KB ID 0001197
Problem
Here we are dealing with the older IPSEC VPN method of remote VPNs, NOT AnyConnect. There is/was a VPN client for Mac OSX which you can still download. But modern versions of OSX have the Cisco IPSec VPN client built into them.
I’m assuming you have already configured the firewall, if not see the article below;
Cisco ASA5500 Client IPSEC VPN Access
Solution
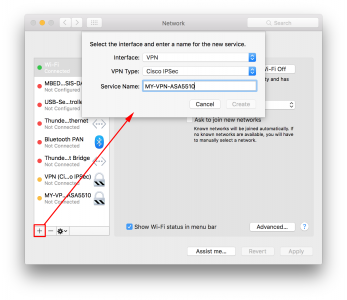
Open your network preferences and add in a new connection > Interface = VPN > VPN Type = Cisco IPSec > Service Name = A sensible name you will recognise, (like connection to work, or home etc.)
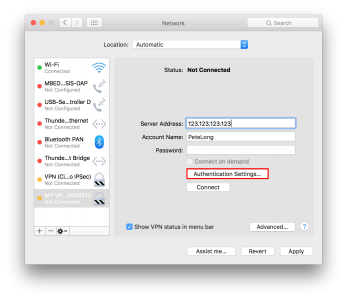
Server address is the public IP, (or name if you have DNS setup*) of your Cisco Firewall > Enter your VPN username > I don’t put in the password, so I will have to type in in manually > Click Authentication Settings.
*For DNS you will need a static public IP, and a registered domain name. The ASA DOES NOT support DNS updates to online services like DynDNS or No-IP etc. It does support DDNS but means the server that leases you your public address is supposed to update your DNS for you, and unless you are your own ISP, and you host your own public DNS records, this wont work!
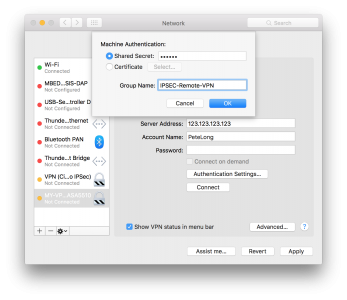
Here you need to supply the ‘shared secret’ for the VPN tunnel, and the Group Name. Your firewall admin should give these to you. If they don’t know, tell them to run ‘more system:running-config’ on the firewall and give you the shared secret and ‘group-policy’/’tunnel-group’ name for this remote VPN > OK.
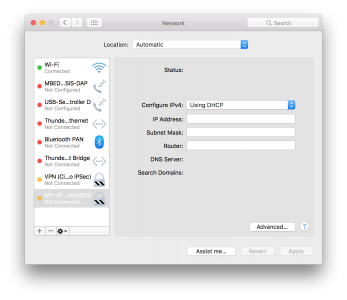
Nearly every time you use DHCP, the firewall with either lease you an address from a ‘pool’ of VPN addresses, or broker the connection, and use your internal DHCP server.
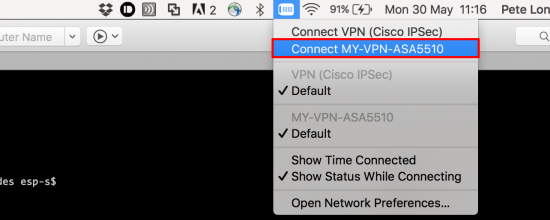
Now to connect the VPN, select the icon shown, and click your Cisco VPN, (in the picture I have two).
If you didn’t put your password in during setup, you will be prompted to enter it to continue.
It does not work?
With all things Cisco, if there’s a problem your easiest way to a solution, is to run a ‘debug’ on the firewall. Execute the following two commands on the firewall, and attempt to connect again, this should point you in the right direction.
debug crypto isakmp 127 debug crypto ipsec 127
Related Articles, References, Credits, or External Links
iPhone and iPad – Configure the Cisco VPN Client


11/05/2020
How do you get the debug info from the Mac? Is it possible to see the IKE and IPSec SA details?
15/05/2020
That is a great question, I would debug this directly on the VPN device (ASA our ISR for example).
30/08/2020
Answer the question! One doesnt always have access to the vpn device
31/08/2020
Jeez Calm down! I didn’t post about debugging on the OSX client because if the asker followed up I would not be able to help them. If they debug the connection on the device, I can probably diagnose the problem and help the asker to fix it.
So To debug the VPN connection on the Mac, In Finder > Go > Go to Folder > /Applications/Utilities/ > Open console.app > click ‘errors and faults’ > in the search bar at the top type ‘neagent’ like this
01/10/2020
Hey there!
I configured my VPN as you mentioned, I have the Shared Secret and name group, but my mac returns an error saying “An irreversible configuration error has occurred. Check configurations and try again.”
I’m not sure what I’m doing wrong, and I’m maybe the only one at my institution using a Mac.
Do you have any idea as to why this error occurred?
Thanks in advance
01/10/2020
Hi It’s difficult to troubleshoot from the client end, (but not impossible) see my answer to Matts post above. I sympathise, being the only Mac user where I work is a challenge, and getting someone from your internal IT to help, is usually a non starter! Do you know have AnyConnect available?
12/02/2021
Hi there,
Thank you for the detailed instructions. I was able to succesfully create a connection to the cisco VPN and i can access network resources and run RDC perfectly. I can’t connect to any non-network resource / public websites though. I assume this is a DNS issue? Do you have any advice?
Thanks
16/02/2021
You need to enable split tunnelling (on the firewall) use the search function above
P