KB ID 0000933
Problem
I’ve done thousands of firewall VPN’s but not many that terminate on Cisco Routers. It’s been a few years since I did one, and then I think I was a wuss and used the SDM. So when I was asked to do one last week thankfully I had the configs ready to go.
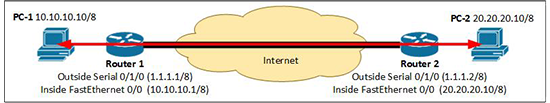
I’m going to use the IP addresses above, and my tunnel will use the following settings;
- Encryption: AES.
- Hashing: SHA.
- Diffie Hellman: Group 2.
- PFS: Enabled.
- Authentication method: Pre-Shared Key.
Solution
1. Setup a policy for phase 1 of the tunnel (ISAKMP).
R1>enable R1#configure terminal Enter configuration commands, one per line. End with CNTL/Z. R1(config)#crypto isakmp policy 1 R1(config-isakmp)#encr aes R1(config-isakmp)#hash sha R1(config-isakmp)#authentication pre-share R1(config-isakmp)#group 2 R1(config-isakmp)#lifetime 86400 R1(config-isakmp)#crypto isakmp key SecretK3y address 1.1.1.2
2. Setup an ACL to define what traffic will be encrypted, and a ‘Transform set’ that will dictate the encryption and hashing for phase 2 (IPSEC).
R1(config)#ip access-list extended VPN-ACL R1(config-ext-nacl)#permit ip 10.10.10.0 0.0.0.255 20.20.20.0 0.0.0.255 R1(config-ext-nacl)#crypto ipsec transform-set VPN-TS esp-aes esp-sha-hmac
3. Create a ‘Crypto map’ that is used to apply the phase 2 settings to an interface.
R1(config)#crypto map VPN-C-MAP 10 ipsec-isakmp % NOTE: This new crypto map will remain disabled until a peer and a valid access list have been configured. R1(config-crypto-map)#set peer 1.1.1.2 R1(config-crypto-map)#set transform-set VPN-TS R1(config-crypto-map)#match address VPN-ACL
4. Apply that crypto map to an interface, (usually the Internet facing one).
R1(config-crypto-map)#interface Serial0/1/0 R1(config-if)#crypto map VPN-C-MAP *Jan 3 07:16:26.785: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON R1(config-if)#exit R1(config)#
5. In most cases your router will be doing NAT, if so you will need to change the ACL that is looking after the NAT for you, look in your running config for something that looks like the following;
R1#show run
Building configuration...
Current configuration : 1249 bytes
------------output removed for the sake of space------------
!
ip nat inside source list 100 interface Serial0/1/0 overload
!
access-list 100 permit ip 10.10.10.0 0.0.0.255 any
!
------------output removed for the sake of space------------
!
line aux 0
!
6. To stop our VPN traffic getting NATTED, we need to put a deny in that ACL, and put it before that permit statement. Remember:
- Permit=Perform NAT
- Deny=Don’t perform NAT
On this router (unlike the ASA‘s that I’m more used to), there is no option to define an ACL line number. So its easier to remove the existing one, add the new line then put the original one back. Finally save the changes.
R1#configure terminal Enter configuration commands, one per line. End with CNTL/Z. R1(config)#no access-list 100 permit ip 10.10.10.0 0.0.0.255 any R1(config)#access-list 100 deny ip 10.10.10.0 0.0.0.255 20.20.20.0 0.0.0.255 R1(config)#access-list 100 permit ip 10.10.10.0 0.0.0.255 any R1(config)#exit R1# %SYS-5-CONFIG_I: Configured from console by console R1#write mem Building configuration... [OK]
7. Now at the other site, the config should be a mirror image. I will post it in its entirety, so you can copy and paste it into the router, I will highlight the bits you need to check and change in red.
crypto isakmp policy 1 encr aes hash sha authentication pre-share group 2 lifetime 86400 crypto isakmp key SecretK3y address 1.1.1.1 ip access-list extended VPN-ACL permit ip 20.20.20.0 0.0.0.255 10.10.10.0 0.0.0.255 crypto ipsec transform-set VPN-TS esp-aes esp-sha-hmac crypto map VPN-C-MAP 10 ipsec-isakmp set peer 1.1.1.1 set transform-set VPN-TS match address VPN-ACL interface Serial0/1/0 crypto map VPN-C-MAP no access-list 100 permit ip 20.20.20.0 0.0.0.255 any access-list 100 deny ip 20.20.20.0 0.0.0.255 10.10.10.0 0.0.0.255 access-list 100 permit ip 10.10.10.0 0.0.0.255 any
8. Test your VPN with the following commands. Note: you need to send some traffic over the VPN before it will establish!
show crypto isakmp sa show crypto ipsec sa
WARNING: If you have an ACL applied to the routers outside interface, you will need to allow in the Peer IP, like so;
ip access-list extended outside-in permit esp host 1.1.1.1 any permit udp host 1.1.1.1 any eq isakmp permit udp host 1.1.1.1 any eq non500-isakmp
If you do not, the other end will fail Phase 1 with a WAIT_MSG_3 Error!
Related Articles, References, Credits, or External Links
NA
