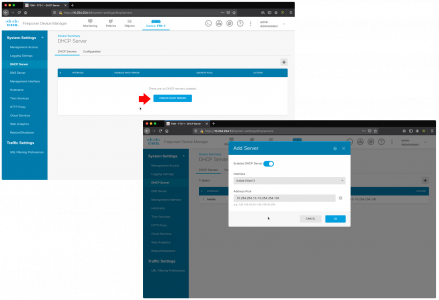
Create a new DHCP Scope: Should you require the firewall to be a DHCP server, log back in to the new internal IP address > System Settings > DHCP Server.
Create DHCP Server > Enable DHCP Server > Enter the new scope > OK.
Remember to commit the changes, and deploy them again!
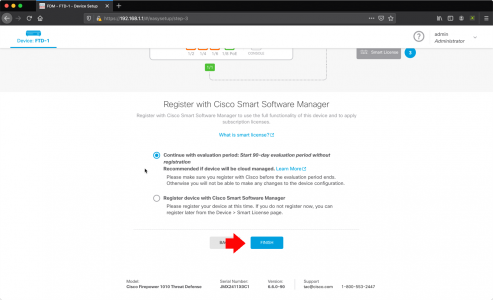
Cisco Firepower FTD Licensing
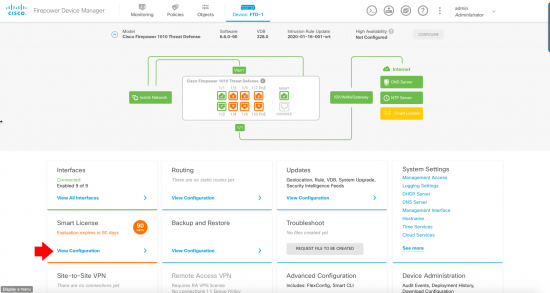
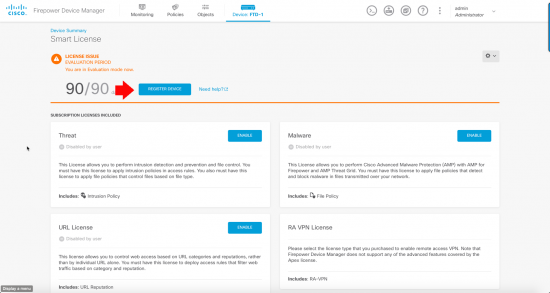
Thankfully this is MUCH easier than doing the same thing while running ASA Code (on the same hardware!) > Smart Licence > View Configuration.
Register Device.
Paste in your token, (from above) > Set your location > Register Device. Go and have a coffee, it will look like it’s broken/not worked for a few minutes.
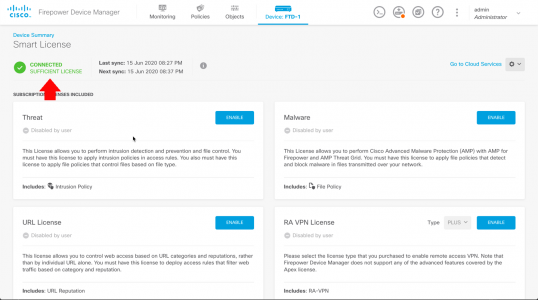
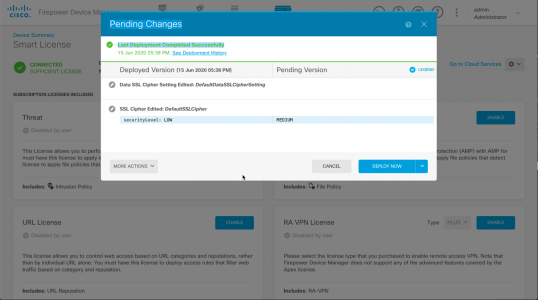
After a while you should see this;
There will be some outstanding changes to save and deploy also, now the unit is registered.
Back in the Cisco Smart Licence portal, it should look a bit like this;
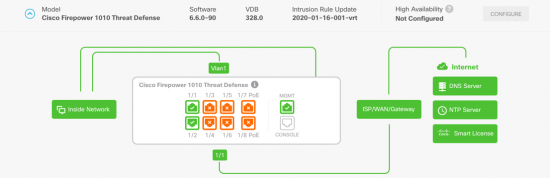
Once fully complete and operational, all connected interfaces should have all the options ‘go-green’. For me the NTP servers took a while!
