KB ID 0000954
Problem
A while back I uploaded a run through on how to deploy GRE tunnels and protect those tunnels with IPsec. That point-to-point GRE tunnel is a good solution, but if you have a lot of sites it’s not a solution that scales very well. Yes you can have 2147483647 tunnel interfaces, but good luck manually configuring all those tunnels and even if you did, if you want each of your remote sites to talk to each other you have all those tunnels to configure as well.
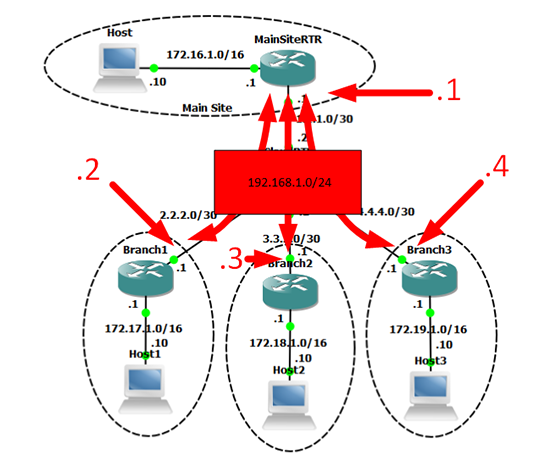
To address that we have DMVPN, rather than a point-to-point GRE tunnel it uses multipoint GRE that can have more than two endpoints. In fact it acts like a ‘network overlay’ that joins all the sites together. It is typically deployed in a hub-and-spoke configuration where one router (the hub) sits at the center and each remote site (spoke) joins the multipoint GRE, tunnels back to the hub. The magic part is, if one spoke needs to speak to another spoke, this is done by building a dynamic tunnel between them ‘on the fly’.
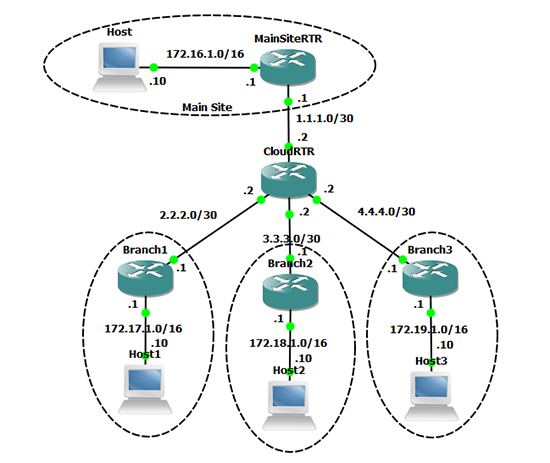
Below is the the network topology I’m going to use;
Note: If you use GNS3 heres the topology and configs for all the routers.
I have a main site that will be the ‘Hub Site’ and at that site MainSiteRTR will be the NHS router. The remaining three hub sites will act as ‘spokes’, so my ‘network overlay’ will be 192.168.1.0/24.
Solution
Configure DMVPN Hub (NHS) Router
Before I start, all the sites are pre-configured as per figure1 above, all the routers can see each other via EIGRP.
1. To begin the setup looks very much like a standard GRE tunnel, but we define a source but no destination (we don’t need to, because we specify tunnel mode gre multipoint). There are two commands for the NHRP setup, ‘ip nhrp map multicast dynamic‘ lets EIGRP information propagate to the ‘spokes’. And ‘ip nhrp network-id 1’ creates a group ID for the DMVPN group. All the spokes will need to share this ID to form tunnels with this NHS Router.<.p>
MainSiteRTR#configure terminal Enter configuration commands, one per line. End with CNTL/Z. MainSiteRTR(config)#interface Tunnel0 MainSiteRTR(config-if)# ip address 192.168.0.1 255.255.255.0 MainSiteRTR(config-if)# ip nhrp map multicast dynamic MainSiteRTR(config-if)# ip nhrp network-id 1 MainSiteRTR(config-if)# tunnel source 1.1.1.1 MainSiteRTR(config-if)# tunnel mode gre multipoint *Mar 1 00:02:31.651: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to down MainSiteRTR(config-if)#exit *Mar 1 00:02:41.635: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up MainSiteRTR(config)#
Configure the Branch ‘Spoke’ Routers
2. There are a few differences here, first ‘ip nhrp map 192.168.0.1 1.1.1.1’ tells the branch router to map the 192.168.0.2 private IP permanently to the 1.1.1.1 public address. ‘ip nhrp map multicast 1.1.1.1’ tells the router to relay ALL its multicast traffic back to the hub router. ‘ip nhrp nhs 192.168.0.1’ tells the spoke router where the hub router is.
