KB ID 0001403
Problem
Back in Part One, we setup the AD (Groups,) and the Certificate services that will knit everything together. Now we need to configure an NPS server that acts as a RADIUS server for our remote clients, And a RAS Server that our remote clients will connect to.
Step1: Network Setup
Microsoft have an alarming habit of telling you to connect DMZ assets to the LAN. In their defence I’ve seen some documentation where theres is a firewall in front and behind their RAS/VPN server, but then you keep reading and they refer to the NIC on the LAN and the NIC in the DMZ. As you can tell I’m not a fan, I prefer to have an un-authenticated and an authenticated DMZ, and neither of them are connected to the LAN, So then I can control what can, and cannot flow between the DMZs and the LAN.
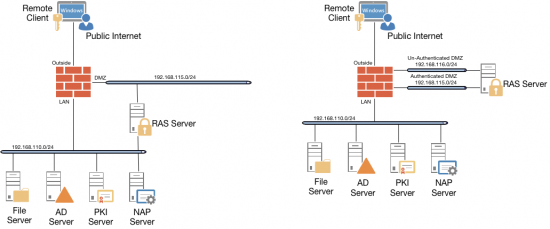
My way means I have to allow more ports for domain membership etc, but, if you have a Cisco ASA I’ve covered that in the following article,
Cisco ASA – Allowing Domain Trusts, and Authentication
As for the VPNs and RADIUS you need to allow the following;
From Outside to the RAS Server
- UDP 500 (ISAKMP)
- UDP 4500 (NAT Traversal)
From the RAS Server to the NPS/NAP Server
- UDP 1812 (RADIUS Authentication)
- UDP 1813 (RADIUS Accounting)
- UDP 1645 (RADIUS Authentication)
- UDP 1646 (RADIUS Accounting)
Quite why it needs both pairs or RADIUS ports I’m unsure, I’ve not scanned or packet captured the traffic, but I’m wiling to bet it really only needs 1812/1813 or 1645/1646.
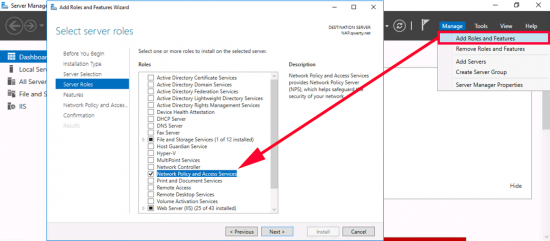
Step2: Install NPS
Server Manager > Manage > Add Roles and Features > Network Policy and Access Services > Complete the wizard accepting the defaults.
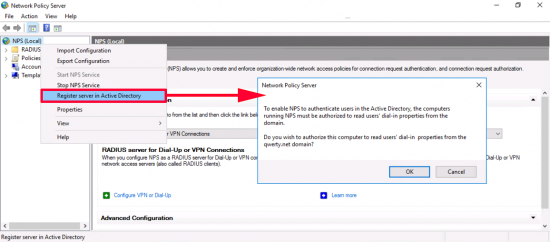
Administrative tools > Network Policy Server > Right click NPS (Local) > Register in Active Directory > OK.
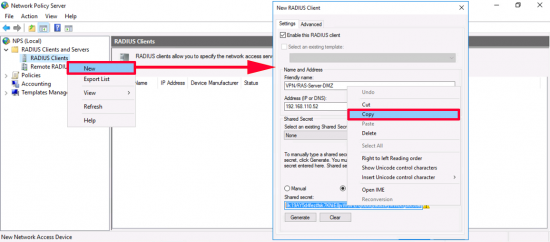
Even though its not setup yet, we need to create our RAS server as a RADIUS client > RADIUS Clients > New.
Friendly Name: A sensible name that identifies the RAS server
IP: IP of the RAS server (On the LAN segment)
Shared Secret: Generate a new one and copy it to the clipboard, (you will need it in a minute.)
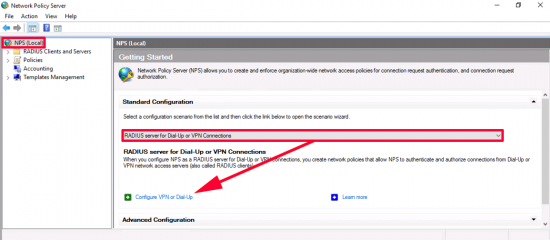
On the main page, ensure ‘RADIUS server for Dial-Up or VPN Connections’ is selected‘ > Configure VPN or Dial-Up.
