KB ID 0001286
Problem
A few weeks ago I installed a 5525-X firewall for a client, and set it up as follows;
ASA Setup FirePOWER Services (for ASDM)
And all was well, then a week later I got an email…
One of our teachers is doing a project with MATHS and ICT involving bitcoin.
Basically, he has something called BITCOIN CORE WALLET installed and it used to work with the old Firewall.
I’ve installed it on my work laptop and taken it home on my Internet connection & it works fine.
BUT, when I bring it back into school, its failing.
When I bypass the Firewall, it also works – so I guess IPS/AMP is blocking something.
The software seems to start and then download/sync “stuff” for bitcoin.
In school it tries and then says “NO block source available“
Google seems to hint towards network issues.
If definitely did work, as the teacher has screen grabs of it working.
Any ideas what could be blocking this ?
Now Bitcoin uses a series of ledgers that update each other around the world, (to make it resilient). So if the FirePOWER was the culprit, then it was either identifying it as a bot, or I had a rule specifically blocking Bitcoin?
Solution
Note: Bitcoin does need TCP port 8883 open, but that didn’t seem to be the problem.
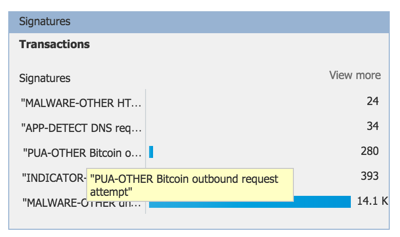
Thankfully on the monitoring tab, as soon as I logged in, the answer was staring me in the face, (I had to change the time frame to last 30 days first).
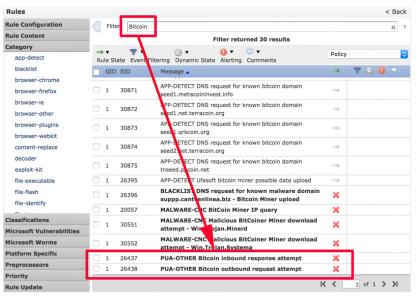
Not only does it confirm the FirePOWER IDS blocked it, but it also told me which ‘Rule’ it had matched, (PUA-OTHER Bitcoin outbound request attempt). PUA stands for Probably Unwanted Application, in case you were wondering. Edit your IDS policy, and search for ‘Bitcoin’.
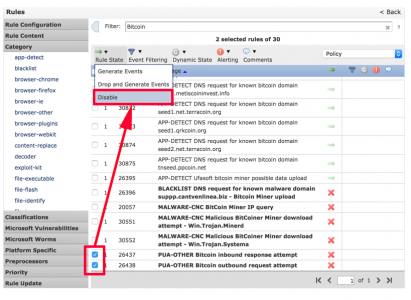
I’ll leave the Malware rules alone, but I’ll allow both the PUA-Bitcoin rules, (i.e. set them to ‘Disable’).
Then don’t forget, you need to deploy the new FirePOWER policy and ensure that your access control policy says it’s up to date on all devices, before you test again. If you’re unsure how to do that, see the link I posted above.
Related Articles, References, Credits, or External Links
NA

12/03/2017
Hi Pete,
Can you create a HOWTO setup firepower on a ASA?
I own a 5506-SEC-BUN and I’d like to know to set it up.
Thanks
12/03/2017
Already have http://www.petenetlive.com/KB/Article/0001107
P
20/03/2017
Thanks for posting great articles. 🙂
21/03/2017
No worries, thanks for the feedback
P