Deny RDS KB ID 0001825
Problem
Way back when I started doing tech (in the days of Novell 4 and NT4), my mantra was, if you must deny something then you’ve done something wrong. Now I work for a UK based MSP that offers SPLA licensing to clients.
Unlike typical RDS licensing, With SPLA this requires every ‘capable‘ AD user that ‘can‘ RDP onto a server (regardless of it’s a Session Host RDS Server or not) needs to have an RDS SAL.
So, when audited and hit with a big licensing bill, the clients first question is usually “How do I reduce this?“
Solution: Deny RDS
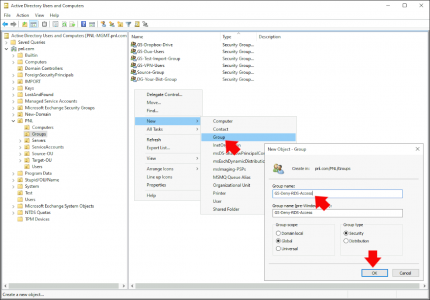
Create a new security group (don’t use domain users!) Give it a sensible name i.e. GS-Deny-RDS-Access (GS for Global security, and I don’t like spaces in names, as it makes scripts easier to write!)
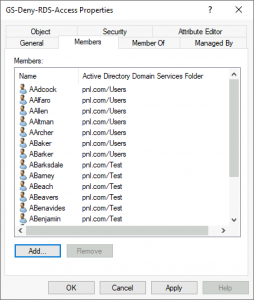
Obviously put in the users you want to explicitly deny RDS access to.
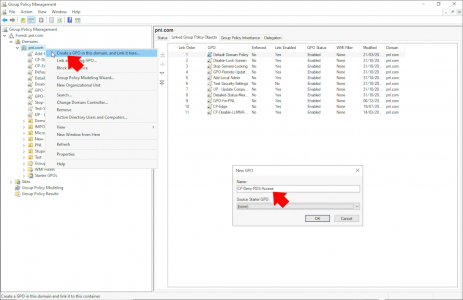
Create (or edit an existing) Group policy linked either to the OU that contains your servers (remember domain controllers are in a different OU, so link it there also). Or If you’re lazy like me simply link it to the root of the domain.
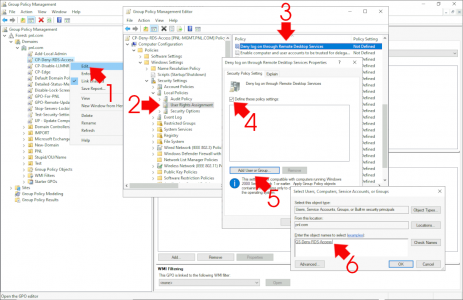
Edit the policy and navigate to.
Computer Configuration > Policies > Windows Settings > Security Settings > User Rights Assignment > Deny Log on through Remote Desktop Services
Enable the policy > Browse to and select the group you created earlier.
Then wait, or force a policy update to test.
Related Articles, References, Credits, or External Links
NA