KB ID 0000922
Problem
I’m very disappointed with HP, theres next to no information on how to do this. My plan was to secure wireless access with certificates, so only clients with a valid digital certificate could authenticate and connect to the wireless. After spending nearly a whole day on the phone to various technical support departments at HP, this remained an impossible requirement!
In the end, as the client only had a few laptops for wireless access, we had to set NPS to allow access to domain users, then filter the devices that were allowed on the MSM controller via MAC address.
Solution
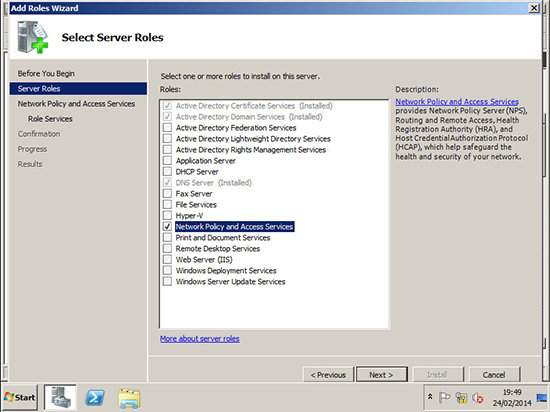
1. Launch Server Manager (Servermanager.msc) Roles > Add Roles > Network Policy and Access Services > Next.
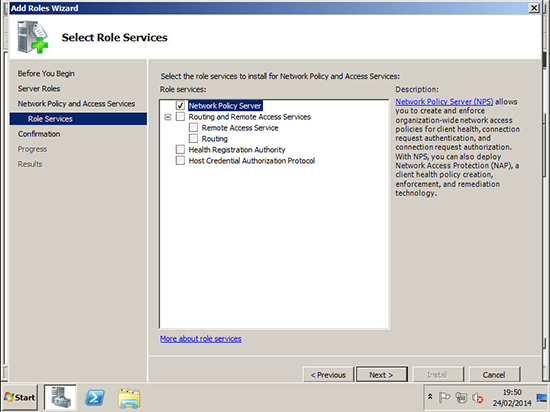
2. Accept the defaults, but on the Role Services page select ‘Network Policy Server’.
3. Expand Network Policy and Access Services > Right click NPS (Local) > Register in Active Directory > Accept the defaults.
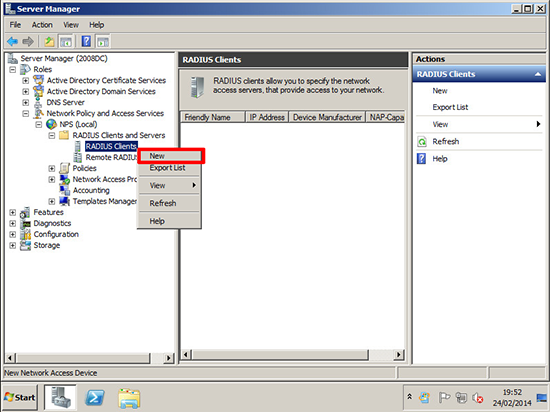
4. Expand RADIUS Client and Servers > RADIUS Clients > New.
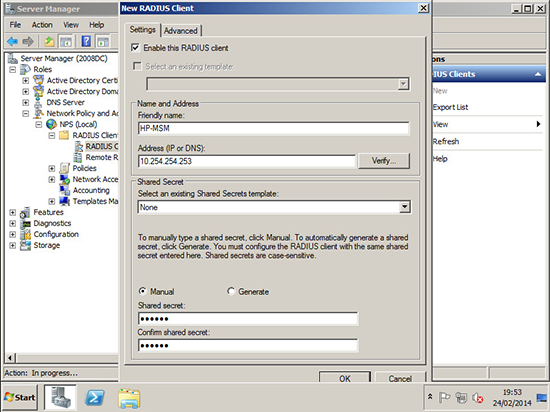
5. Specify a name > The IP address of the MSM controller > type in a shared secret and confirm it (this can be anything but remember it, as you need to enter it on the controller later > OK.
