KB ID 0001734
Problem
When considering Securing FortiGate remote administration, I’ve written about changing the https management port to something other than TCP 443 before, I suppose that’s security by obfuscation (though even a script kiddy with one hours experience, will be able to spot an html responses). Typically with other vendors you limit remote administration access, to specific IP addresses (or ranges). So how to do the same in Fortigate?
FortiGate Trusted Hosts
With FortiGate the approach is slightly different, (to Cisco anyway) in that, you allow access from ‘Trusted Hosts‘ and you do that ‘Per Administrator’ not for the entire remote access solution (like HTTPS or SSH). On reflection I like this, because by default you will have a user called ‘admin’ and an attacker will ‘possibly’ know that. With FortiGate you can restrict the admin account so it can only log on from inside, or from management hosts/networks or from an Out of Band management network.
You can also give an administrative password to one partner and only allow access from that partner’s public IP/Range, or if like my firm we need to support a lot of firewalls we can hard code this into our default deployments and retain remote administration. (Though FortiManager is the direction you want to be headed in, for that!)
Configure FortiGate ‘Per Administrator’ Trusted Hosts.
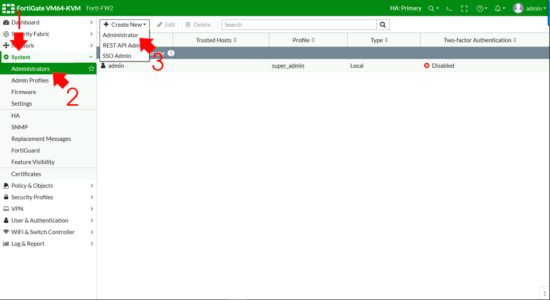
System > Administrators > Create New > Administrator.
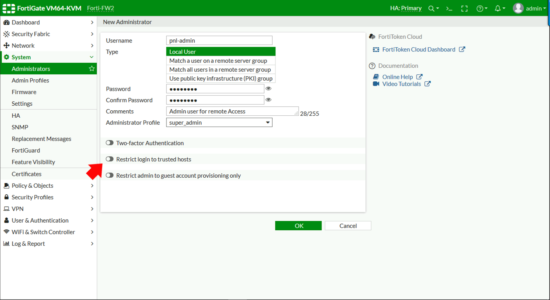
Create a username/password > Select the admin level required > Enable ‘Restrict Login to Trusted Hosts’
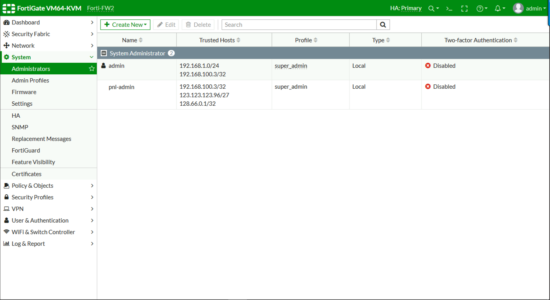
Here’s an example where the admin account can only manage the firewall form the 192.168.1.0/24 network, and a management host 192.168.2100.3 For ‘external‘ access I’ve got a new administrator, who can get access from my management host, (for belt and braces), a single public network, and a public IP address.
Related Articles, References, Credits, or External Links
NA

06/05/2022
this is not a very good solution.
security auditors don’t like to see the management interface even loading.
cisco gets this right
fortinet is being dumb here
they will just keep bringing the fact to the management “we can STILL see the interface” justifying more audits and time wasting for IT.
11/05/2022
I’ve spent over 20 years deploying Cisco firewalls, externally with Cisco you can change the port or change the management IP, Forti you can do both those things, and then further secure it to a different login account.
>>Security auditors dont like to see the management interface even loading
Restrict the access IPs then? Or disable remote access and only manage the device via VPN.
06/06/2022
management can be disabled per interface, internally if it still needs completey limited use a management VLAN
09/08/2022
“firewall local-in-policy” is, what you need, if you do not want to see ssh prompt.