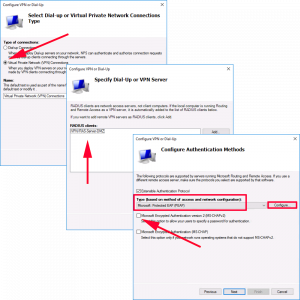
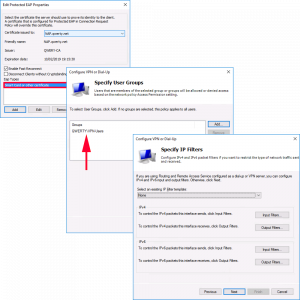
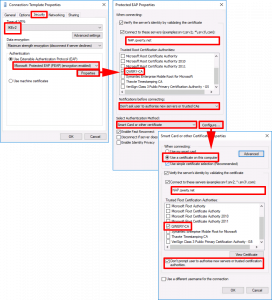
Select ‘Virtual Private Network (NPS) Connections > Next > Ensure the RADIUS server you have just created is listed > Next > Ensure ONLY ‘Extensible Authentication protocol’ is ticked > Change its value to Microsoft Protected EAP (PEAP) > Configure.
EAP Types: Remove the one that is listed by default > Add in ‘Smart card or other certificate’ > OK > Under Groups make sure sure you have ONLY added the group you created back in part one > Next > Next.
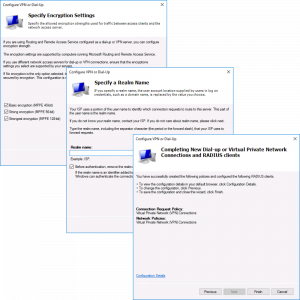
Next > Next > Finish.
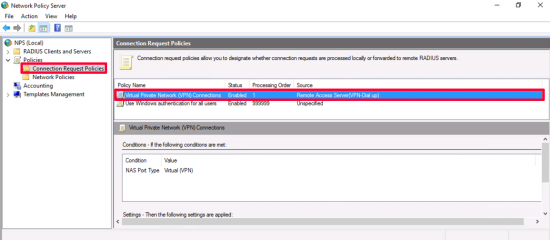
Your connection request policies should look like this.
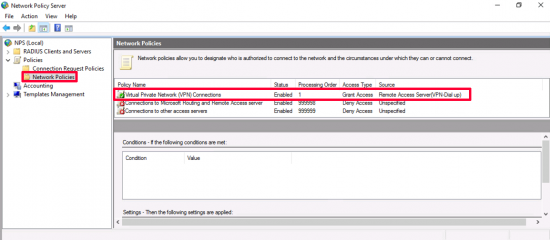
Your network policies should look like this.
Step 3: Setup RAS
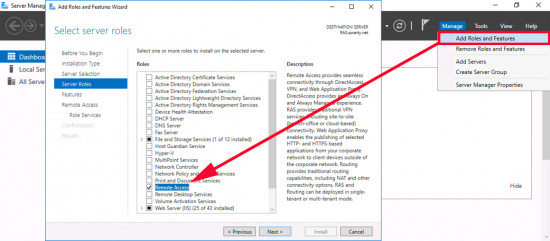
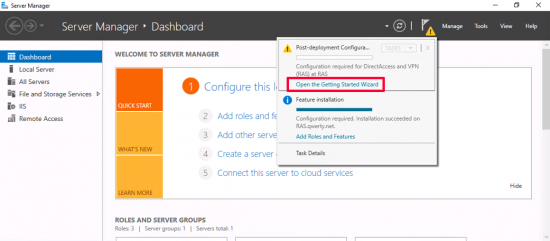
Server Manager > Manage > Add roles and Features > Next > Next > Next > Remote Access > Next.
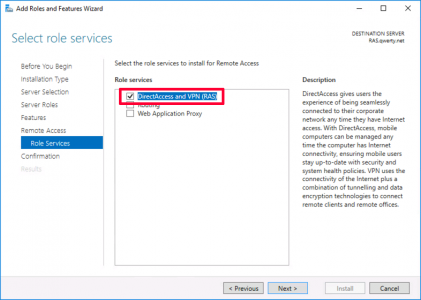
Select DirectAccess and RAS > Finish the wizard accepting the defaults.
