KB ID 000116
Problem
The one reason I prefer Cisco over Microsoft is they rarely change things, you learn how to do something and it’s learned. This is the second time have had to write this article purely because the Azure UI has changed!
Virtual Network Gateway Options
With VPN’s into Azure you connect to a Virtual Network Gateway, of which there are TWO types Policy Based, and Route Based. This article will deal with Policy Based, for the more modern Route based option, see the following link;
Microsoft Azure ‘Route Based’ VPN to Cisco ASA
Policy Based
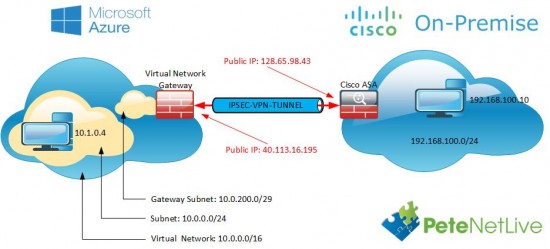
These came first, essentially they work like this, “If traffic is destined for remote network (x) then send the traffic ‘encrypted’ to local security gateway (y).” Note: Where Local Security Gateway is a firewall at YOUR site, NOT in Azure! This is the way traditionally VPNs have been done in Cisco ASA, In Cisco Firewall speak it’s the same as “If traffic matches the interesting traffic ACL, then send the traffic ‘encrypted’ to the IP address specified in the crypto map”.
Advantages:
- Can be used on older Cisco Firewalls (ASA 5505, 5510, 5520, 5550, 5585).
- Can be used on newer Cisco Firewalls (ASA 5506-x, 5508-X, 5512-x, 5515-x, 5516-x, 5525-X, 5545-X, 5555-x, 5585-X)
- Can be used with Cisco ASA OS (pre 8.4) IKEv1 only,
Disadvantages
- Can only be used for ONE connection from your Azure Subnet to your local subnet. Note: You could ‘hairpin’ multiple sites over this one tunnel, but that’s not ideal.
Route Based
These were typically used with routers, because routers use Virtual Tunnel Interfaces to terminate VPN tunnels, that way traffic can be routed down various different tunnels based on a destination, (which can be looked up in a routing table). But Cisco ASA now supports Virtual Tunnels Interfaces (After version 9.7(1))
Advantages
- Can be used for VPNs to multiple sites.
Disadvantages
- Requires Cisco ASA OS 9.7(1) So no ASA 5505, 5510, 5520, 5550, 5585 firewalls can use this.
Configure Azure for ‘Policy Based’ IPSec Site to Site VPN
You may already have Resource Groups and Virtual Networks setup, if so you can skip the first few steps.
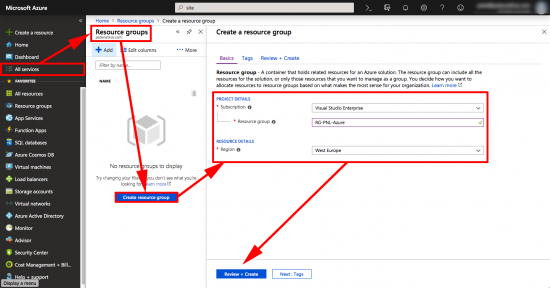
Sign int0 Azure > All Services > Resource Groups > Create Resource Group > Give your Resource Group a name, and select a location > Create.
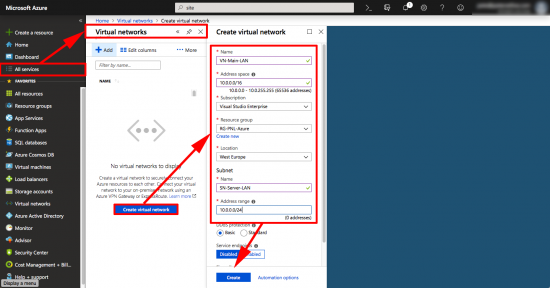
OK, if you’re used to networking this can be a little confusing, we are going to create a virtual network, and in it we are going to put a virtual subnet, (yes I know this is odd, bear with me!) It’s the ‘Subnet Name ‘and ‘address range‘ that things will actually connect to, (10.0.0.0/24).
