KB ID 0001000
Problem
My colleague had to set this up on the test bench today, and it looked infinitely more interesting that what I was doing, so I grabbed my console cable, and offered to ‘help’.
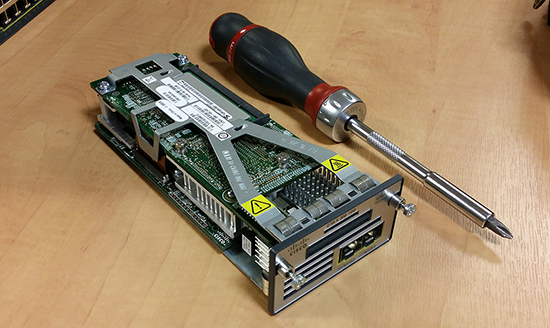
This was done on two Cisco Catalyst 3560-X switches, each with a 10G Service Module (C3KX-SM-10G), and 1Gb SFP modules (Note: Not 10Gb ones, this will become important later).
Solution
1. First hurdle was, when we tried to add the first command to the interface ‘cts man’ it would not accept the command, you need to make sure you are running either IP Base, or the IP Services feature set.
Note: We are running the universal IOS image this allows us to do the following;
Switch(config)#license boot level ipbase PLEASE READ THE FOLLOWING TERMS CAREFULLY. INSTALLING THE LICENSE OR LICENSE KEY PROVIDED FOR ANY CISCO PRODUCT FEATURE OR USING SUCH PRODUCT FEATURE CONSTITUTES YOUR FULL ACCEPTANCE OF THE FOLLOWING TERMS. YOU MUST NOT PROCEED FURTHER IF YOU ARE NOT WILLING TO BE BOUND BY ALL THE TERMS SET FORTH HEREIN. You hereby acknowledge and agree that the product feature license is terminable and that the product feature enabled by such license may be shut down or terminated by Cisco after expiration of the applicable term of the license (e.g., 30-day trial period). Cisco reserves the right to terminate or shut down any such product feature electronically or by any other means available. While alerts or such messages may be provided, it is your sole responsibility to monitor your terminable usage of any product feature enabled by the license and to ensure that your systems and networks are prepared for the shut down of the product feature. You acknowledge and agree that Cisco will not have any liability whatsoever for any damages, including, but not limited to, direct, indirect, special, or consequential damages related to any product feature being shutdown or terminated. By clicking the "accept" button or typing "yes" you are indicating you have read and agree to be bound by all the terms provided herein. ACCEPT? (yes/[no]): yes Switch(config)# Mar 30 01:43:18.513: %IOS_LICENSE_IMAGE_APPLICATION-6-LICENSE_LEVEL: Module name = c3560x Next reboot level = ipbase and License = ipbase
Then reload the switch.
2. Then this jumped up and bit us;
Mar 30 01:32:07.400: %CTS-6-PORT_UNAUTHORIZED: Port unauthorized for int(Te1/1) Mar 30 01:32:19.379: %PLATFORM_SM10G-3-SW_VERSION_MISMATCH: The FRULink 10G Service Module (C3KX-SM-10G) in switch 1 has a software version that is incompatible with the IOS software version. Please update the software. Module is in pass-thru mode.
3. If you issue the following command, you can see the difference (highlighted).
Switch#show switch service-modules
Switch/Stack supports service module CPU version: 03.00.76
Temperature CPU
Switch# H/W Status (CPU/FPGA) CPU Link Version
-----------------------------------------------------------------
1 OK 41C/47C ver-mismatch 03.00.41
Switch#4. So a quick download from Cisco later, with the file on a FAT32 formatted USB drive.
Switch#archive download-sw usbflash0:/c3kx-sm10g-tar.150-2.SE6.tar
examining image...
extracting info (100 bytes)
extracting c3kx-sm10g-mz.150-2.SE6/info (499 bytes)
extracting info (100 bytes)
System Type: 0x00010002
Ios Image File Size: 0x017BDA00
Total Image File Size: 0x017BDA00
Minimum Dram required: 0x08000000
Image Suffix: sm10g-150-2.SE6
Image Directory: c3kx-sm10g-mz.150-2.SE6
Image Name: c3kx-sm10g-mz.150-2.SE6.bin
Image Feature: IP|LAYER_3|MIN_DRAM_MEG=128
FRU Module Version: 03.00.76
Updating FRU Module on switch 1...
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!
!!!!!!!!!!!!!!!!!!!
Updating FRU FPGA image...
FPGA image update complete.
All software images installed.
Switch#
Configuring One Switch Uplink for MACSEC
1. Notice I’m configuring GigabitEthernet 1/2 NOT TenGigabitEthernet 1/1, this is because I’m using 1Gb SFP’s, both interfaces are listed in the config! (This confused us for about twenty minutes). We are not using dot1x authentication, we are simply using a shared secret password (abc123). Note: This has to be a hexedecimal password i.e numbers 0-9 and letters a-f.
Switch(config)#interface GigabitEthernet 1/2 Switch(config-if)#cts man % Enabling macsec on Gi1/2 (may take a few seconds)... Switch(config-if-cts-manual)#no propagate sgt Switch(config-if-cts-manual)#sap pmk abc123 mode-list gcm-encrypt Switch(config-if-cts-manual)#no shut Switch(config-if)# Mar 30 01:59:03.800: %CTS-6-PORT_UNAUTHORIZED: Port unauthorized for int(Gi1/2) Mar 30 01:59:04.799: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthe rnet1/2, changed state to down Mar 30 01:59:05.805: %LINK-3-UPDOWN: Interface GigabitEthernet1/2, changed state to down Mar 30 01:59:08.339: %LINK-3-UPDOWN: Interface GigabitEthernet1/2, changed state to up Mar 30 01:59:09.329: %CTS-6-PORT_UNAUTHORIZED: Port unauthorized for int(Gi1/2) Mar 30 01:59:10.016: %CTS-6-PORT_AUTHORIZED_SUCCESS: Port authorized for int(Gi1/2) Mar 30 01:59:11.023: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthe rnet1/2, changed state to up
Configuring A Port-Channel Switch Uplink for MACSEC
1. Configure MACSEC on both physical interfaces, before you ‘port-channel’ them. The second interface (when using 1GB SFP’s), is GigabitEthernet 1/4.
! interface Port-channel1 switchport trunk encapsulation dot1q switchport mode trunk ! ! interface GigabitEthernet1/2 switchport trunk encapsulation dot1q switchport mode trunk cts manual no propagate sgt sap pmk abc123 mode-list gcm-encrypt channel-group 1 mode on ! interface GigabitEthernet1/4 switchport trunk encapsulation dot1q switchport mode trunk cts manual no propagate sgt sap pmk abc123 mode-list gcm-encrypt channel-group 1 mode on !
Related Articles, References, Credits, or External Links
Thanks to Steve (www.linevty.com) for doing 97% of the hard work, whilst being slowed down by my ‘help’.