KB ID 0001034
Problem
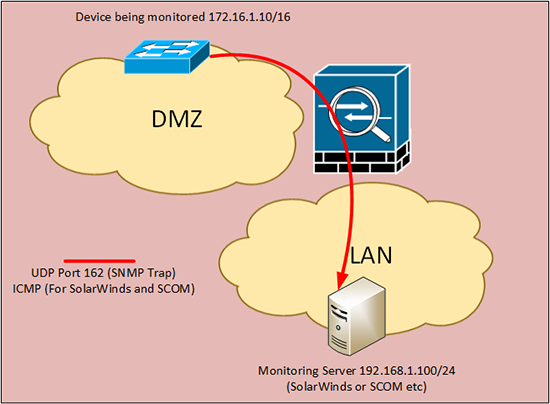
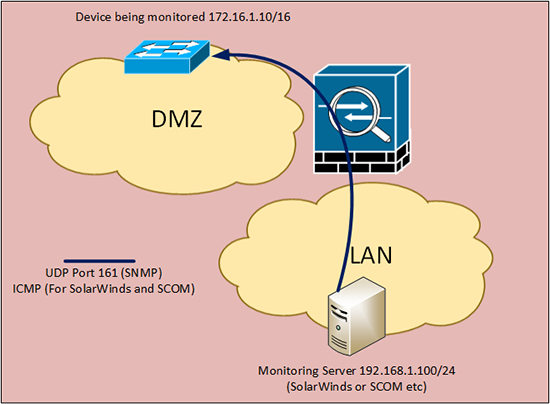
Had a requirement to let SNMP traffic though a firewall this week, I have a client that has both SolarWinds and SCOM, and they need to monitor the external Citrix ADC load balancers. For SNMP we simply need UDP ports 161 and 162 (See below) but SolarWinds maintains ‘ping’ connectivity to the monitored assets, so ICMP also needs to be open.
Inbound Ports
Outbound Ports
Solution
As my ‘weapon of choice’ is a Cisco ASA, here’s how to set it up.
1. Connect to the firewall and proceed to global configuration mode.
Password:******* Type help or ‘?’ for a list of available commands. Petes-ASA> enable Password: ******** Petes-ASA# configure terminal Petes-ASA(config)#
2. Assuming my inside interface is called ‘inside’ allow the traffic outbound then apply that ACL to the firewall with an access-group command.
Cisco ASA – ‘access-group’ Warning
3. Assuming my outside interface is called ‘outside’ allow the traffic inbound then apply that ACL to the firewall with an access-group command.
Cisco ASA – ‘access-group’ Warning
Note: Simply allowing ICMP will not permit ‘ping’ see the following article;
4. Save the changes.
Also
You may want to open UDP 514 (syslog) from the device to the monitoring server, (assuming you have configured syslog on the monitored device). If the monitored device cannot communicate make sure it’s not using DNS to resolve the monitoring server (if so you may need to open UDP 53 to a DNS server).
Related Articles, References, Credits, or External Links
NA