All Services > Virtual Networks > Create Virtual Network > Give the Virtual Network a name, a subnet, select your resource group > Then create a Subnet, give it a name and a subnet > Create.
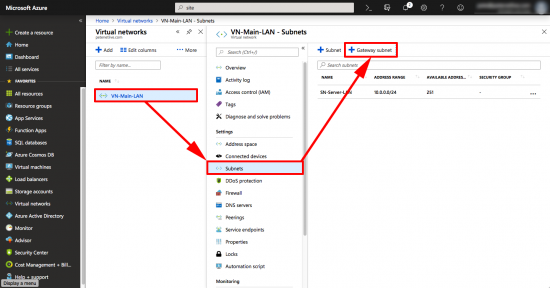
To further confuse all the network engineers, we now need to add another subnet, this one will be used by the ‘gateway’. If you are a ‘networking type’ it’s part of the virtual network, but is more specific than the subnet you already created.
With your virtual network selected >Subnets > +Gateway Subnet.
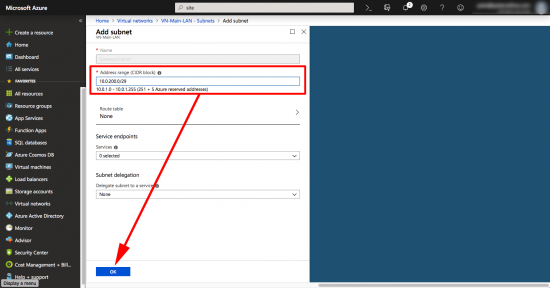
You can’t change the name, (you could before, then it wouldn’t work, which was strange, but I suppose it’s fixed now) > put in another network that’s part of the Virtual-Network, but does not overlap with the subnet you created in the previous step > OK.
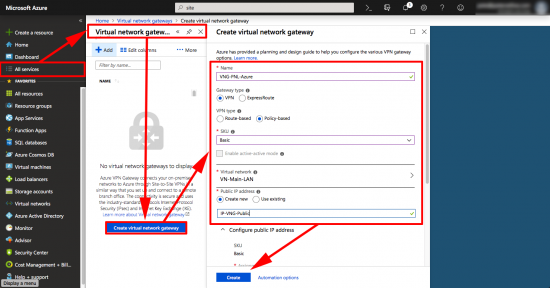
All Services > Virtual Network Gateways > Create Virtual Network Gateway > Name it > Policy Based (Note: This will change the SKU to Basic) > Create New Public IP > Give it a Name > Create.
Note: This will take a while, go and put the kettle on! Make sure all running tasks and deployments are complete before continuing.
You can do the next two steps together, but I prefer to do then separately, or it will error if the first one does not complete!
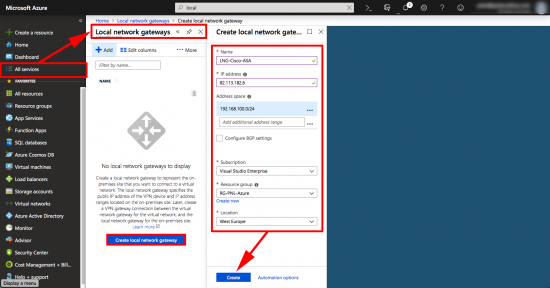
Now you need to create a Local Security Gateway. (To represent your Cisco ASA). All Services > Local Security Gateway > Create Local Security Gateway > Name it > Supply the public IP > Supply the Subnet(s) ‘behind’ the ASA > Select your Resource Group > Create.
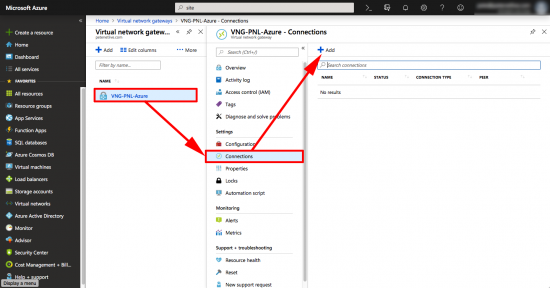
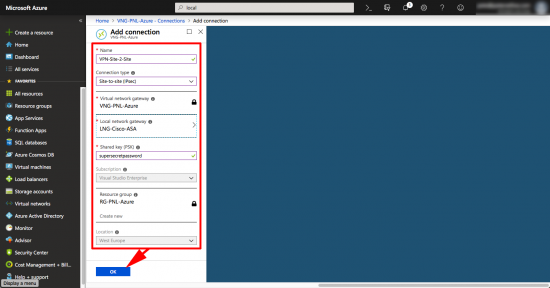
Finally create the VPN > Select your Virtual Network Gateway > Connections > Add.
