KB ID 0000055
Problem
Cisco NetFlow lets you export information about traffic flow, it was originally written for the router IOS, but is now available for Cisco ASA, which uses NSEL (Note ASA uses NetFlow version 9 {newest at time of writing})
Note: NetFlow can not give you “Live” data, but it can show you what has happened over a period of time, and remember like any other “Logging” this will have an adverse affect on the firewall (depending on how busy it is).
Setting this up is a two step process, the firewall is configured as the NetFlow “Exporter”, then you install an application that accepts and collates that information, that is the NetFlow “Collector”.
Solution
1. Log into your firewall via CLI and enter enable mode, then enter configure terminal mode.
User Access Verification Password:******** Type help or '?' for a list of available commands. PetesASA> enable Password: ******** PetesASA# conf t PetesASA(config)#
1. We haven’t set one up yet, but we need to let the firewall know the IP address that the NetFlow “Collector” will be running on, in this case I’m going to use 10.254.254.253. (Note: the port number on the end is unimportant).
PetesASA(config)#
PetesASA(config)# flow-export destination inside 10.254.254.234 2055
PetesASA(config)#
2. The next command aggregates multiple events into separate NSELs on a 15 second interval.
PetesASA(config)#
PetesASA(config)# flow-export delay flow-create 15
PetesASA(config)#
3. Now we are going to set the refresh rate at which the templates are sent, if you do not do this it will default to 30 minutes.
PetesASA(config)#
PetesASA(config)# flow-export template timeout-rate 1
PetesASA(config)#
4. I’m going to apply this with the default global-policy, because most of you will have one, (Though I notice every 8.2(1) 5505 I’ve put in recently does NOT have one so check).
PetesASA(config)# policy-map global_policy PetesASA(config-pmap)# class class-default PetesASA(config-pmap-c)# flow-export event-type all destination 10.254.254.234 PetesASA(config-pmap-c)# exit
6. If you haven’t got a global policy, this will not apply until you have applied the global_policy globally, this is done with a service-policy command, check to see if you already have this command in your config, or simply execute the command and the firewall and will tell you, like so….
Note: If it does not error then it was NOT applied 🙂
PetesASA(config)#
PetesASA(config)# service-policy global_policy global
WARNING: Policy map global_policy is already configured as a service policy
PetesASA(config)#
7. Don’t forget the save the config with a “write mem” command.
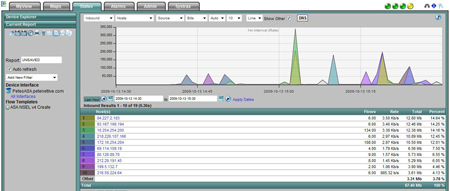
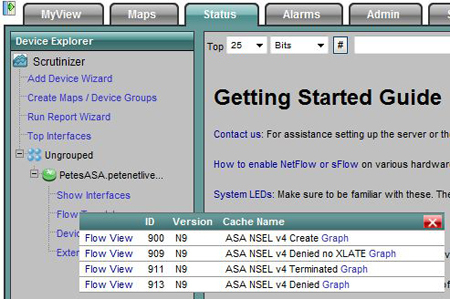
8. Now go to the machine you want to install your NetFlow collector software on, I prefer Plixer Scrutinizer because its free and its easy to set up. Connect to it via the built in web site (username admin password admin) > Click Status > Expand Ungrouped > Expand the firewall > Flow templates > Pick one.
9. There’s your throughput 🙂
Related Articles, References, Credits, or External Links
NA