KB ID 0001085
Problem
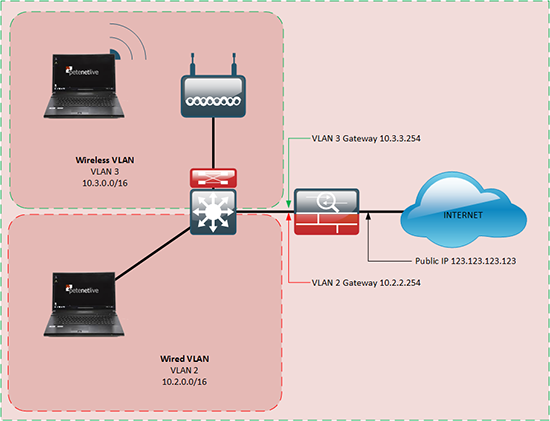
You can take the physical interface of a Cisco ASA firewall, (or an ether channel) and split it down into further sub-interfaces. This way you can set multiple VLANs to use this interface as a gateway at the same time whilst still separating the traffic.
In this scenario I’m going to have two VLANs, one for my wired clients, and one for a ‘Guest WiFi’ that I’m setting up. I want the guest WiFi to run in its own separate VLAN, so it can’t touch my corporate network. And I want to NAT both networks to my public IP.
Maximum number of sub interfaces, depends on the hardware model maximum number of VLANs so;
|
Model
|
Max VLANS
|
| 5506-X | 5 (30 with Security Plus) |
| 5506-W-X | 5 (30 with Security Plus) |
| 5506-H-X | 30 |
| 5508-X | 50 |
| 5510 | 50 (100 with Security Plus) |
| 5512-X | 10 (100 with Security Plus) |
| 5515-X | 100 |
| 5516-X | 100 |
| 5520 | 150 |
| 5525-X | 200 |
| 5540 | 200 |
| 5545-X | 300 |
| 5550 | 250 |
| 5555-X | 500 |
| 5580 | 250 |
| 5585-X | 1024 |
Note: Sub interfaces are NOT supported on the ASA 5505. (But you can have up to 20 VLANs with a ‘security-plus‘ licence, or 3 (DMZ restricted) with a ‘base‘ licence).
Solution
To create sub interfaces on a physical interface, that interface must have no settings on it (other than it should not be shutdown).
Petes-ASA # configure terminal Petes-ASA(config)# clear interface gigabitEthernet 1
Create Sub interface for VLAN 2 Petes-ASA(config)# interface gigabitEthernet 1.2 Petes-ASA(config-subif)# vlan 2 Petes-ASA(config-subif)# nameif Corp-LAN INFO: Security level for "Corp-LAN" set to 0 by default. Petes-ASA(config-subif)# security-level 100 Petes-ASA(config-subif)# ip address 10.2.2.254 255.255.0.0 Petes-ASA(config-subif)# exit Petes-ASA(config)# Create Sub interface for VLAN 3 Petes-ASA(config)# interface gigabitEthernet 1.3 Petes-ASA(config-subif)# vlan 3 Petes-ASA(config-subif)# nameif Corp-WiFi INFO: Security level for "Corp-Wifi” set to 0 by default. Petes-ASA(config-subif)# security-level 90 Petes-ASA(config-subif)# ip address 10.3.3.254 255.255.0.0 Petes-ASA(config-subif)# exit Petes-ASA(config)#
Note: I’ve manually set the security levels and made the corp-lan interface more trusted.
So my firewall config now looks like this;
! interface GigabitEthernet1 no nameif no security-level no ip address ! interface GigabitEthernet1.2 vlan 2 nameif Corp-LAN security-level 100 ip address 10.2.2.254 255.255.0.0 ! interface GigabitEthernet1.3 vlan 3 nameif Corp-WiFi security-level 90 ip address 10.3.3.254 255.255.0.0 !
NAT/PAT Traffic From Your Sub-Interfaces
Taking all traffic from both subnets (10.2.0.0/16 and 10.3.0.0/16), and I’m going to NAT both of these to my public IP. (Note: I’m actually going to PAT the addresses, but that’s just semantics).
Petes-ASA(config)# object network Corp-LAN-PAT Petes-ASA(config-network-object)# subnet 10.2.0.0 255.255.0.0 Petes-ASA(config-network-object)# nat (Corp-LAN,outside) dynamic interface Petes-ASA(config-network-object)# exit Petes-ASA(config)# object network Corp-Wifi Petes-ASA(config-network-object)# subnet 10.3.0.0 255.255.0.0 Petes-ASA(config-network-object)# nat (Corp-WiFi,outside) dynamic interface Petes-ASA(config-network-object)# exit
If you have ACLs you will need to allow the traffic out, and if you want to test connectivity by pinging a public IP address you will need to have ICMP inspection configured on the firewall.
What if you want the WiFi VLAN to have a different Public IP?
If you want to use another public IP from your public range, here is an example of the config;
<
! interface GigabitEthernet0 nameif outside security-level 0 ip address 123.123.123.123 255.255.255.0 ! interface GigabitEthernet1 no nameif no security-level no ip address ! interface GigabitEthernet1.2 vlan 2 nameif Corp-LAN security-level 100 ip address 10.2.2.254 255.255.0.0 ! interface GigabitEthernet1.3 vlan 3 nameif Corp-WiFi security-level 90 ip address 10.3.3.254 255.255.0.0 ! object network Corp-LAN-PAT subnet 10.2.0.0 255.255.0.0 nat (Corp-LAN,outside) dynamic interface ! object network Corp-Wifi subnet 10.3.0.0 255.255.0.0 nat (Corp-WiFi,outside) dynamic 123.123.123.124 ! route outside 0.0.0.0 0.0.0.0 123.123.123.124 !
OR, If you want the traffic to leave by another public interface (i.e. connected to another ISP) you can do the following;
! interface GigabitEthernet0 nameif outside security-level 0 ip address 123.123.123.123 255.255.255.0 ! interface GigabitEthernet1 no nameif no security-level no ip address ! interface GigabitEthernet1.2 vlan 2 nameif Corp-LAN security-level 100 ip address 10.2.2.254 255.255.0.0 ! interface GigabitEthernet1.3 vlan 3 nameif Corp-WiFi security-level 90 ip address 10.3.3.254 255.255.0.0 ! interface GigabitEthernet2 nameif outside-WiFi security-level 0 ip address 234.234.234.234 255.255.255.252 ! object network Corp-LAN-PAT subnet 10.2.0.0 255.255.0.0 nat (Corp-LAN,outside) dynamic interface ! object network Corp-Wifi subnet 10.3.0.0 255.255.0.0 nat (Corp-WiFi,outside-WiFi) dynamic interface ! route outside 0.0.0.0 0.0.0.0 123.123.123.124 route outside-wifi 0.0.0.0 0.0.0.0 234.234.234.235 !
Setting Up The Switch
This will depend upon the vendor, but essentially if it’s a Cisco Switch you make the uplink switch port a ‘trunk-port’, and either allow ALL or VLAN 2 and 3. Then every wired connection will connect to a port you have setup as a ‘access-port’ on VLAN 2. All the wireless equipment will plug into ports that you have made ‘access-ports’ on VLAN 3.
For other vendors you would need to ‘tag’ VLANs 2 and 3 onto the firewall uplink port. Then ‘untag’ VLAN 2 on all the wired ports. Then finally ‘untag‘ VLAN 3 on all the wireless ports.
See the following article for more information;
HP and Cisco – VLANs and Trunks Confusion!
Related Articles, References, Credits, or External Links
NA