Give the tunnel a name > Site-to-Site IPSec > Select your Local Network Gateway (ASA) > Create a pre-shared-key (you will need this for the ASA config!) > Select your Resource Group > OK.
Configure the Cisco ASA for ‘Policy Based’ Azure VPN
I read somewhere that the ASA had to be at 9.1? That’s not true, I’ve done it with a firewall running 8.3, and I’ve read blog posts from people who have done this with a Cisco PIX (running version 6). But the firewall does have to support AES encryption (‘show version’ will tell you). There are some subtle differences in the code which I will point out below, but essentially you should be running an OS newer than 8.4 for this config to work. (As I’ve said I’ll address 8.4, and 8.3 (or earlier) below).
Connect to the ASA and create an object group for your local subnet, and the subnet that you are using in Azure, (Called Azure-SN above).
Type help or '?' for a list of available commands. Petes-ASA> enable Password: ******** Petes-ASA# configure terminal Petes-ASA(config)# object-group network OBJ-AZURE-SN Petes-ASA(config-network-object-group)# description Azure Subnet Petes-ASA(config-network-object-group)# network-object 10.0.0.0 255.255.255.0 Petes-ASA(config-network-object-group)# exit Petes-ASA(config)# object-group network OBJ-LOCAL-SN Petes-ASA(config-network-object-group)# description Local Subnet Petes-ASA(config-network-object-group)# network-object 192.168.100.0 255.255.255.0 Petes-ASA(config-network-object-group)# exit
Then create an access-list, this will alert the firewall that there is some ‘interesting traffic’ that needs to be encrypted (we will call this ACL later on, from the crypto-map). Then create a NAT rule that stops traffic that’s going over the VPN tunnel from being NATTED.
Petes-ASA(config)# access-list ACL-AZURE-VPN extended permit ip object-group OBJ-LOCAL-SN object-group OBJ-AZURE-SN Petes-ASA(config)# nat (inside,outside) 1 source static OBJ-LOCAL-SN OBJ-LOCAL-SN destination static OBJ-AZURE-SN OBJ-AZURE-SN no-proxy-arp route-lookup
Our VPN is going to use a pre-shared-key, (you created in Azure above). It will use AES-256 for encryption, SHA for hashing, and Diffie Hellman version 2 for key exchange. So we need to have a matching ‘phase 1’ (that’s ISAKMP) policy.
Petes-ASA(config)# crypto ikev1 policy 5 Petes-ASA(config-ikev1-policy)# authentication pre-share Petes-ASA(config-ikev1-policy)# encryption aes-256 Petes-ASA(config-ikev1-policy)# hash sha Petes-ASA(config-ikev1-policy)# group 2 Petes-ASA(config-ikev1-policy)# lifetime 28800 Petes-ASA(config-ikev1-policy)# exit
Enable ISAKMP (version 1) on the outside interface, then configure the parameters that will be used in ‘phase 2’ (that’s IPSEC). Note: If your outside interface is called something else like Outside or WAN substitute that!
Petes-ASA(config)# crypto ikev1 enable outside Petes-ASA(config)# crypto ipsec ikev1 transform-set AZURE-TRANSFORM esp-aes-256 esp-sha-hmac Petes-ASA(config)# crypto ipsec security-association lifetime seconds 3600 Petes-ASA(config)# crypto ipsec security-association lifetime kilobytes 102400000
Next, you need a tunnel-group, in this case the only job of the tunnel group has is to keep the pre-shared-key (PSK) to the peer you specify. Which in this case is the Azure Gateway.
