KB ID 0000641
Problem
Microsoft disabled the local administrators account for a good reason, (its GUID it always the same, and its a well known attack vector into Windows). That said, if you have a problem on the domain, and you want to get into a client machine directly, not having the local admin enabled can be a pain.
Note: If you deploy your machines via WDS you can add a local admin account (with a different name) to your deployed machines see,
Windows Deployment Services (On Server 2008 R2)
Solution
1. On a domain controller Start > Administrative Tools > Group Policy Management Console.
2. Navigate to where you want to create your policy, or edit an existing one.
Note: You CAN apply this policy to domain controllers and the domain admin account will be unaffected. So you CAN set in the default domain policy if you wish. I prefer to create separate policies for things though, as it makes settings easier to find.
Enabling the Local Administrator via Group Policy
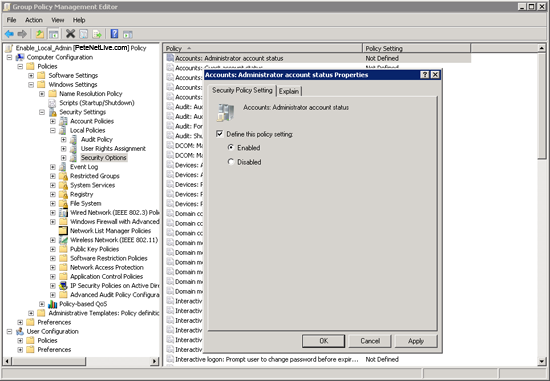
3. Navigate to;
Locate the “Account: Administrator account status Properties”, define and enable the policy.
Set the local Administrators Password via Group Policy
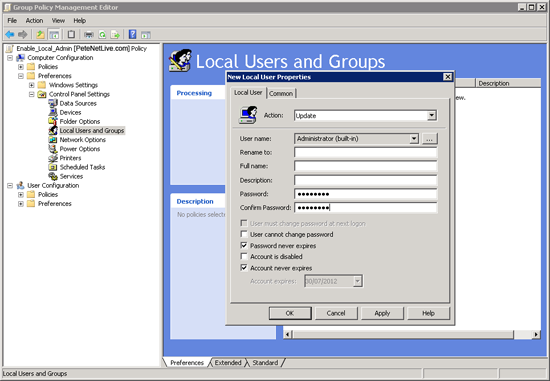
4. You need to do this with a group policy preference, but you can do this in the same policy, navigate to;
Right click > New > Local User > In the ‘User name’ section change the drop down to Administrator (built-in) > Set the password > Un-tick ‘User must change password at next logon’ > Tick ‘Password never expires’ > Apply > OK > Exit the policy editor.
5. Then either reboot the clients, wait a couple of hours, or manually run “gpupdate /force” on them.
Related Articles, References, Credits, or External Links
NA