Open the Getting Started Wizard > Select VPN Only.
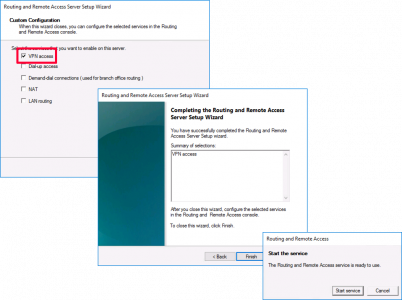
Administrative Tools > Routing and Remote Access > Right click {server-name} > Configure and enable Routing and Remote Access > Next > Custom configuration.
VPN Access > Next > Finish > Start service.
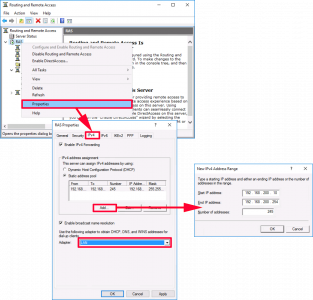
Once again right click {server-name} > Properties > IPv4 > Note: If you are not going to use your internal DHCP server/scope, then you can set one up manually (as shown) > Ensure ‘Enable broadcast name resolution’ is selected, and the RAS servers internal/LAN interface is selected > Apply.
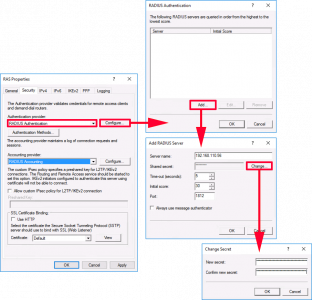
Security Tab: Authentication provider = RADIUS Authentication > Configure > Add > Enter the IP of the NPS server > Change > Paste in the shared secret you copied, (above) > OK > OK.
Repeat the same procedure for Accounting provider, (below).
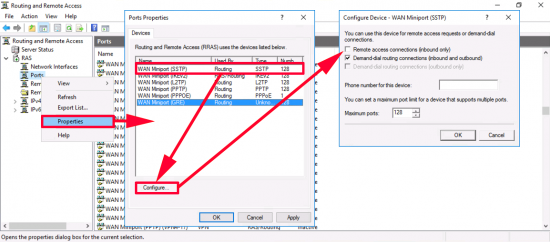
Drill down to ‘Ports’ > Right Click > Properties > Select SSTP > Configure > Remove the tick from ‘Remote access connections (inbound only) > OK. Repeat this procedure for ALL the protocols EXCEPT IKEv2, (So when finished, only IKEv2 is set to accept incoming requests).
Step 4: Configure Reference Windows 10 Machine
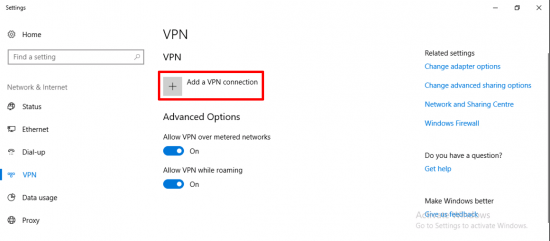
On a Windows 10 machine* Launch the ‘Change virtual private networks.
*Note: Your logged on user, must have a certificate issued to them, and be a member of the AD group we created earlier.
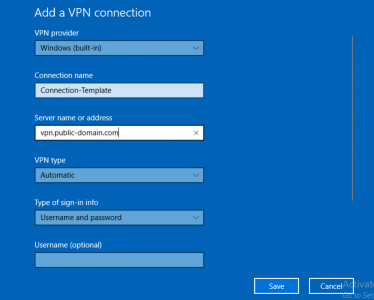
Add a VPN Connector.
- VPN Provider: Windows (Built-in).
- Connection Name: Connection-Template.
- Server Name or address: (The ‘public’ name we put on the certificate on the RAS server).
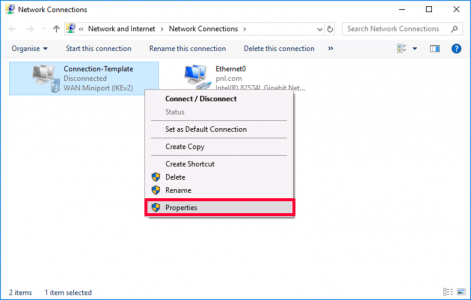
Change Adapter options.
