KB ID 0001052
Problem
By default the Cisco ASA will allow connection via SSLv3. The POODLE exploit works by forcing SSL to fall back to SSLv3 and then decrypting that communication. However you are still not completely protected as per this Threat Validation, so the ASA platform can still be attacked via TLSv1.0. Note: At time of writing TLSv1.2 is not supported, but it is on the road-map for version 9.3(2).
So this procedure will not completely eliminate the threat, but it’s as mitigated as it’s possible to be at this time, (And TLSv1 is considered more secure than SSLv3 anyway).
Solution
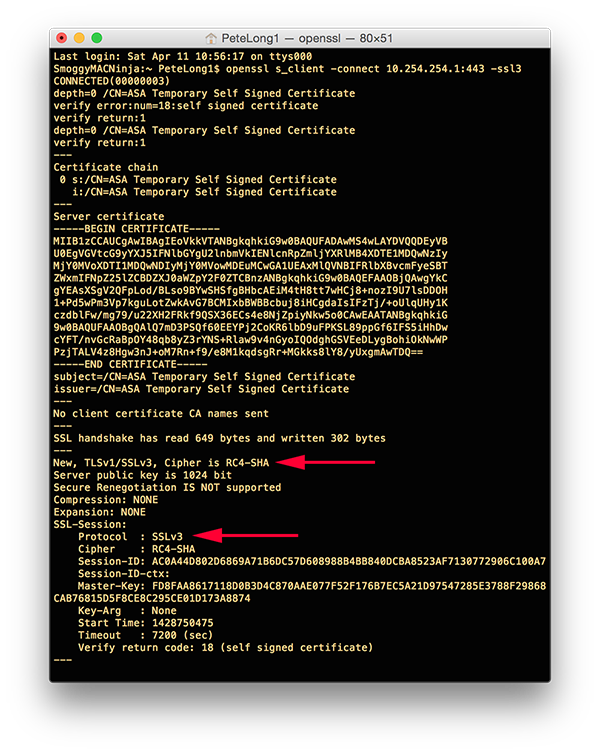
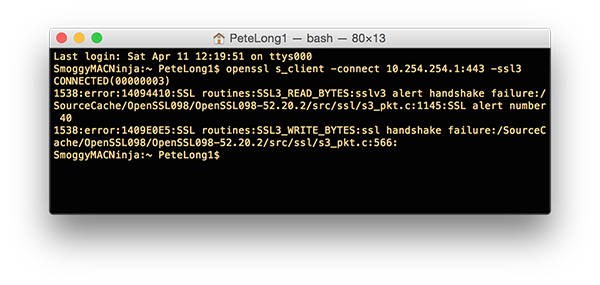
1. You can check your firewall is contactable via SSLv3, here I’m on MAC OSX and I’ve got OpenSSL installed. If I try to initiate an SSLv3 connection it works.
