OCSP KB ID 0001145
Problem
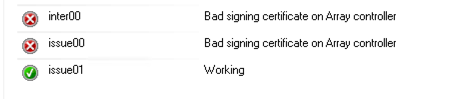
I had a client ring in the other day, they have a three tier PKI solution on Windows Certificate Services, that I put in about a year ago, it has been running fine, but now they were seeing some errors.
Bad signing certificate on Array controller.
The following errors were also being logged;
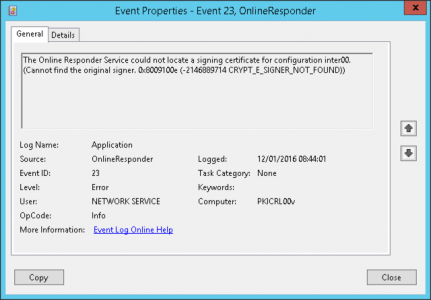
Event ID 23
Log Name: Application Source: Microsoft-Windows-OnlineResponder Date: 12/01/2016 08:44:01 Event ID: 23 Task Category: None Level: Error Keywords: User: NETWORK SERVICE Computer: PKICRL00v Description: The Online Responder Service could not locate a signing certificate for configuration inter00.(Cannot find the original signer. 0x8009100e (-2146889714 CRYPT_E_SIGNER_NOT_FOUND))
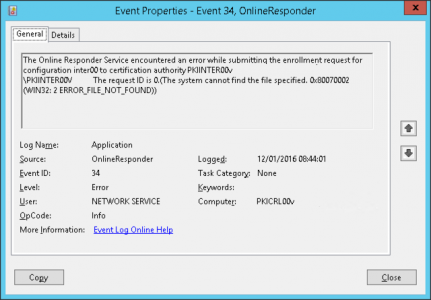
Event ID 34
Log Name: Application Source: Microsoft-Windows-OnlineResponder Date: 12/01/2016 08:44:01 Event ID: 34 Task Category: None Level: Error Keywords: User: NETWORK SERVICE Computer: PKICRL00v Description: The Online Responder Service encountered an error while submitting the enrollment request for configuration inter00 to certification authority PKIINTER00v\PKIINTER00V. The request ID is 0.(The system cannot find the file specified. 0x80070002 (WIN32: 2 ERROR_FILE_NOT_FOUND))
OCSP Solution
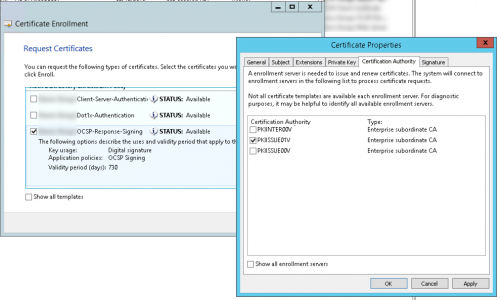
I quickly ascertained that removing and adding the nodes, didn’t fix the problem. On the OCSP server, launch an MMC session, and add in the Certificates snap-in for local computer. Do a manual enrolment, but in the details, set the issuing CA to one of the CA’s that is displaying an error, (using the OCSP Responder certificate template). Repeat for each CA.
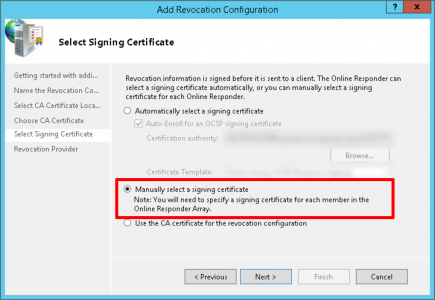
Now add each node, but choose ‘manually select a signing certificate’.
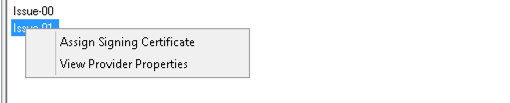
Then assign the certificate, and choose the correct cert for each node.
Related Articles, References, Credits, or External Links
NA