KB ID 0001470
Problem
Other that learn this for an exam I’ve never had to deploy this in anger. So when I heard we had a customer at work who wanted to take a look at it I was quite keen to take a look.
To encrypt a VM you need to have an additional KMS (Key Management server) which VMware do not provide. They do provide a list, so theres no point me posting a list that will be out of date in a couple of weeks. Our client expressed a preference for HyTrust, so that’s what I ran with
WARNINIG: You need vCenter 6.5 or above to do VM encryption
Deploy HyTrust KMS Server
At time of writing the current version is 4.2.1 you can get a 60 trial if you want to give it a test.
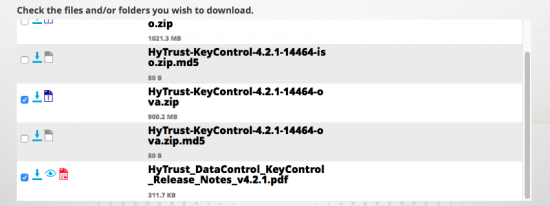
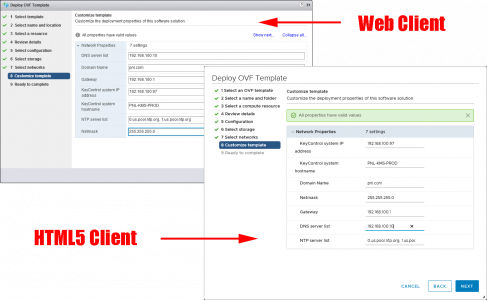
Pull down the appliance and deploy the OVF into your environment;
VMware vSphere – How to Import and Export OVF and OVA Files
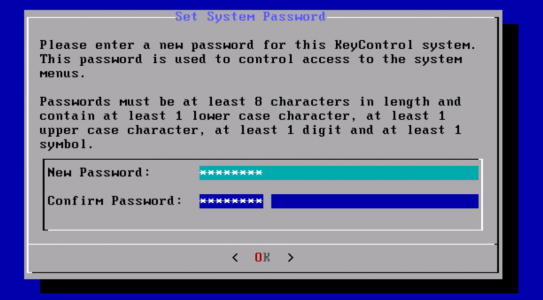
Go get a coffee, when deployed, connect to the console set a console password, and follow the instructions until it tells you to connect via a browser.
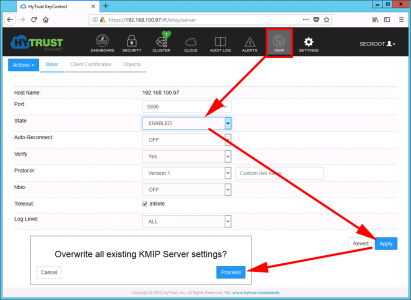
Connect via a browser (default username and password is secroot), Change the password when prompted, and proceed to KMIP. By default the service is disabled so enable it. (Take note of the port number, 5696 you will ned this later!)
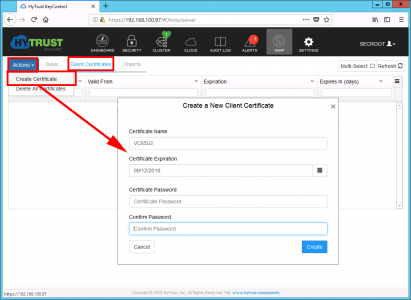
Client Certificates > Action > Create Certificate > Give it a name, and leave the password section blank.
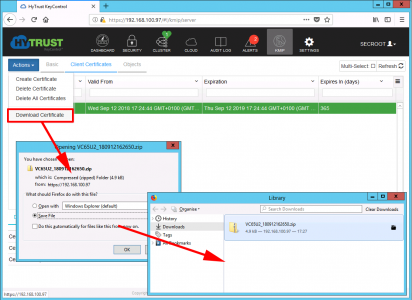
Actions > Download certificate > Save the Zip file, if you open it you will find two PEM files, (you only actually need the one that has the same name as you used above).