Right click the VPN connection > Properties.
Security Tab:
- Type of VPN: IKEv2
- Data Encryption: Maximum
- Use Extensible Authentication Protocol (EAP)
- Properties > Enter the name on the certificate on your NAP Server, (I know that does not make sense trust me!)
- Tick your Root CA Cert for the domain.
- Select ‘Don’t prompt user to authorise new servers or new authorities’.
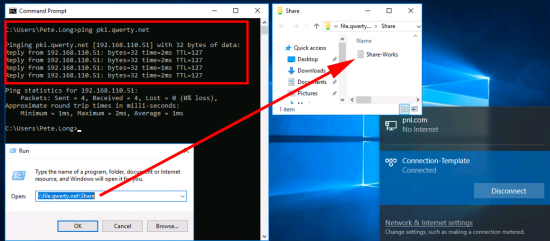
Connect your VPN to test it.
Make sure everything works.
Note: I had some DNS resolution problems, see the post below to find out how I fixed them;
Windows 10: Remote VPN Client Cannot Resolve Domain DNS
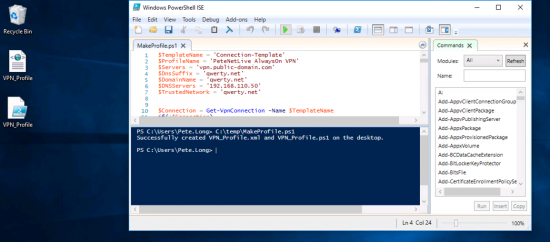
Now you need to ‘capture’ all those settings so you can give them to your other clients. To do that you need a copy of the PowerShell script MakeProfile.ps1 You will need to edit the script a little, see the example below. Running the script will output two files to the desktop, an PowerShell Script and an XML file
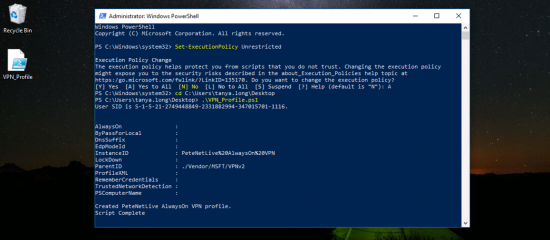
Step 5: Deploying the Settings
At the time of writing you can deploy these settings via three methods, PowerShell Script, SCCM, or Microsoft Intune. I’m simply going to run the PowerShell Script, there are a few restrictions though, you have to be logged on as the particular user. They need administrative rights to run the script, which is a bit of a pain, you can use restricted groups and set the powershell to run at logon with group policy, then remove the policy when configured, but it’s still a bit of a drama. Below I’m simply running the VPN_Profile.ps1 file I generated above.
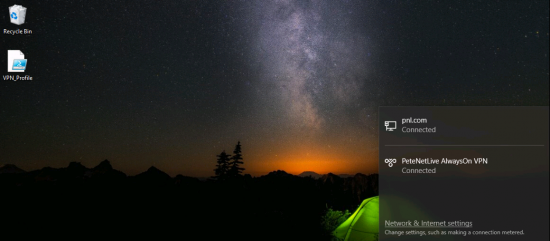
Now once the user logs in, (and has a valid remote internet connection.) The remote client will auto-connect.
That covers USER tunnels, you can also, (Post 1709 Windows 10 Builds,) have DEVICE tunnels. Which I would write a part three about, but I simply cannot get them to work, so I’m waiting for the bugs to be ironed out, and I will revisit it at some point in the future.
Related Articles, References, Credits, or External Links
NA





10/09/2018
Thanks for your clear and detailed walk-though.
Some questions on the network setup diagram. On the left side, the DMZ is on the same subnet as the internal LAN. Is that intentional or just a copy and paste type of error?
The second similar question is about the diagram on the right side – the Authenticated DMZ is also on the same subnet as the internal LAN – is that intentional?
Also on that diagram, is that meant to be a single firewall device, and the Authenticated and Unauthenticated DMZ interfaces on the RAS server are both connected to that same device?
11/09/2018
Hi Ralph, thanks for spotting the typo! LAN is 192.168.110.0/24 (Image updated). Both deployments use a single firewall, On the left the RAS server is connected both LAN and DMZ. The second deployment (on the right) Is MY PREFERRED method, to have an un-authenticated and an authenticated DMZ with the RAS server connected to both.