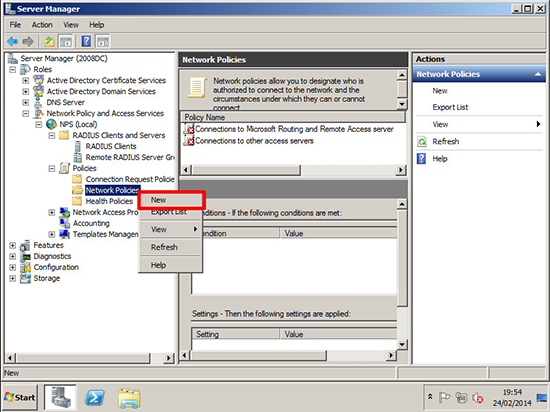
6. Expand Policies > Network Policies > New.
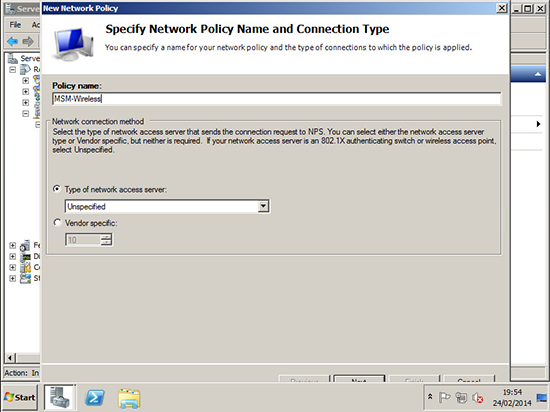
7. Give it a name > Next.
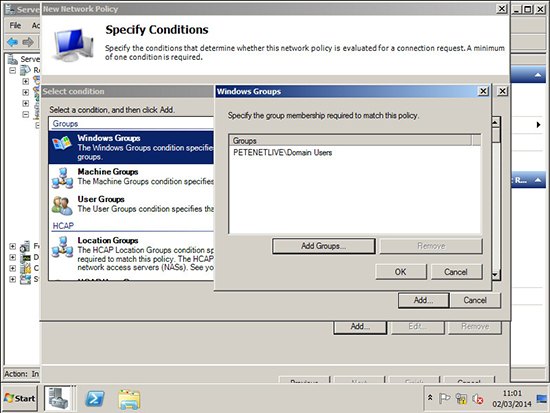
8. Add in Windows Groups and select the user group you wish to grant access to > OK > Add > Next.
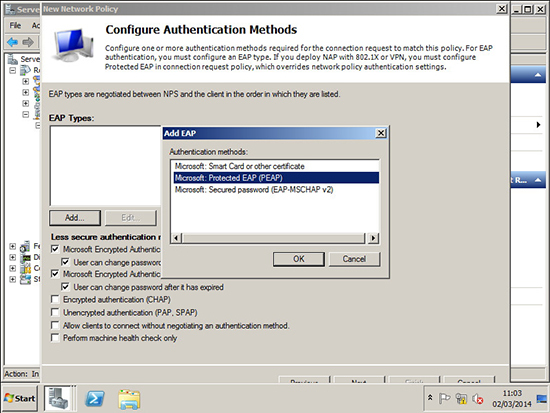
9. Add in ‘Microsoft Protected EAP (PEAP)’ > OK > Next.
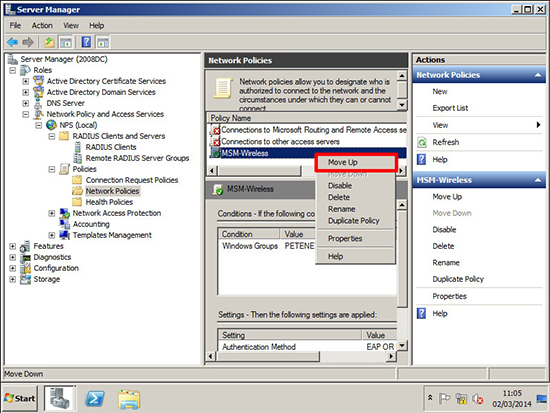
10. Move your newly created policy to the top.
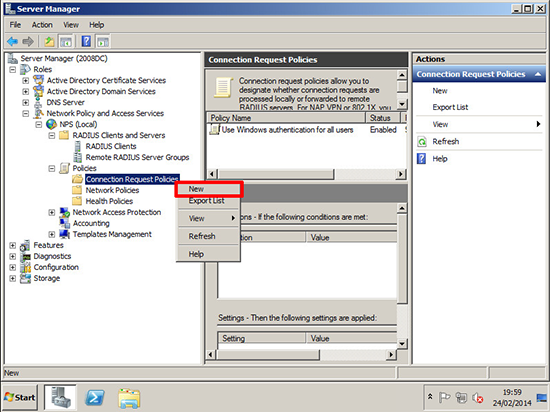
11. Now create a new ‘Connection Request Policy’.
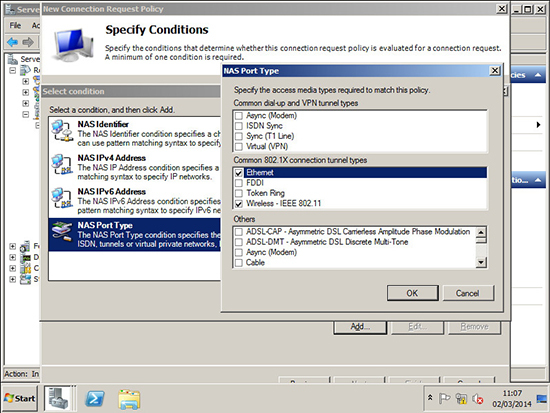
12. Add in NAS Port Type > Select Ethernet and Wireless – IEEE 802.11 > OK > Next.