Petes-ASA(config)# tunnel-group 40.113.16.195 type ipsec-l2l Petes-ASA(config)# tunnel-group 40.113.16.195 ipsec-attribute Petes-ASA(config-tunnel-ipsec)# ikev1 pre-shared-key supersecretpassword Petes-ASA(config-tunnel-ipsec)# exit
The thing that ties it all together is the crypto map. Here I’ve called it “AZURE-CRYPTO-MAP”, WARNING if you already have a crypto map, use the name of that one, or all your existing VPNS will stop working, (show run crypto will tell you). This is because, you can only have one crypto map applied to an interface, but you can have many crypto map numbers, i.e crypto map {NAME} {NUMBER} {COMMAND}. And each VPN tunnel has its own number.
Petes-ASA(config)# crypto map AZURE-CRYPTO-MAP 1 match address ACL-AZURE-VPN Petes-ASA(config)# crypto map AZURE-CRYPTO-MAP 1 set peer 40.113.16.195 Petes-ASA(config)# crypto map AZURE-CRYPTO-MAP 1 set ikev1 transform-set AZURE-TRANSFORM Petes-ASA(config)# crypto map AZURE-CRYPTO-MAP interface outside
There are a couple of extra commands you will need, these are sysops commands. Their purpose set things globally, and are generally hidden from the config, (i.e ‘show run’ wont show them). These are recommendations from Azure. The first one drops the maximum segment size to 1350.The second command keeps the TCP session information even if the VPN tunnel drops.
Petes-ASA(config)# sysopt connection tcpmss 1350 Petes-ASA(config)# sysopt connection preserve-vpn-flows Petes-ASA(config)# exit
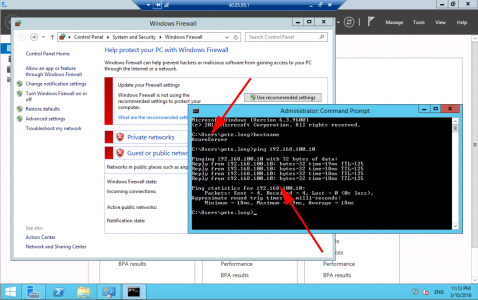
Testing Azure to Cisco ASA VPN
To test we usually use ‘ping’, the problem with that is, if you are using Windows Servers they will have their Windows firewall on by default, which blocks pings, (bear this in mind when testing). Also your ASA needs to be setup to allow pings, (try pinging 8.8.8.8 that usually responds), if yours doesn’t then configure your ASA to allow ping traffic.
As mentioned above, you might want to turn the firewalls off to test.
On the Cisco ASA you can see the tunnel is established at Phase 1 (ISAKMP)
Petes-ASA# show cry isa IKEv1 SAs: Active SA: 1 Rekey SA: 0 (A tunnel will report 1 Active and 1 Rekey SA during rekey) Total IKE SA: 1 1 IKE Peer: 40.113.16.195 Type : L2L Role : initiator Rekey : no State : MM_ACTIVE
If yours says something else, (or nothing at all) then phase 1 has not established. You need to Troubleshoot phase 1 of the VPN tunnel. (Probably: Public IP is wrong, or pre-shared-key (shared secret) has been mistyped, check these first).
Assuming that’s working, your next test is to make sure that Phase 2 has established. You should see packets encrypting and decrypting.
Petes-ASA(config)# show cry ipsec sa
interface: outside
Crypto map tag: AZURE-CRYPTO-MAP, seq num: 1, local addr: 128.65.98.43
access-list ACL-AZURE-VPN extended permit ip 192.168.100.0 255.255.255.0 10.0.0.0 255.255.255.0
local ident (addr/mask/prot/port): (192.168.100.0/255.255.255.0/0/0)
remote ident (addr/mask/prot/port): (10.0.0.0/255.255.255.0/0/0)
current_peer: 40.113.16.195
#pkts encaps: 2, #pkts encrypt: 2, #pkts digest: 2
#pkts decaps: 3, #pkts decrypt: 3, #pkts verify: 3
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 2, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 128.65.98.43/0, remote crypto endpt.: 40.113.16.195/0
path mtu 1500, ipsec overhead 74(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabled
current outbound spi: 97624DA8
current inbound spi : D7705547
inbound esp sas:
spi: 0xD7705547 (3614463303)
transform: esp-aes-256 esp-sha-hmac no compression
in use settings ={L2L, Tunnel, IKEv1, }
slot: 0, conn_id: 335872, crypto-map: AZURE-CRYPTO-MAP
sa timing: remaining key lifetime (kB/sec): (97199999/3556)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x0000000F
outbound esp sas:
spi: 0x97624DA8 (2539802024)
transform: esp-aes-256 esp-sha-hmac no compression
in use settings ={L2L, Tunnel, IKEv1, }
slot: 0, conn_id: 335872, crypto-map: AZURE-CRYPTO-MAP
sa timing: remaining key lifetime (kB/sec): (97199999/3556)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
Petes-ASA(config)#
Azure to Cisco VPN ‘Policy Based’ IKEv1 Complete Code Snippets to Copy and Paste
(Change the values highlighted in red) WARNING: re-read the warning about crypto map names above!