13/09/2018
Thanks! That makes much more sense.
26/10/2018
Pete,
how could you use the setup without using DMZ? Would you need the NPS server registered IP on the internet as well to do that? looking to set it up and test it also….the client supposed to ask for your creds? when I tried to set it up the first time, I don’t remember it doing that.
Thanks,
Chris
29/10/2018
You would need a public facing NIC on the RAS server, I would not recommend this.
P
01/11/2018
Hi, Any update on when the part 3 will be written as I need the device tunnel working. We also seem to be falling at a authentication attempt due to the following reason: The connection was prevented because of a policy configured on your RAS/VPN server error?
Our setup is roughly the same as this setup. 2 x VPN a cluster in the DMZ behind a external DNS name, NPS on the LAN
02/11/2018
Hi Steve, I had such a bad experience with it I’ve never revisited it 🙁 Ill stick with Cisco AnyConnect, Sorry Buddy
15/01/2020
I too am failing with the same error. Honestly not sure what’s wrong here. Have you figured it out?
22/02/2019
Hi, First of all i want to say that this guide has helped me a lot! But i had 1 question, Am i obligated tu use (P)EAP? of can i use something like MSCHAP?
25/02/2019
I don’t see why not, I only ever use PEAP/EAP or EAP/TLS.
P
26/02/2019
Hi, Has anyone experienced an issue with Windows 10 refusing to save the PEAP settings? Particularly specifying the servers to connect to and the certificate to use?
This is on Windows 10 Enterprise 1803
12/06/2019
Hi James,
I included the information in the template that I used to generate the powershell script that creates the profile, in my environments, I have not faced this issue.
However, the way I deploy the profile to my users may work as aworkaround for you.
I create a scheduled task on the clients with a GPO, the task runs with highest priviledges and as SYSTEM. The task triggers the profile-creation script, with a few changes.
I start by checking if the profile is already present, if it is, then it skips to the end.
If not, then it creates the profile.
The script could be edited to remove the existing profile first and then re-add it.
18/03/2019
You say:
“UDP 1813 (RADIUS Accounting)”
But later:
“it really only needs 1812/1823”
Now what? 1813 or 1823?
19/03/2019
1812 if your only doing authentication, and 1813 if you doing accounting as well.
02/04/2019
I got device tunnel to work. The problem i have now that my logon script tries to run before the user is completely logged in. I dont want to set a delay on the logon script (because it will affect other users). Is there a way that when the connection gets build up the logon script is called?
03/04/2019
Use an AnyConnect Login script?
12/02/2021
Hi Jordy,
Just wondering how you got your device tunnel up and running. I have follwed all the settings but still getting the 13801 error
12/05/2019
Hi Pete,
Excellent article!
Helped me get through this and understand what I didnt from MS articles.
You ask about DEVICE AUTH.
As I found out, simply
– auto enroll Computer certificates
– RAS > Properties > Security > Auth Methods > Allow Machine Certificate…for IKEv2
– On Windows 10 client – under Security > Auth > Instead of EAP – simply choose “use machine certificates”
VOILA
06/09/2019
Hi Pete,
Brilliant tutorial! you should be writing documentation for Microsoft as this is much more helpful than theirs 🙂
Thank you – appreciate all the effort!
01/10/2019
Hi Pete,
Very useful article !.
I observed that I continued getting authentication method error. If I set NPS server & W10 to Microsoft: Peap, the W10 fails to connect. If I set both to EAP-MSCHAP v2, I get prompted, but I get connected
23/10/2019
Hey Pete,
great Article!
There is one question regarding the un-/authenticated DMZ deployment.
Doesn‘t the RAS Server need to be a Domain-Member to receive the proper Certificates?
How do you accomplish that?
Thanks & keep up to good work,
Mike
24/10/2019
No, you can do a CSR and issue a certificate to a non domain joined server 🙂
19/12/2019
Hi Pete,
I have managed to implement VPN, it connects but I cannot access anything on the local domain, I cannot ping via ip or hostname. I checked my ip address and it doesn’t show a gateway, is this correct or needed? The VPN server has two adaptors, PROD and DMZ, and within the properties of ipv4 in routing and remote access, I have specified a static IP and select PROD as the adaptor. Yet no luck?
29/04/2020
Paddy,
Did you resolve your issue?
