KB ID 0001651
Problem
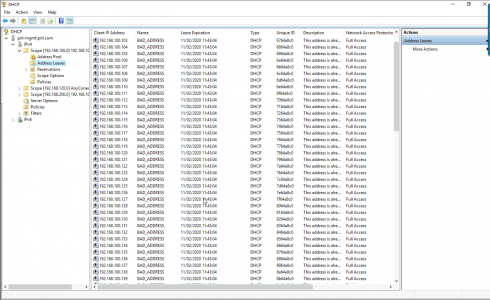
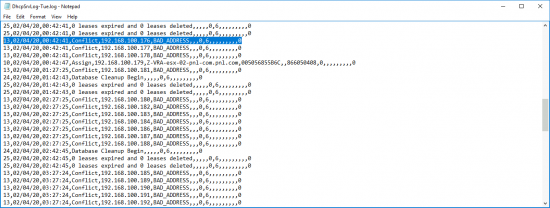
I had a client machine struggling to get an DHCP address, and when I looked in DHCP the scope it was full of this;
BAD_ADDRESS This address Is Already in Use
Solution
A tour of Google and forums is full of posts by people with this problem, and other than, ‘Oh I looked in the logs and fixed it’ (with no mention of what log, or where this log was), or ‘Yeah I used Wireshark and located a problem client‘, then no follow up on what they did, or scanned for. So I pretty much had to slog through and work it out for myself. I’ll detail each step I took below, most of which didn’t help, or sent me in the wrong direction, but for you that may be a better solution.
And I will give you enough information to at least be helpful!
Firstly Common Sense Check: If this has just happened what have you changed? Have you added any Wireless Controllers, or Access Points? Have you deployed any new Switches or Firewalls. In my case, it was my test network so it could have been happening for months!
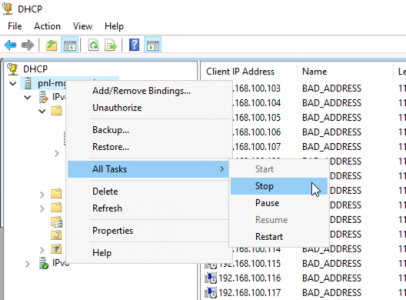
The most frequent cause of this error is simply because someone has setup another DHCP server on the network. That will be easy to diagnose, simply ‘Stop’ your DHCP Server;
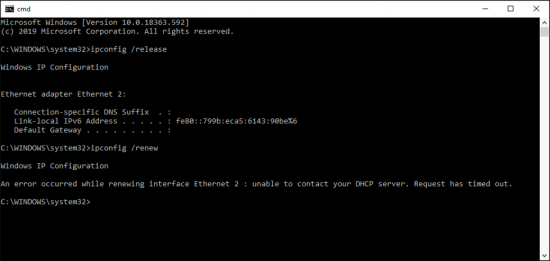
Then on a DHCP client, issue an ifconfig /release and ifconfig /renew, If it gets an IP address, issue an ifconfig /all and look for the IP of the DHCP server it’s using, that’s your culprit. However as you can see, mine didn’t get an IP address so this wasn’t my problem.
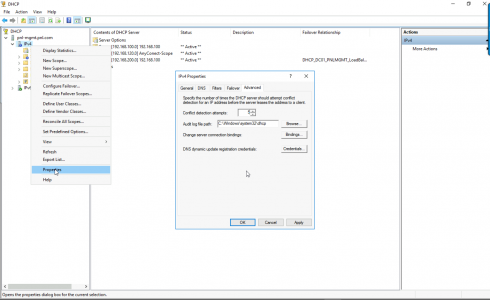
The next most popular suggestion is to enable ‘Conflict Detection‘, though in most places the information on where to find this, is incorrect, (as it’s been copied and pasted around the forums without actually checking it!) See below, you locate it on the properties of the Protocol not the Server > Advanced Tab > You are supposed to set it between 1 and 6 so I went for 5, (but after deleting all the BAD_ADDRESS entries, they were all back after 30 minutes or so, so this didn’t work for me either).
Look in the logs: Well they were useless also, DHCP creates a new log every day in C:\Windows\System32\Dhcp called ‘DHCPSrvLog-DAY.log’ as you can see it was not helpful.