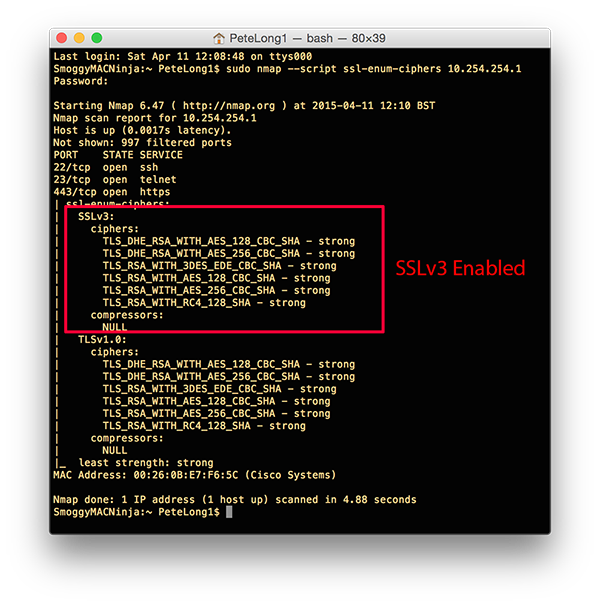
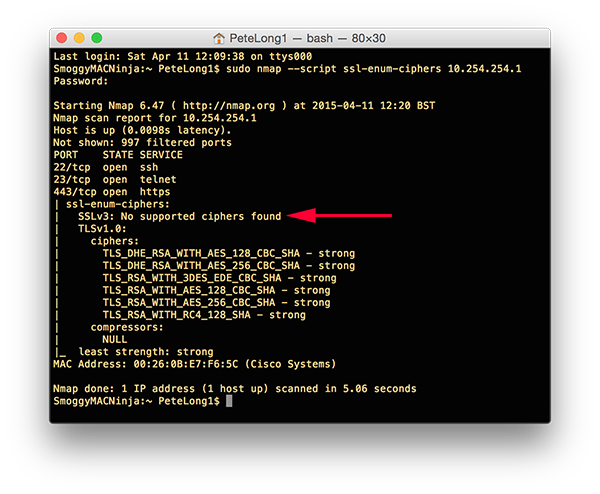
Or if you have nmap installed you can use that as well;
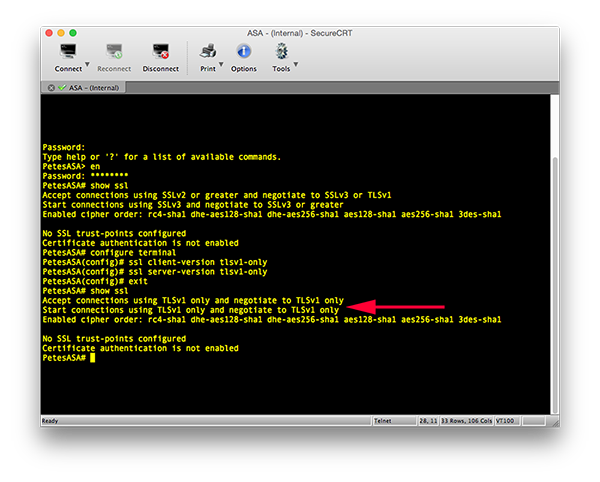
2. Below you can see I’m confirming the SSL settings (i.e. it will accept SSLv3). Then I force the firewall to only accept TLSv1.0.
Petes-ASA# configure terminal Petes-ASA(config)# ssl client-version tlsv1-only Petes-ASA(config)# ssl server-version tlsv1-only
You can see, afterwards when I view the SSL options, only TLSv1 will be accepted.
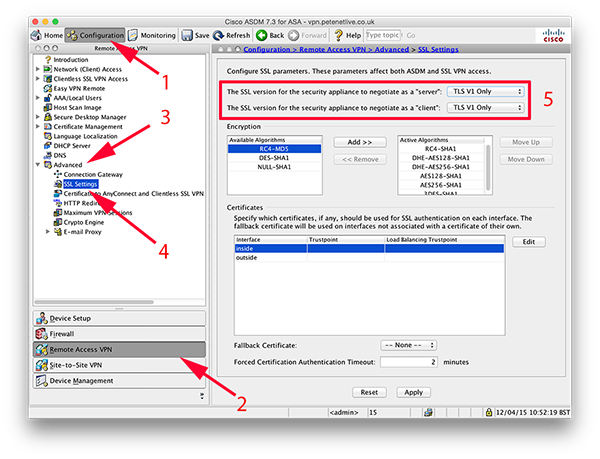
3. If you prefer to use the ADSM, then you will find the same settings at, Configuration > Remote Access VPN > Advanced > SSL Settings;
The SSL version for the security appliance to negotiate as a ‘server’ = TLS V1 Only
The SSL version for the security appliance to negotiate as a ‘client’ = TLS V1 Only
4. Don’t forget to ‘Apply’ and then save the changes.
Cisco ASA Testing for SSLv3
Simply perform the tests that I did above;
1. Proving the absence of SSLv3 with OpenSSL.
2. Proving the absence of SSLv3 with nmap.
Related Articles, References, Credits, or External Links
NA