I can’t ping anything on the local network or even the internal interface IP On the RRAS. Unless I wait. Which can take 5mins. Sometimes 30 mins or even an hour and then all works fine. Or to speed this up, I can disconnect and then reconnect. But I’m not satisfied with that.
15/01/2020
Thank you for the great step by step instructions. I was able to setup mostly everything because of these. However, when trying to connect from client, I’m receiving “The connection was prevented because of a policy configured on your RAS/VPN server. Specifically, the authentication method used by the server to verify your username and password may not match the authentication method configured in your connection profile. Please contact the Administrator of the RAS server and notify them of this error.” It’s the same error message in RAS server as well and I’ve followed everything in the article exactly, I think. I am not sure what to look for and I would love to get any insight on this.
31/01/2020
Hi.
I have the same error – did you resolve this ?
27/02/2020
If you check event viewer, what errors do you get
27/03/2020
I got this on a recycled server that I previously had tried to configure Direct Access on. I uninstalled everything and reconfigured but always got the error. I spun up a new VM, ran through the same config and it just worked. RRAS tends to leave things behind.
27/04/2020
If you are using NPS on Server 2019, there is a bug with the Windows Firewall rules and NPS. It doesn’t actually let the traffic on ports 1812/1813 through. This causes the above error. To fix this issue, you must run “sc.exe sidtype IAS unrestricted” and this will allow the traffic through.
27/02/2020
Hi, wanted to know best method to provide redundancy. I have two sites and have currently configured working in site A, however once in side B what would be best for redundancy and load balancing? Anyone set this up in this way
16/04/2020
This is incredibly helpful! I’m constrained to implementing the ‘dual dmz’ approach you show at the top of the page. I’m a bit floored about how to setup the NICs, Default Gateway, and possible Static Routes. I’m sure it’s all very doable, just not sure how to go about it.
03/05/2020
Hi,
Thanks for your guide.
It’s very helpful but it lacks one thing : A small IP configuration sheet.
How did you configure your RRAS / NPS interfaces ?
I’ll have to implement the same infrastructure as you did in the right drawing by the end of May for 8.500 computers.
I’m not he network architect in the story, I’m in charge of the MS part… but I’d like to have a clearer view of how you configured each network interfaces.
Another question : do you think we could use an already implemented RADUIS solution (not MS) ?
Thanks in advance
08/05/2020
Hi again, I’m really confused.
Can you help me please?
My LAB is made like this:
LAN: 192.168.253.x (.1 = AD01 / DNS / ADCS – .40 = MECM01 – .250 = FW NIC)
RRAS NIC1 facing the LAN connected to the firewall (192.168.100.250): 192.168.100.70 / no default GW
RRAS NIC2 facing the WAN connected to the firewall (192.168.99.250): 192.168.99.70 / default GW = FW 192.168.99.250
I give the 192.168.200.150-250 range to VPN clients
WAN: 192.168.33.x (.80 = FW NIC)
Certificates are OK everywhere.
Questions :
Do I have to enable Routing Feature on the RRAS?
Do I have to route the IP range (eg: 192.168.200.x) I give to the VPN clients?
Can you give an IP range from the LAN (eg: 192.168.253.x)?
I currently can mount my device AOVPN, the client gets that 192.168.200.150 address… with no GW and DNS = 192.168.253.1 and that’s all.
Which ports do I open from NIC1 to LAN?
I’ve tried any any for now from NIC1 LAN but it doesn’t change anything.
Do I have to configure NAT?
For now, pinging 192.168.253.1 (DNS / AD server) from NIC1 comes with 192.168.100.70 IP address.
Maybe I’m completely wrong but I don’t understand why I cannot see any of the 2 servers I have in the LAN.
Even adding static route on ADC01 192.168.200.0/24 192.168.253.250 doesn’t change anything.
Thanks in advance
09/10/2020
Really appreciate your article. It was so much more comprehensive than the Microsoft one. I set it up a while back and it has been working amazingly.
I’m now having an issue. Our NPS server certificate renewed 2 days ago, and because the clients are set up to verify the server, the new id it is presenting is different, so the clients fail to connect as they don’t recognize the server.
If on the client I pick “Tell user if the server’s identity can’t be verified”, instead of “Don’t ask user to authorise new servers or trusted CAs” it does pop up a message that it can’t verify the server, and asks if you want to continue, and if you agree, it will connect. Not really the intent of a seamless connection.