VERSION 8.4 AND NEWER ! object-group network OBJ-AZURE-SN description Azure Subnet network-object 10.0.0.0 255.255.255.0 exit object-group network OBJ-LOCAL-SN description Local Subnet network-object 192.168.100.0 255.255.255.0 exit ! access-list ACL-AZURE-VPN extended permit ip object-group OBJ-LOCAL-SN object-group OBJ-AZURE-SN ! nat (inside,outside) 1 source static OBJ-LOCAL-SN OBJ-LOCAL-SN destination static OBJ-AZURE-SN OBJ-AZURE-SN ! crypto ikev1 policy 5 authentication pre-share encryption aes-256 hash sha group 2 lifetime 28800 ! crypto ikev1 enable outside ! crypto ipsec ikev1 transform-set AZURE-TRANSFORM esp-aes-256 esp-sha-hmac crypto ipsec security-association lifetime seconds 3600 crypto ipsec security-association lifetime kilobytes 102400000 ! tunnel-group 40.113.16.195 type ipsec-l2l tunnel-group 40.113.16.195 ipsec-attribute ikev1 pre-shared-key 1234567890asdfg ! crypto map AZURE-CRYPTO-MAP 1 match address ACL-AZURE-VPN crypto map AZURE-CRYPTO-MAP 1 set peer 40.113.16.195 crypto map AZURE-CRYPTO-MAP 1 set ikev1 transform-set AZURE-TRANSFORM ! crypto map AZURE-CRYPTO-MAP interface outside ! sysopt connection tcpmss 1350 ! sysopt connection preserve-vpn-flows VERSION 8.4 (BEFORE IKEv2 WAS INTRODUCED) ! object-group network OBJ-AZURE-SN description Azure Subnet network-object 10.0.0.0 255.255.255.0 exit object-group network OBJ-LOCAL-SN description Local Subnet network-object 192.168.100.0 255.255.255.0 exit ! access-list ACL-AZURE-VPN extended permit ip object-group OBJ-LOCAL-SN object-group OBJ-AZURE-SN ! nat (inside,outside) 1 source static OBJ-LOCAL-SN OBJ-LOCAL-SN destination static OBJ-AZURE-SN OBJ-AZURE-SN ! crypto isakmp policy 5 authentication pre-share encryption aes-256 hash sha group 2 lifetime 28800 ! crypto isakmp enable outside ! crypto ipsec transform-set AZURE-TRANSFORM esp-aes-256 esp-sha-hmac crypto ipsec security-association lifetime seconds 3600 crypto ipsec security-association lifetime kilobytes 102400000 ! tunnel-group 40.113.16.195 type ipsec-l2l tunnel-group 40.113.16.195 ipsec-attribute pre-shared-key 1234567890asdfg ! crypto map AZURE-CRYPTO-MAP 1 match address ACL-AZURE-VPN crypto map AZURE-CRYPTO-MAP 1 set peer 40.113.16.195 crypto map AZURE-CRYPTO-MAP 1 set ikev1 transform-set AZURE-TRANSFORM ! crypto map AZURE-CRYPTO-MAP interface outside ! sysopt connection tcpmss 1350 ! sysopt connection preserve-vpn-flows OLDER THAN VERSION 8.3 (BEFORE NAT SYNTAX CHANGED) ! name 10.0.0.0 OBJ-AZURE-SN name 192.168.100.0 OBJ-LOCAL-SN ! access-list ACL-AZURE-VPN extended permit ip OBJ-LOCAL-SN 255.255.255.0 OBJ-AZURE-SN 255.255.0.0 ! access-list NO-NAT-TRAFFIC extended permit ip OBJ-LOCAL-SN 255.255.255.0 OBJ-AZURE-SN 255.255.0.0 nat (inside) 0 access-list NO-NAT-TRAFFIC ! crypto isakmp policy 5 authentication pre-share encryption aes-256 hash sha group 2 lifetime 28800 ! crypto isakmp enable outside ! crypto ipsec transform-set AZURE-TRANSFORM esp-aes-256 esp-sha-hmac crypto ipsec security-association lifetime seconds 3600 crypto ipsec security-association lifetime kilobytes 102400000 ! tunnel-group 40.113.16.195 type ipsec-l2l tunnel-group 40.113.16.195 ipsec-attribute pre-shared-key 1234567890asdfg ! crypto map AZURE-CRYPTO-MAP 1 match address ACL-AZURE-VPN crypto map AZURE-CRYPTO-MAP 1 set peer 40.113.16.195 crypto map AZURE-CRYPTO-MAP 1 set transform-set AZURE-TRANSFORM ! crypto map AZURE-CRYPTO-MAP interface outside ! sysopt connection tcpmss 1350 ! sysopt connection preserve-vpn-flows