At this point I put my networking head on, and ‘thought outside the box’, If DHCP is detecting these as BAD ADDRESSES, then they must be in the arp cache on the DHCP server right? Well look at this;
arp -a
Well that’s encouraging, at least now I’ve got a suspect MAC address, lookup up that MAC address online, and it comes back as VMWare (which sent me off in the wrong direction, it was not a VMware virtual machine in my vSphere in the end). Ive got a decent Cisco Switch so I thought I’d see which interface it was connected to, (but it wasn’t there).
show mac address-table
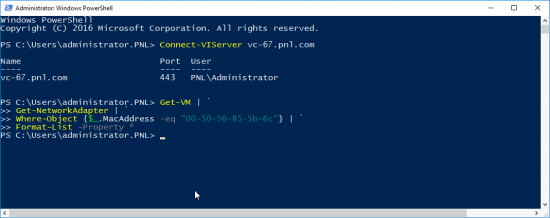
At this point I was still thinking it was a VMware virtual machine, so I used PowerCLI (Thats PowerShell for VMware), to query for that MAC address, but that revealed nothing.
So, my last hope was Wireshark, I fired it up on the DHCP server, and set the filter to;
bootp.option.type == 53
Then I deleted all the BAD_ADDRESS entries, left Wireshark ‘sniffing’, and went for lunch. I returned to this (see below). Now 192,168,100,107 was one of the BAD_ADDRESS entries, and I did not know what it was. The other entries on there for 192.168.100.3 are understandable, (that’s my DHCP server!) So now I had a Layer 3 address to hunt.
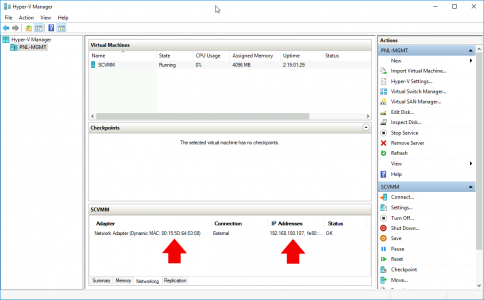
When I RDP connected to it, I got prompted for a password, so now I know it’s a Windows box! I hunted all through my VMware virtual machines, it was not there. Just as an afterthought I remembered I have a Hyper-V server, could that be running a virtual machine? BOOM! There is a SCVMM server, I was using for some Zerto testing a couple of months ago! Turned it off, problem solved!
Hope you find your culprit quicker than I did!
Related Articles, References, Credits, or External Links
NA




01/05/2020
Fantastic methodology. Thanks for sharing!
01/05/2020
Thanks David, I try to write the articles I’d like to find 🙂
11/02/2022
Awesome. Thanks for this article!
03/12/2020
Hi tnx for this helpful article. One question: when i use the command arp -a it just displays only a few IPs which have nothing to do with acutal IP addresses in my scopes… Is there any other way I could obtain the real MAC address from the DHCP leases?
08/12/2020
arp -a will only show addresses on your ‘directly connect layer 2 network’, if you are on a different range then you need to put yourself on the same VLAN as the DHCP scope (or a VLAN with a DHCP helper of course).
08/02/2021
I have same situation. Ip adress end. DHCP logs help me find problem with Kyosera 1035 MFU. He take Ip adress, after that some error, and take another IP adress until adresses ended.
19/05/2021
Thanks for the info this really help with a troublesome Mac computer, I found a repetition of MAC Addresses with the arp -a command that made it easier to find the culprit
Thanks
30/11/2021
Thank you very much for your sharing and records, wish you have a nice day 🙂
10/01/2022
Thank you so much! Same issue, but with a different BOOM! In my case it was a LANCOM access point that caused this stupid behavior.
13/07/2022
I ran through the same process. I’m a little new to wireshark but when I ran it with the command, I get for my output the DHCP server and also the 0.0.0.0 address for all of the other entries.
I looked at the entries and it seems to be a switch, an access point, and maybe a workstation. Not sure why I would get a 0.0.0.0 address instead an address within the subnet. Any ideas? Any other filters or such I can try?
Thanks!
10/11/2022
A big thank you for this article ! It’s been 24 hours since I found the cause and thanks to you I was able to find the VM that was polluting
Thanks
16/08/2024
Wow what a neat real world troubleshooting write up. I learned new spot to check!
20/08/2024
ThanQ