I can just turn off “Verify the server’s identity by validating the certificate”, but again, not really the most logical choice.
Hoping you can tell me what is required so my clients can again recognize the NPS server with it’s renewed machine certificate.
08/05/2021
Amazing article and my AlwaysOn VPN have been working for sometime so far, I tried today and I was getting “Cannot connect the parameter is incorrect”. On the client machine this is the only logs I am getting.
CoId={0119583F-6B27-41A9-A9E5-D12F0508A985}: The link to the Remote Access Server has been established by user xxx\XXaa.
CoId={0119583F-6B27-41A9-A9E5-D12F0508A985}: The user XX\XXaa dialed a connection named AlwaysOn – VPN which has failed. The error code returned on failure is 87.
Nothing showing on the server, it seems that establishes the connection then it fails. If you can help out Pete I will be so grateful.
08/06/2021
Hi Pete,
Thanks for the article/Post
some questions:
1. Why are you using a RRAS as part of the setup ? (considering you also have a CiscoASA in the configuration) ?…. Firewall can provide VPN connectivity to the directly without the need for a RRAS ?
2. Unless this is related to the “Always ON” feature ? & hence you need it ?
3. I got tsomething similar setup using firewall + NPS + A/D + IKEv2 (windows built-in client) but no RRAS. It works great. I’m trying to work out how to get the “Always ON” component hence my questions above
cheers
09/06/2021
1. This is Microsoft ‘Always on’, not Cisco AnyConnect ‘Always on’ that’s two different things?
2. As above.
3. Sounds like you have L2TP?
16/11/2021
Hey Pete,
You have a typo in your config:
Step 3, you mention “Authentication Provider” twice, instead of Authentication Provider and then Accounting Provider when configuring RADIUS.
Justin
21/11/2021
Thanks 🙂
05/12/2021
Followed this guide (great guide for ease of understanding by the way), and all works well connecting wise, however one minor problem. Once connected via ikev2 we cannot access any local resources on our internal network. If we reconfigure the RRAS back to PPTP, all works perfectly in respect to accessing resources. Seems that (in our case anyway), the moment we decide to use ikev2 authentication, all forms of routing come to a dead halt.
It’s a 2019 server located in AWS.
Have added routes, deleted routes, tried server 2016/2019, tried Windows 10 client and windows 11 client, tried different carrier providers to ensure it wasn’t them blocking traffic. Every single site we look up say go to the network settings and uncheck “use default gateway”. Which, works for internet sure, but absolutely does not fix the access to local resources issue.
The only thing we are doing different to the guide, is using an IP pool in the 172.16.3.0/24 range. This was to ensure no conflicts arose between VPN clients and local clients even in the most bizarre of circumstances for it to occur (despite it being all blocked off with firewalls, it’s an old habit from the 90’s I still use.
However, we have tried using DHCP pool (clients can’t obtain an address as it fails when they connect), tried using the same range as internal perimeter, same range as external perimeter, tried random pools of IP addresses. Anything to try and get this thing to route traffic. (yes I know, some of those ideas were wrong, but we were getting desperate to see why the RRAS server won’t route (2019 is our latest incarnation for info)
I’m sure it’s just either a checkbox or the smallest of things I have missed.
03/01/2022
Thank you for your great gide.
I am using the configuration with an unauthenticated and an authenticated DMZ.
I assign the VPN clients an IP address in the subnet of the authenticated DMZ.
Connections works fine, name resulution works fine and I can access my servers.
The problem is that I can not access the internet from my vpn client while it is connected.
Of course I added a firewall rule to allow traffic from my authenticated DMZ to the internet.
I assume this is a routing problem. How does the vpn client know which gateway it should use in my authenticated network? Or am I wrong?
Thanks in advance
22/01/2022
I found the solution to my problem. I had to add a static route on the RAS Server to 0.0.0.0
Looks like the clients get this route when connected. And find their way to the internet.
25/08/2023
Thanks for sharing. Just a quick question regarding routing and FW rules. In the scenario in your righr hand side picture were you have two interfaces on the RRAS server to be able to limit traffic. But how about the VPN clients.. Can we in this solution limit access in the FW and if so, is that based that the clients traffic goes through the “Authenticated DMZ” interface but using the subnet
192.169.200.x/24 so in the FW we can limit using that subnet?