Related Articles, References, Credits, or External Links
Microsoft Azure To Cisco ISR Router Site to Site VPN
Azure to Cisco VPN – ‘Failed to allocate PSH from platform’

19/05/2016
So I’m trying to mentally get over this configuration hurdle that we have with EIGRP at the L3 core and the ASA hosting the VPN connection to Azure. All your instructions above are fine, just the route redistribution into the L3 core is causing me issues >.>
I can see the redistr’d route in the L3 core, but the pkts coming from Azure don’t go back out. I can see traffic coming back in from Azure and decrypting, but there’s no encryption to be seen. Any thoughts?
19/05/2016
Hi,
So the traffic from Azure is decrypting, you can see this on ‘show cry ipse sa’? But no traffic is going back to Azure from your LAN (the Decrypting packets in the same display is not incrementing?)
Are you reverse route injecting the Azure subnet? You say you can see this route on the core? If so check your ACL and NAT policies on the ASA, make sure the static nat has a route-lookup on the end of it.
24/07/2016
Hi! All clear as usual )
And what’s about if my Radius/Syslog/CRL server is on outside interface? For ASA-ASA L2L I need to add additional line to crypto map (azure-vpn-acl) but not with Azure… Any ideas ?
25/07/2016
Are they physically outside the ASA of just presented to the outside world from inside/DMZ?
05/10/2016
Pete,
Thank you for the documentation. I’ve been able to get everything setup as expected, but if I set the mask on my ASA (obj-Azure-sn)to 255.255.255.0, The tunnel says I have no matching crypto map entry for remote proxy 172.5.0.0/255.255.0.0).
If I set the Mask to 255.255.0.0 The tunnel comes up, but is unable to pass traffic between sites. I could not use the 10.0.0.0 network as we have other traffic on it. We use 172.16.x.x for LAN, so I figured I could use 172.5.x.x, but this could have been my fatal error. Sub-netting is not in my wheelhouse.
Thanks for any and all help in advance.
06/10/2016
Hi,
Without seeing the config, its hard to comment, if you do a ‘show run crypto’ it show show you the ACL its matching. You may need to take the tunnel offline then make the change, then bring the tunnel back up!
Pete
14/11/2016
hi pete, is it work also if version ASA is 8.2?
14/11/2016
Yes providing you use the pre 8.3 version at the bottom of the page.
Pete
17/11/2016
What happens if you configure IKEv2 with the Azure gateway?
18/11/2016
Hi Tim,
I’ve not tried IKEv2, all the examples given by M$ specify IKEv1. If you wanted to try you, would not need to specify it as a policy, the enable it on the outside interface and create a V2 transform set.
Pete
22/11/2016
Hi Pete,
Great guide! Have you ever seen issues initiating the VPN from Azure > ASA? I recently configured an Azure VPN connection where I only have control of the ASA configuration. Simply put the tunnel comes up regardless of initiation but when trying from Azure > ASA traffic will not passing. When pinging in the other direction (ASA > Azure) it comes up immediately and passes traffic in both direction.
