KB ID 0001182
Problem
There’s an alarming amount of people who have contacted me about this error;
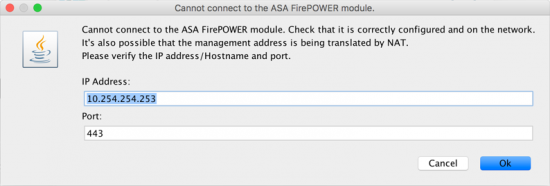
Cannot connect the the ASA FirePOWER module.
Cannot connect the the ASA FirePOWER module.. Check that it is correctly configured and on the network. It’s also possible that the management address is being translated by NAT.
Please verify the IP address/Hostname and port.
Note: If you have just updated or re-imaged the SFR module, see this article
Solution
You see this error when YOU attempt to connect to the ASDM, it does NOT mean the firewall cannot see the FirePOWER module. So look at the IP address it’s telling you that it can’t see, in the example above thats 10.254.254.253 can YOU ping that address from YOUR location?
You will see this error if the FirePOWER module is incorrectly cabled or not plugged into the same network as the inside/LAN of the parent firewall. Or if the management port is misconfigured, see the following article; (yes even if you are using FMC).
ASA 5505-X / 5508-X Setup FirePOWER Services (for ASDM)
You will also see this error if you are on your corporate LAN and the FirePOWER module does not have route to get to you. See the following article;
Cisco FirePOWER – Adding a Static Route
You will also see this error if you are connected to the ASDM from the firewall’s PUBLIC ip address. To avoid this error, and to manage the SFR externally you would need to have done the following;
- Connect to firewall via a VPN (which has access to the network segment that the inside, and management interfaces are on).
- Have ‘management-access’ enabled on the inside interface.
- Allowed https/ASDM access from the VPN subnet, and opened the ASDM from the firewalls INSIDE IP.
Follow the solutions in the following article;
Cannot Manage ASA via AnyConnect VPN
Related Articles, References, Credits, or External Links
NA

21/11/2016
I had a similar issue it turned out my lan gateway was not pointing to the firewall inside ip address which caused a routing issue.
05/09/2018
Once again, thanks Pete! Adding a static route fixed the issue.
06/09/2018
Thanks for the feedback.
15/05/2019
I have 2 firewalls configured as active passive mode, ports g7, g8 are in failover and stateful mode.
Also g1 , 2 and 3 are the standby
my question is how can i make the management firepower interface works as stand by as well ?
16/05/2019
A failure of the SFR module will cause a failover event, however each SFR must be licenced and configured separately.
P
13/11/2019
Hi Pete!
Should the SFR modules be configured with the same IP adresses etc for the failover to work? If i put one on 10.0.0.2 and the other on 10.0.0.3, how would the ASA know to sent traffic to the other IP address?
13/11/2019
NO! they are completely separate, the active firewall sends traffic though the SFR that’s inside it, the IP of the SFR does not matter at all (as long as it’s up) You need two lots of Licences as well! and you need two configs (though you can export the policies from one to the other).
14/11/2019
Yeah, I managed to find the information regarding the licenses but nothing on the network configuration in HA, thank you very much for the quick reply!
14/11/2019
No probs.