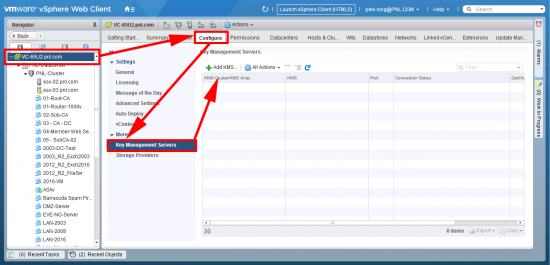
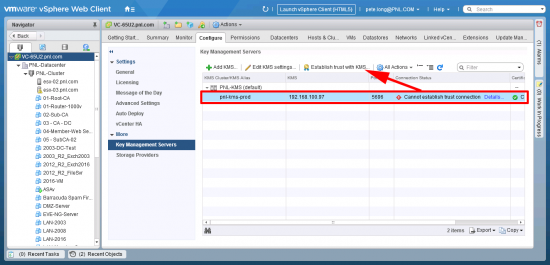
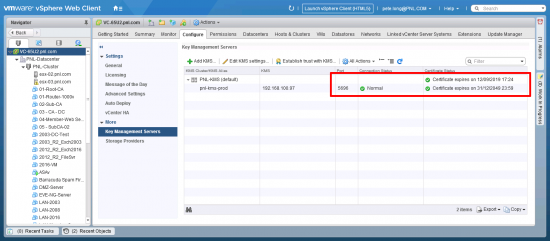
Over on your vCenter > Select the vCenter > Configure > Key Management Servers > Add.
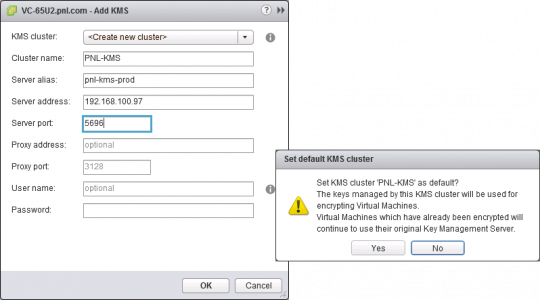
Supply a name, the IP address of the appliance, and the port number > OK > Yes.
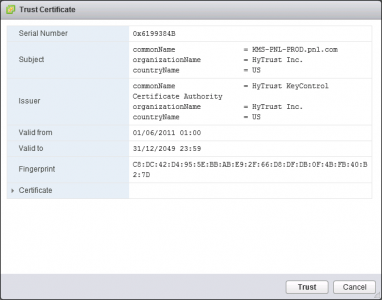
Trust.
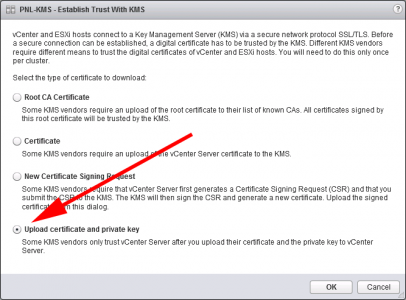
Select the KMS > Establish trust with KMS.
Upload a certificate and private key > OK.
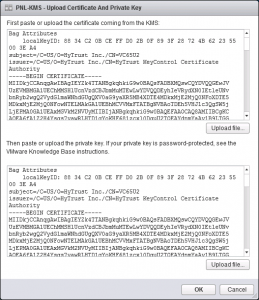
Paste in the SAME PEM FILE into both top and bottom windows. (The one with the name you chose, and downloaded earlier) > OK.
If you have done everything right all the status lights should ‘go-green’
You can now create a VM Storage Encryption Policy. (Well you can create one first, but without a KMS server, nothing will get encrypted).
Part Two: VMware: Creating a Storage Encryption Policy
Related Articles, References, Credits, or External Links
NA