It has me totally puzzled as to why this would be.
Cheers,
John
22/11/2016
Hi John,
One way initiation: I usually see with older versions of the ASA code, or if you managed to enable PFS on one end, then I’ve seen that happen before.
Pete
20/01/2017
@John,
The same is being observed on our first time setup (s2s VPN tunnel) between a Cisco ASA and Azure. Traffic passes through successfully when initiated from hosts residing behind the Cisco ASA but not when connection is started from hosts within the Azure. Did you manage to get through this challenge? On our side we have a Cisco ASA 5516-X.
@PeteLong,
Will the sysopt tcpmss parameter set to 1300 create any issues considering the requirements are to clamp it at 1350 ? No PFS have been enabled on this side so still need to find the root cause
I appreciate your comments in advance.
Regards
Stefan
20/01/2017
Hi Stefan,
I cant see any issues in dropping the segment size to 1300, With some internet carriers in the UK (BT FTTC) I’ve had to do similar things in the past. And of course if the tunnel stutters it’s pretty easy to reverse 🙂
Interested to see John’s reply about the one way initiation though?
P
20/10/2017
Hi Stefan, I have the same issue with an ASA
“Traffic passes through successfully when initiated from hosts residing behind the Cisco ASA but not when connection is started from hosts within the Azure.”
Any solution to this issue at this time?
Tahnks.
Jesus
16/02/2017
Hi Pete,
If I run the sysopt command on my ASA 5510 version 8.2 will that affect my other site-to-site vpn connections? Thanks.
18/02/2017
Yes its a global command, so next time the other tunnels establish they will have a smaller segment size, I’ve not seen that break a tunnel though 🙂
P
03/06/2017
If i have a Cisco Asa connected to a Virtual Azure network sa 10.0.0.0 / 16 and the server net in the azure cloud is 10.0.0.0/24 and then i have a second Virtual Network on a other Resource group in azure, with 10.1.0.0/24 peered to the 10.0.0.0/24 network.
The connection between my azure networks works just fine, it cant send packedes both ways, but my local network connected to the Asa 192.168.0.0/24 can only send traffic to the 10.0.0.0/16 network and only reach the 10.0.0.0/24 subnet.
Due to the configuration of the site-to-site vpn.. How the hell do i make the Asa to route the traffic through the tunnel.?
If i send a static route the tunnel wont allow it due to the IPSEC krytpo..
03/06/2017
10.1.0.0/24 is a completely different subnet range? if you wanted to add it to the same VPN tunnels then you would need to add that network to the cryptomap ACL as a second ACE entry, and add a second NAT exemption for the second network;
Petes-ASA(config)# object-group network OBJ-AZURE-SN-2
Petes-ASA(config-network-object-group)# description Azure Subnet
Petes-ASA(config-network-object-group)# network-object 10.1.0.0 255.255.255.0
Petes-ASA(config-network-object-group)# exit
Petes-ASA(config)# access-list ACL-AZURE-VPN extended permit ip object-group OBJ-LOCAL-SN object-group OBJ-AZURE-SN-2
Petes-ASA(config)# nat (inside,outside) 1 source static OBJ-LOCAL-SN OBJ-LOCAL-SN destination static OBJ-AZURE-SN-2 OBJ-AZURE-SN-2 no-proxy-arp route-lookup
Pete
28/09/2017
You might also want to disable iisakmp keepalives as Azure dont’tsupport it. So add in the tunnel group to Azure, tunnel-group “namee# ipsec-attributes, isakmp keepalive disable.
/Per
10/04/2018
Never worked for me even use IKEV2! I am not sure because of ASA 5510 or Firmware Version 9.1?!
11/04/2018
IVEV2 was introduced in v 8.4 (if memory serves).
04/06/2018
Great article as always Pete! Any IKEv2 love?
It appears that when attempting IKEv2 configurations received via Azure’s VPN Device Script https://docs.microsoft.com/en-us/azure/vpn-gateway/vpn-gateway-download-vpndevicescript
The output file defaults to “Policy Based” which translates to IKEv1 crypto map as shown above.