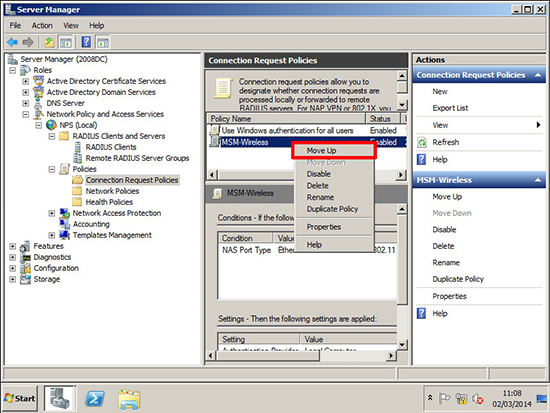
13. Move your new policy to the top.
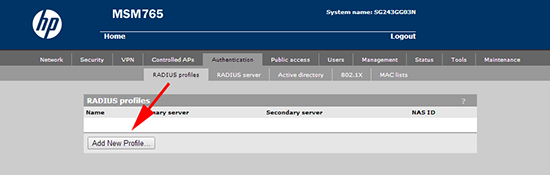
14. Log into the MSM > Home > Authentication > RADIUS Profiles > Add New Profile.
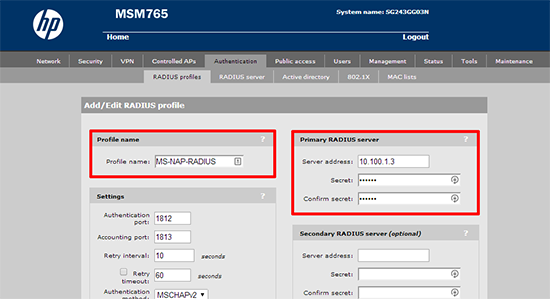
15. Give the policy a name > Enter the IP address of the NPS server > Then type in the shared secret, (you created in step 5.) > Save.
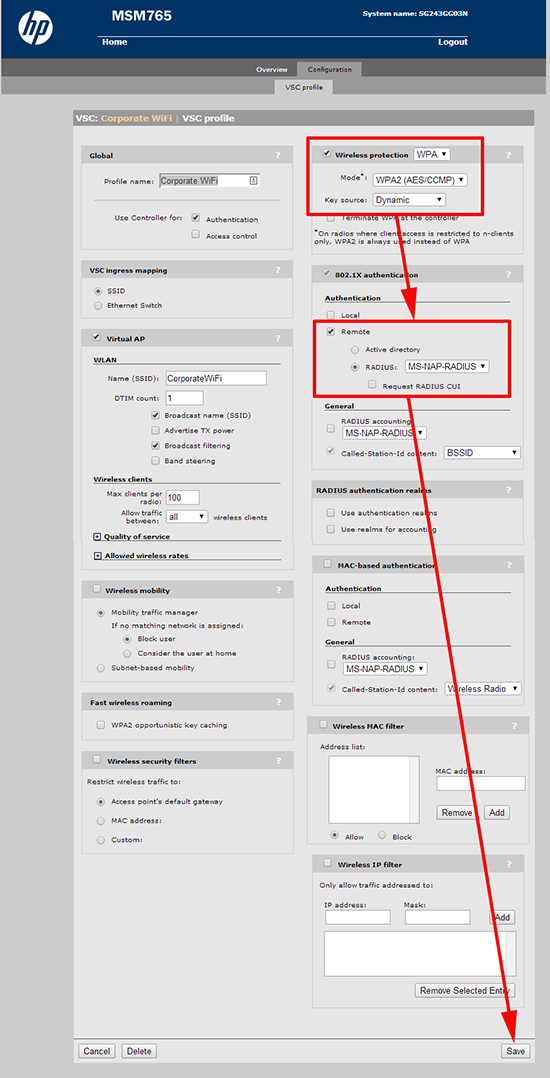
16. On the VSC for the wireless network you want to enable RADIUS for > Set Wireless protection to WPA > Mode to WPA2 (AES/CCMP) > Key source to Dynamic > Your RADIUS profile should be added automatically > Save.
Related Articles, References, Credits, or External Links
NA