Branch1#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch1(config)#interface Tunnel0 Branch1(config-if)# ip address 192.168.0.2 255.255.255.0 Branch1(config-if)# ip nhrp map 192.168.0.1 1.1.1.1 Branch1(config-if)# ip nhrp map multicast 1.1.1.1 Branch1(config-if)# ip nhrp network-id 1 Branch1(config-if)# ip nhrp nhs 192.168.0.1 Branch1(config-if)# tunnel source 2.2.2.1 Branch1(config-if)# tunnel mode gre multipoint *Mar 1 00:07:28.403: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to down Branch1(config-if)#exit *Mar 1 00:07:38.387: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up Branch1(config)#
3. Then configure each branch router the same, (apart from the tunnel source and the endpoint IP).
Branch 2 Router Config Branch2#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch2(config)#interface Tunnel0 Branch2(config-if)# ip address 192.168.0.3 255.255.255.0 Branch2(config-if)# ip nhrp map 192.168.0.1 1.1.1.1 Branch2(config-if)# ip nhrp map multicast 1.1.1.1 Branch2(config-if)# ip nhrp network-id 1 Branch2(config-if)# ip nhrp nhs 192.168.0.1 Branch2(config-if)# tunnel source 3.3.3.1 Branch2(config-if)# tunnel mode gre multipoint Branch2(config-if)# exit *Mar 1 00:09:32.631: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up Branch2(config)# Branch 3 Router Config Branch3#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch3(config)#interface Tunnel0 Branch3(config-if)# ip address 192.168.0.4 255.255.255.0 Branch3(config-if)# ip nhrp map 192.168.0.1 1.1.1.1 Branch3(config-if)# ip nhrp map multicast 1.1.1.1 Branch3(config-if)# ip nhrp network-id 1 Branch3(config-if)# ip nhrp nhs 192.168.0.1 Branch3(config-if)# tunnel source 4.4.4.1 Branch3(config-if)# tunnel mode gre multipoint Branch3(config-if)# exit *Mar 1 00:11:05.259: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to down Branch3(config)# *Mar 1 00:11:15.247: %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up Branch3(config)#
Verifying and Testing the DMVPN Setup
4. On the main site;
MainSiteRTR#show dmvpn
Legend: Attrb --> S - Static, D - Dynamic, I - Incompletea
N - NATed, L - Local, X - No Socket
# Ent --> Number of NHRP entries with same NBMA peer
Tunnel0, Type:Hub, NHRP Peers:3,
# Ent Peer NBMA Addr Peer Tunnel Add State UpDn Tm Attrb
----- --------------- --------------- ----- -------- -----
1 2.2.2.1 192.168.0.2 UP never D
1 3.3.3.1 192.168.0.3 UP never D
1 4.4.4.1 192.168.0.4 UP never D5. On a branch site (Note: There is only one tunnel to the Main Site);
Branch1#show dmvpn
Legend: Attrb --> S - Static, D - Dynamic, I - Incompletea
N - NATed, L - Local, X - No Socket
# Ent --> Number of NHRP entries with same NBMA peer
Tunnel0, Type:Spoke, NHRP Peers:1,
# Ent Peer NBMA Addr Peer Tunnel Add State UpDn Tm Attrb
----- --------------- --------------- ----- -------- -----
1 1.1.1.1 192.168.0.1 UP 00:08:24 S6. But if from the same branch site you ping another branch site, it will dynamically build a tunnel to that site also. (Note: The S denotes static, and the D denotes dynamic).
Branch1#ping 192.168.0.4
Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.0.4, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 32/60/108 ms
Branch1#show dmvpn
Legend: Attrb --> S - Static, D - Dynamic, I - Incompletea
N - NATed, L - Local, X - No Socket
# Ent --> Number of NHRP entries with same NBMA peer
Tunnel0, Type:Spoke, NHRP Peers:2,
# Ent Peer NBMA Addr Peer Tunnel Add State UpDn Tm Attrb
----- --------------- --------------- ----- -------- -----
1 1.1.1.1 192.168.0.1 UP 00:08:52 S
1 4.4.4.1 192.168.0.4 UP never DProtect and Encrypt the Tunnel(s) with IPSEC
7. BE AWARE the traffic traveling over these tunnels is still being sent in cleartext, it’s simply been ‘encapsulated’ with GRE. To rectify that we can protect the tunnels with IPSEC.