Note: Obviously the interfaces in orange are not in use!
Related Articles, References, Credits, or External Links
NA



17/06/2020
Pete,
I’ve been through this setup twice now; before you set anything up upgrade to the newest OS level you want to be at. I’ve set all of this up only to find out that the OS that comes with it is full of bugs and worse; the upgrades fail. This makes you fall back to a image rebuild in rommon.
17/09/2020
Hmmm, I have a 5525-x with a FirePover module.
And so I’m wondering whether to reimage the FTD 6.6x?
Does FTd still have a lot of bugs? Is it better to stay on ASA os + Firepower on my firewall?
17/09/2020
Don’t do it, it’s awful, you will get stressed and reinstall the old OS again!
30/09/2020
I’m in the same boat. I have a 5525X with the sfr module and was planning to replace with a 1140 runnig FTD using vFMC to manage multiple devices. Big draw is to connect everything to Threat Response & SecureX which you need FTD to integrate directly. However, I installed a 1010 with FTD and found it to be a learning curve (especially after the CLDAP reflection attack). The consolidated codebase is not what it’s crack up to be. Although I do like having to only do 1 update and the faster deployment push from the FMC. I can see configuring the newer 1000/2000 series will be a pain for sites that only have internet connection.
01/10/2020
We are still considering dropping all ASA/FPR rollouts, (with the exception of ASAv) Where I work. I just cant justify fighting Cisco’s corner any more. And My CTO is a Fortinet Champion, so the writing is on the wall for us.
29/01/2021
Hello
Is it possible to connect on each interface diffrent VLAN ? and do manage dhcp relay ?
Example VLAN 1 on the interface 1, Vlan 2 on the interface 2.
On the VLAN 1 is the DHCP and VLAN 2 can request to VLAN 1 an adresse IP to the DHCP.
And have VLAN 1 and 2 going out to internet but not communicated to each other, just for the DHCP
Thanks for the clarification
01/02/2021
With ASA code it should be possible https://www.petenetlive.com/KB/Article/0001501 with FTD code I’m not sure.
30/03/2021
i used asa 5510 and my company is bought firepower 1120 threat defence. i have problems, how i configure options like: creating VLAN-s, set security level on interface. i use Firepower device manager. i must some other option for configuring because those options does not exist in device manager
30/03/2021
Speak to Cisco – get the ASA Code and re-image it with ASA Code.
24/06/2021
I have installed a 1010 with FTD at a remote site. I am managing it via the outside interface (from defined IP addresses). It works OK for a couple of months and then for some reason I can’t login or even ping the interface. This problem can only be resolved by a reboot, which is not convenient for such a remote site. Do you have any advice, please?
11/10/2021
Just got my first 1010 (ASA) as a test run to replaces some asa 5506’s that also use the Firepower module. Having lots of fun with licensing already…
Can the 1010 ASA run ASA & also the firepower module like the 5506, or is do you have to go full FTD to get access to the firepower stuff? – we currently just use the module for geo-blocking and don’t really want to go full FTD. I notice none of the session sfr stuff works any more.
12/10/2021
ASA on Firepower models is ASA only no Firepower features.
01/03/2022
If I have only Firepower 1000 ASA Standard available on my smart account. Can I register the FTD into my smart account? Or do I need to get Firepower Threat Defense base first? As I bought FPR1010 without any subscriptions and still want to FTD.
01/03/2022
Depends where/how you bought it! Typically you only Get the license version for the SKU you purchased, (unless you speak very nicely to Cisco TAC).
01/03/2022
As I have gone through your great articles and didn’t find the step that you add Firepower Threat Defense base on your smart account. So, I assume that Firepower Threat Defense base license automatically appears after you registered again once you finished reimage from ASA to FTD.
01/03/2022
The reseller you buy the device from, will transfer the licence (ASA or FTD – depending on what you bought) from their HOLDING account at Cisco to YOUR Smart Licence account.
From that point you simply need to associate it with the device once you have generated the key and imported the device into you smart account.
16/03/2022
how can i configure port forwarding for 3 different servers for public access behind fpr?
17/03/2022
If you have only one public IP – then you would need to forward three different ports? (typically you will need 80/443 for a web server?) If you have multiple Web servers weach should have its own public IP, and you will need to a one-to-one static NAT.