However, the fun seems to begin when the ASA [5545 in my case] requires min 9.9.x code to perform connections via IKEv2 virtual tunnel interface – MS “Route Based” vpn.
Just sharing the wealth hoping this may stop some potential headaches for some folks.
13/08/2018
It looks like the ASA-to-Azure VPN can now use route based configuration on the ASA. This involves using a tunnel interface. It all seems pretty simple so far. I’m only wondering what the point of the IP address on the tunnel interface is… I’m assuming it is just needed for the interface to be up/up as I don’t see any other configuration that even refers to it and my tunnel is up.
15/08/2018
Its just an IPv4 address for the virtual tunnel interface 🙂
31/10/2018
Just ran the “VERSION 8.4 AND NEWER” config on an 5550 and confirmed it is still working with Azure.
31/10/2018
Thanks for the feedback.
18/02/2019
Still working in 2019 🙂
09/04/2019
OLDER THAN VERSION 8.3 (BEFORE NAT SYNTAX CHANGED)
I’m trying to setup using your provided configuration and not getting very far.
I’m assuming Older than version 8.3 would be 8.2 but I can’t get the ASA to accept the following command.
crypto map AZURE-CRYPTO-MAP 1 set ikev1 transform-set AZURE-TRANSFORM
It doesn’t understand ikev1.
Thoughts on how to get around this issue?
13/04/2019
Ooh, Typo ThankQ. I’ve changed the article accordingly – simply use ‘crypto map AZURE-CRYPTO-MAP 1 set transform-set AZURE-TRANSFORM’ The older ASA does not know what ikev1 and ikev2 are!
09/12/2019
Thanks Pete!
Excellent tutorial!!!!
This worked great for our Cisco ASA running 9.1
(Even though the Azure interface has already changed slightly… AGAIN)
The only issue I have now is that once the VPN connection times out, if I initiate a connection from within Azure, it does not reestablish the VPN connection. So I end up having to ping something from the office LAN to the Azure virtual network to get the VPN connection to come back up.
Wondering if you or anyone else has had the same experience.
Thanks again
02/06/2020
Standing ovation to you, and this post. Amazing detail on the troubleshooting section!!!
Thank you 🙂
03/06/2020
Cheers Pablo!
05/06/2020
Perfect…works perfect June 2020. Thanks for the help with this magical setup.
25/09/2020
Thank you for confirming that Azure Networking has nothing to do with the networking we all know. I can stop banging my head now.
This worked for me on an ASA now going to do it on an MX.
9-25-2020
08/06/2021
Excellent post Pete! I’m trying to get this work with a Cisco NGFW and not getting it to work. Any tips you can recommend?
09/06/2021
I’m still running FirePower with ASA code on it!
21/06/2021
Hello,
We have Asa 5525, the remote side says that we have to use traffic selector 0.0.0.0/0 for both side as the VPN tunnel is a route-based!
Our asa has already launched several site-to-site and sslvpn cisco any connect.
Can this be configured so that other VPN connections are not affected? When we install crypto map with acl any-any cisco anyconnect cannot connect to server.
Thank you!
01/10/2021
Hi Pete,
I am able to initiate comminucation from Azure to On Prem, but any communication initated from On Prem fails. What could be the issue
19/05/2022
Hello Pete,
I need help with respect to interesting traffic subnets in Azure, We are only allowed to user Public IPs as in encryption domain(interesting traffic ACL subnets).
Could you please help to suggest how can one use NAT at Azure end and then can allow NAT IP inside the interesting traffic ACL.
Azure end IP details
Peer IP: 52.10.5.6
Enc IP: 52.20.6.7
Cisco end IP details
Peer IP: 152.147.204.67
Enc IP: 152.147.204.70
VPN must be Policy based
07/05/2025
Been trying to get this to work. I have a successful ikev2 IPsec tunnel up and connecting. I can ping from on prem to azure. But I can’t initiate traffic from azure to onprem. My nat statement has route lookup on it. Packet tracer doesn’t seem to work when source is azure to destination on prem due to acl drop, I assume because something to do with encryption in the tunnel coming from azure hitting the outside interface? Not sure really. Is there something you need to do on azure side to say send traffic down the tunnel? Or a nat exempt like we do on ASA?