MainSiteRTR#configure terminal Enter configuration commands, one per line. End with CNTL/Z. MainSiteRTR(config)#crypto isakmp policy 10 MainSiteRTR(config-isakmp)# authentication pre-share MainSiteRTR(config-isakmp)# encryption aes MainSiteRTR(config-isakmp)# group 2 MainSiteRTR(config-isakmp)# hash sha MainSiteRTR(config-isakmp)# crypto isakmp key Sh@reds3cret address 2.2.2.1 MainSiteRTR(config)# crypto isakmp key Sh@reds3cret address 3.3.3.1 MainSiteRTR(config)# crypto isakmp key Sh@reds3cret address 4.4.4.1 MainSiteRTR(config)# crypto ipsec transform-set TFS-PNL esp-aes esp-sha-hmac MainSiteRTR(cfg-crypto-trans)# crypto ipsec profile PF-PNL MainSiteRTR(ipsec-profile)# set transform-set TFS-PNL MainSiteRTR(ipsec-profile)# interface Tunnel0 MainSiteRTR(config-if)# tunnel protection ipsec profile PF-PNL *Mar 1 00:25:34.055: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON MainSiteRTR(config-if)# exit MainSiteRTR(config)#
8. Then simply repeat on the branch routers, the only difference is the peer addresses.
Branch 1 Router Config Branch1#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch1(config)#crypto isakmp policy 10 Branch1(config-isakmp)# authentication pre-share Branch1(config-isakmp)# encryption aes Branch1(config-isakmp)# group 2 Branch1(config-isakmp)# hash sha Branch1(config-isakmp)#crypto isakmp key Sh@reds3cret address 1.1.1.1 Branch1(config)#crypto isakmp key Sh@reds3cret address 3.3.3.1 Branch1(config)#crypto isakmp key Sh@reds3cret address 4.4.4.1 Branch1(config)#crypto ipsec transform-set TFS-PNL esp-aes esp-sha-hmac Branch1(cfg-crypto-trans)#crypto ipsec profile PF-PNL Branch1(ipsec-profile)# set transform-set TFS-PNL Branch1(ipsec-profile)#interface Tunnel0 Branch1(config-if)# tunnel protection ipsec profile PF-PNL Branch1(config-if)#exit Branch1(config)# *Mar 1 00:36:47.179: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON Branch1(config)# Branch 2 Router Config Branch2#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch2(config)#crypto isakmp policy 10 Branch2(config-isakmp)# authentication pre-share Branch2(config-isakmp)# encryption aes Branch2(config-isakmp)# group 2 Branch2(config-isakmp)# hash sha Branch2(config-isakmp)#crypto isakmp key Sh@reds3cret address 1.1.1.1 Branch2(config)#crypto isakmp key Sh@reds3cret address 2.2.2.1 Branch2(config)#crypto isakmp key Sh@reds3cret address 4.4.4.1 Branch2(config)#crypto ipsec transform-set TFS-PNL esp-aes esp-sha-hmac Branch2(cfg-crypto-trans)#crypto ipsec profile PF-PNL Branch2(ipsec-profile)# set transform-set TFS-PNL Branch2(ipsec-profile)#interface Tunnel0 Branch2(config-if)# tunnel protection ipsec profile PF-PNL Branch2(config-if)#exit Branch2(config)# *Mar 1 00:37:57.239: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON Branch2(config)# Branch 3 Router Config Branch3#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Branch3(config)#crypto isakmp policy 10 Branch3(config-isakmp)# authentication pre-share Branch3(config-isakmp)# encryption aes Branch3(config-isakmp)# group 2 Branch3(config-isakmp)# hash sha Branch3(config-isakmp)#crypto isakmp key Sh@reds3cret address 1.1.1.1 Branch3(config)#crypto isakmp key Sh@reds3cret address 2.2.2.1 Branch3(config)#crypto isakmp key Sh@reds3cret address 3.3.3.1 Branch3(config)#crypto ipsec transform-set TFS-PNL esp-aes esp-sha-hmac Branch3(cfg-crypto-trans)#crypto ipsec profile PF-PNL Branch3(ipsec-profile)# set transform-set TFS-PNL Branch3(ipsec-profile)#interface Tunnel0 Branch3(config-if)# tunnel protection ipsec profile PF-PNL *Mar 1 00:39:10.515: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON Branch3(config-if)#exit
9. To test re-establish the tunnels, and this time you can see they are protected;
MainSiteRTR#show crypto isa sa
IPv4 Crypto ISAKMP SA dst src state conn-id slot status 1.1.1.1 3.3.3.1 QM_IDLE 1002 0 ACTIVE 1.1.1.1 4.4.4.1 QM_IDLE 1003 0 ACTIVE 1.1.1.1 2.2.2.1 QM_IDLE 1001 0 ACTIVE
Download the DMVPN labs and have a play
Related Articles, References, Credits, or External Links
Cisco Simple GRE Tunnels (With IPSEC)